Then to top it all off, if the story got out, customers would stop coming in fear of getting their card stolen. But when you incur a credit card breach like this, the credit card companies start getting into your business. When the Home Depot and Neiman Marcus were hit with their massive credit card breaches, those hackers were selling the dumps on 2pac.cc and getting 50% of the sales.
Top 5 Data Removal Services Of 2025
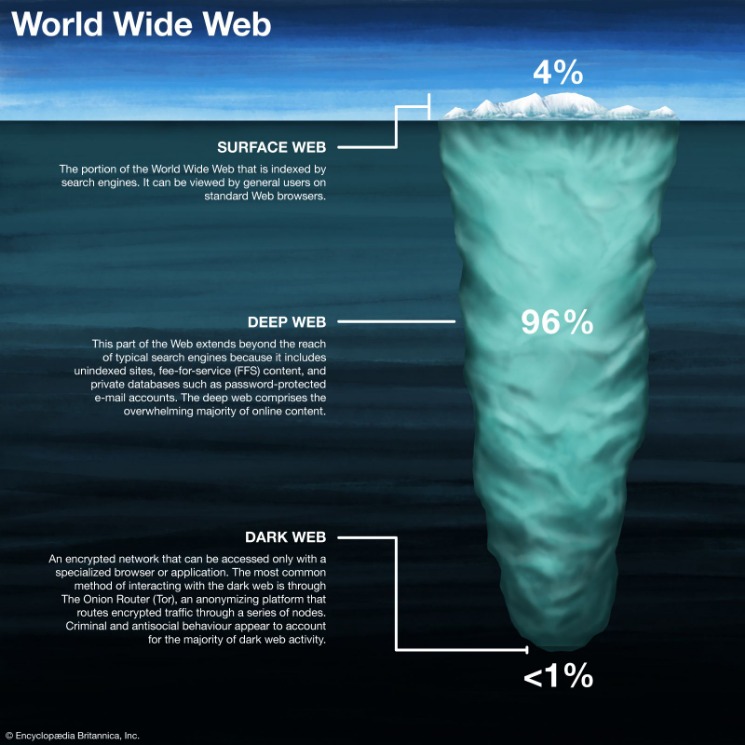
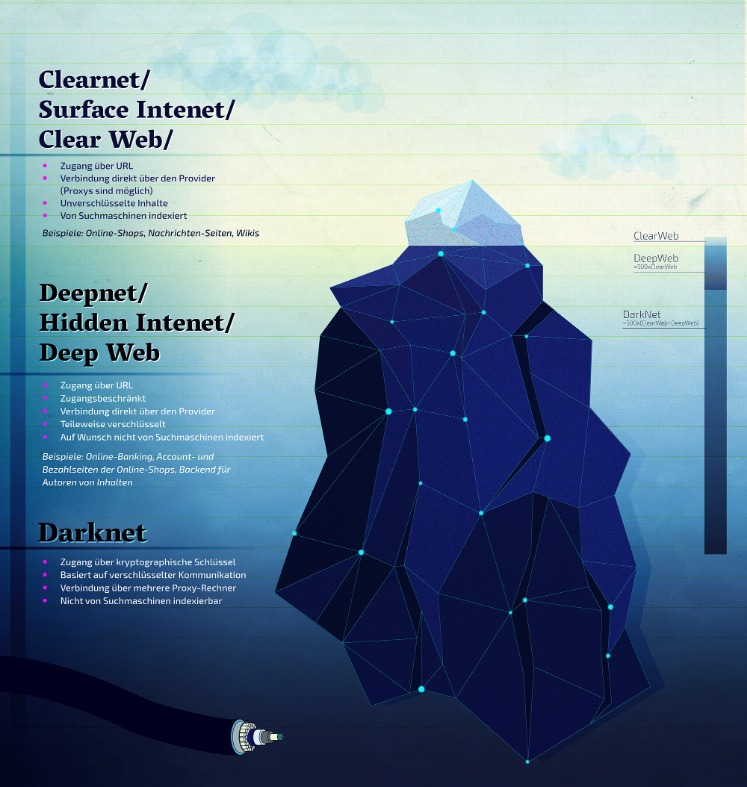
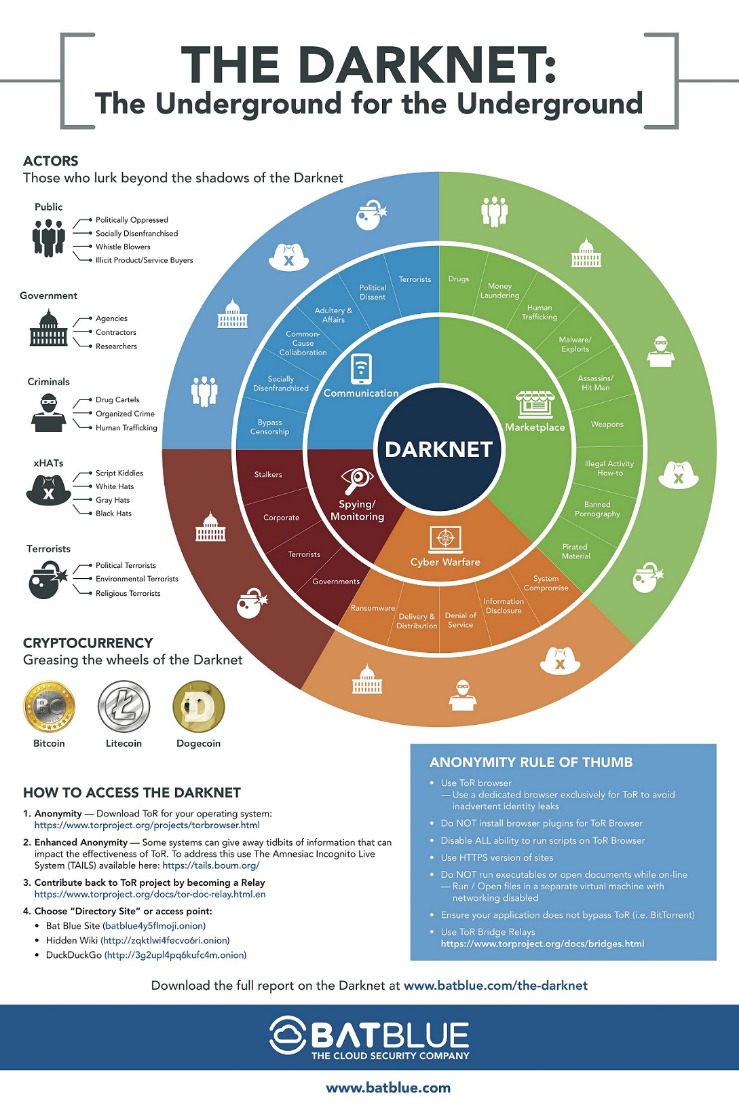
There are several whistleblower sites, including a dark web version of Wikileaks. That’s why we monitor your personal information and alert you if we spot new activity or changes. Make purchases with your debit card, and bank from almost anywhere by phone, tablet or computer and more than 15,000 ATMs and more than 4,700 branches. They may even make a driver’s license or medical insurance card using your information and then use the documents if they’re arrested or want to get a medical procedure. The sheer quantity of data available for purchase has created a bulk sales mentality for Dark Web customers. Legitimate users of the dark web include activists, or people who live under oppressive regimes, but they only account for a small percentage of the dark web.
- Some were taken down by law enforcement, others just vanished overnight with users’ money.
- Detective Dunn examined the PC and found credit cards were bought from two different websites, Bulba.cc and Track2.name.
- These sites are used for the buying and selling of stolen credit card information, as well as other forms of personal information such as Social Security numbers and driver’s license information.
- While it is not inherently malicious, the Dark Web has gained notoriety for being a breeding ground for cybercrime, enabling activities that range from illegal drug trading to hacking services and the sale of stolen data.
Get the latest updates on privacy, plus expert tips, and security guides to up your digital protection game. Prudence is the key to mitigating all online risks. But with the right preventive strategies, including real-time fraud detection, multi-layered authentication, and bot mitigation, organizations can reduce their exposure. Smaller businesses are often targeted because they may lack enterprise-level security infrastructure, making them easier to exploit. 3D Secure adds an extra layer of authentication, often requiring one-time passcodes or biometrics from the cardholder. This shadow economy supports a full-fledged cybercrime supply chain, from data theft to monetization, further complicating mitigation efforts.
Despite its name, the marketplace operates primarily in English and serves a global audience. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. Beginning in September 2021, Abacus Market has established itself as one of the leading dark web marketplaces. To expand their reach, some marketplaces established parallel channels on Telegram.
Warning For Would-Be Fraudsters

Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. Moreover, NordVPN is a service that doesn’t store or log your search results. Wondering what the best dark web VPN to use with Tor is for accessing the best onion sites on the dark web? If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web.
What Is Spyware? Definition, Types And Protection 2026
Some vendors even sell lists of "cardable" sites for a few dollars. Card data on the dark web is a valuable commodity, and it's often sold on specialized marketplaces known as Card Shops. The three suspects from Indonesia confessed to stealing payment card data using the GetBilling JS-sniffer family.
Anonymous Forums
When you first log into Bitdefender Central after activating your subscription, the service immediately starts mapping your digital footprint. Flare, for example, enables you to automatically scan the clear & dark web for any leaked or stolen account credentials. However, it also lingers all across the dark web to infect unsuspecting users just like it does on the rest of the web. It is often offered in some portals to give threat actors the tools for cyberattacks. This network anonymizes users by encrypting their connections and routing them through multiple nodes, making it challenging to trace back their identity or location. Freezing your credit reports with all three major credit bureaus―Experian, TransUnion and Equifax―can help keep someone else from opening an account in your name.
Verified Social Channels And News Sites
The detective monitored the site for the next few weeks to try to see how many cards were being bought in a week. Their cash registers were Windows computers running a credit card processing software. The detective started chatting with Track2 over ICQ to learn more and he found out that Track2.name was where untrusted customers go to buy stolen cards. The detective then started looking at these two carding websites, Bulba.cc and Track2.name.
Darknet carding sites are hidden online marketplaces that facilitate the buying and selling of stolen credit card information. Understanding the implications and risks of darknet carding sites can help users navigate the complexities of online security, ensuring better protection against potential threats. The most prominent claim is that large quantities of stolen card data circulate on the darknet, backed by a September 2025 report quantifying over six million compromised credit cards and noting specific national impacts such as thousands of affected Swiss citizens; this underscores a large, persistent supply-side problem for card fraud .
Dark Web Credit Card Fraud: Detecting And Preventing Credit Card Fraud
Individuals and businesses should take steps to protect their personal and financial information, such as using strong passwords, enabling two-factor authentication, and monitoring their credit reports for suspicious activity. Using a diffuse network of money mules, Zen Crew provides account opening services at various financial institutions (FIs) in the U.S., the UK and Canada. Telegram is separate from dark web forums, but it is worth also monitoring relevant illicit channels for a comprehensive cybersecurity posture.
Plus, it lets you set your location for local results, manage safe search filtering, and there’s even an AI “Assist” tool that provides AI search results — so you don’t have to visit web pages to find your answer. And I liked that if I visited a site that had a .onion version, it prompted me to switch to that version. DuckDuckGo is a search engine available on the Tor network that lets you browse the surface and dark web. You can also filter the results by telling Ahmia to only display links from the last day, week, or month. For example, I used the “radio” keyword and the third result was Deep Web Radio, which is a popular online radio station on the dark web. I tested it 10+ times, and it always provided me with accurate search results.
It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. This is high-level protection; no one can intercept your data or activities. It offers multiple security protocols, including OpenVPN UDP/TCP, L2TP/IPSec, and PPTP. This means that there will be no data to track your activities.
Threat Actor Profiles
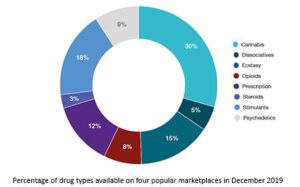
Listen to Nethone’s Intelligence Specialist Michał Barbaś as he explains the latest credit card dumps and how carding forums and markets work. In 2025, the landscape of darknet markets continues to evolve, offering users enhanced security, reliability, and accessibility for drug trade. The crackdown marks the second time in less than a month that the stolen credit card market has lost its top vendor site.

Never Share Personal Information
NordVPN analyzed statistical data gathered by independent researchers specializing in cybersecurity incident research from markets where payment card numbers are being sold. This includes stolen information and personal details leaked through data breaches such as credit card data, medical data, SSN, username and password combinations, home addresses, and many, many more details. The majority of users (over 90% as per our research) only need a Tor Browser for accessing .onion links; they don’t need to know about other methods.
We strongly recommend connecting to a VPN before you open any dark web links. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. Pastebins are text sharing services, useful for sending and sharing large snippets of code or text. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way.
Some focus purely on raw card data, while others specialize in “fullz” packages that include accompanying identity information. They sort cards by issuing bank, geography, and type, since platinum and high-limit cards command premium prices. After obtaining the data, sellers don’t just dump it on markets, they package it strategically. The Magecart group pioneered this technique, compromising thousands of online stores by exploiting vulnerabilities in popular e-commerce platforms. This type of malware silently infect payment terminals and exfiltrate card data in real-time. They’ve essentially created a parallel economy with its own reputation systems, escrow services, and even customer support channels.
The “massive collection of sensitive data containing over 1 million unique credit and debit cards,” was published to the criminal forum on Feb. 19 and contained six archives comprising a total of 1,018,014 cards. Darknet carding sites operate in a hidden part of the internet, accessible only through specific software like Tor. Those with a taste for entertainment can buy access to paid online subscription services. The Dark Web is a marketplace where criminals trade stolen financial data obtained via hacking or illegal activities such as phishing, skimming, and malware infections. In addition, Haystak offers a premium plan that allows deeper search, email alerts, and access to historical content.
Some of the best-known names include Abacus Market, Russian Market, and BriansClub, all with thousands of illegal items available.Despite closures by authorities or the typical “exit scams” (when a marketplace disappears with all the money), these sites continue to pop up. By monitoring the dark web, you can quickly identify when your cards are compromised through partner organizations or merchants. Monitoring these sites also helps track the effectiveness of security investments. I’ve seen cases where security teams identified compromised card data from their institution appearing on the dark web weeks before they traced the actual breach point. By monitoring dark web markets, we often discover data breaches before they’re publicly reported. The key is catching this activity before large volumes of card data make it to market.