Learn to identify and prevent CEO fraud scams with expert strategies from McAfee, your trusted guide in cybersecurity and fraud… Stay informed about new threats and protect your data with insights… That said, it’s still important to take as many precautions as you can to keep your family and your technology safe. The fact is, an everyday internet user like yourself likely won’t have any contact with this level of the internet.
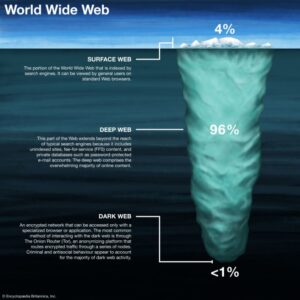
Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material.
Tips For Staying Safe On The Dark Web
It allows you to visit websites on the dark web. The Onion Project, or TOR is the predominant anonymous computer network. I do not condone the use of DNMs to purchase or sell drugs and other illegal materials online. The Tor browser offers strong online protection, given that it routes your online traffic via severa…
What Are Governments Doing To Combat Dark Net Threats?
- As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet.
- For Android mobile devices, the official Tor Browser application can be found and installed directly from the Google Play Store.
- Library Genesis offers a search engine for collections of books on such topics as computers, business, technology, and more.
- However, understanding how it works is crucial for appreciating the broader landscape of online privacy and security.
Being hidden doesn't translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk. You won't be able to access .onion addresses using a standard search engine as they aren't indexed by crawlers. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. The mobile app uses DuckDuckGo as its default search engine and is supported by the Orbit framework to provide secure access to the Tor network. VPNs are also used for accessing geo-locked content hosted by streaming services.
Dark Web Sites
The dark web, a subset of the deep web, cannot be accessed with a regular browser. To access these resources, you need to log in with a username and password using a traditional browser like Chrome or Safari. To reach Geekflare.com, you can either type its URL in your standard web browser or search for Geekflare in your favorite search engine. However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. We use this data for functional purposes, analytics, and personalized advertising (which may include sale or sharing of your personal information). Consenting to these technologies will allow us to process data such as your IP address and browsing behavior or unique IDs on this site.
A New Era: Social Media And AI Tools Challenge Google’s Long-Standing Reign
Another common method for finding onion services is through onion directories or link lists, which are essentially curated lists of .onion addresses categorized by topic. One of the significant challenges in navigating the dark web is discovering and accessing these onion services. When Tor Browser encounters an .onion address, it recognizes it as a request to connect to a hidden service within the Tor network and initiates the necessary routing and decryption processes. Older, shorter 16-character v2 .onion addresses were also used in the past, but these have been deprecated and are no longer supported by the current Tor network due to security vulnerabilities.
Get A Personalized Protection Plan Today
The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship. There are many different ways to access the dark web, but navigating it can be tricky and dangerous if you don’t know what you’re doing. This website allows you to type in your email address or phone number and see if it’s been compromised in any data breaches.
Tor Hidden Wiki 2024

Your internet activity is still subject to exit node risks, so always use HTTPS and avoid entering any personal information on unencrypted sites. That means your ISP only sees encrypted VPN traffic and can’t tell you’re using Tor. Don’t download anything unless you’re absolutely sure it’s safe.
Tor encrypts your traffic and routes it through multiple volunteer-operated relays, making it difficult to trace. But how does one safely and legally access the Dark Web? Changing the Windows setting affects system apps (like Calculator, Calendar, and Mail), but what about the rest of your software? To truly manage your environment, we recommend downloading “Auto Dark Mode” from the Microsoft Store.
- The trick with these onion websites is their accessibility, which is made possible only with the Tor Browser.
- The Tor Browser is a unique web browser designed specifically to provide users with privacy and anonymity online.
- It's a place where you'll find data leaks and illegal trades, but also legitimate, legal online activities users want to carry out without attracting the attention of law enforcement agencies or governments.
- It also adds a crucial layer of encryption before your traffic even enters the Tor network.
- All the websites and content that isn’t being shown on the “surface web” is generally referred to by many as the “deep web”, “dark web”, or “invisible web.”
- Either way, some sites take up to a minute or more to load, so don’t fret.
MANAGED SERVICES
We’ve clarified how to go on the dark web anonymously with the help of a VPN. Either way, some sites take up to a minute or more to load, so don’t fret. Copy the URL of the site you want to visit, press Enter, and you’re all set. If you’re prompted to connect, click the purple Connect button. Everything you do is protected by NordVPN, vital to accessing the dark web and enjoying it privately.


Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. If you want to buy something on the dark web, it’s a best practice to create a fake identity. Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users).
The Darknet Guide: Introduction
Engaging in any of these activities is a serious crime with severe consequences. However, what you do on the dark web can certainly be illegal. This makes it nearly impossible for anyone to trace your online activity back to you. Your traffic is then bounced through a series of volunteer-operated servers, known as nodes or relays.