It will offer you an additional layer of encryption to access the deep parts of the internet. You can also use it within the dark web, as it has .onion links. Though people usually think of dark websites as the wrong online place, that’s not the complete truth. Adam is a senior security analyst who specializes in deep-dive research and practical security guides. The dark web often feels like the Wild West of the internet, a realm of anonymity, intrigue, and lurking danger behind every corner.
Javascript (JS) is recommended for accessing the dark web sites. Chat with Strangers (dark web links for android) is a virtual chat room hosted in the Tor Browser that is randomized and anonymous. Now, in the search bar of the Tor, type or paste the .onion URL of the website that you want to visit and press “Enter”. The list is made keeping in mind to reduce your time wastage on scouring on the darkweb websites which you can easily visit taking reference from here. It's something built into the password management services offered by Apple and Google as well, so you don't need to trawl through data leaks manually yourself.
Is It Illegal To Visit Dark Web Websites?
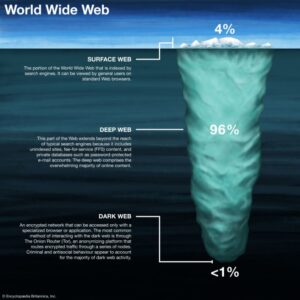
Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… Thus, staying connected to a VPN when you access these sites is vital. The deep web is not a series of sites but a storehouse of records, including email accounts, medical records, private messages, and more. The deep web represents a portion of the Internet you can’t access using a regular search engine. While they might sound the same, these websites are fundamentally different. If you need a listing of currently active websites, contact their support, and they will provide you with that.
- TorLinks maintains one of the most reliable directories of verified .onion sites.
- As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address.
- Check out these best onion sites to access the dark web securely and anonymously.
- NoScript and HTTPS Everywhere extensions provide additional protection against malicious scripts and unsecured connections.
- The service remains free to use, and the secure design prevents access to third parties, eavesdroppers, and other malicious agents.
- Whether you're just browsing onion links, looking for darknet market sites, or interested in educating yourself about the dark web, consider this the best place to look.
How Much Does It Cost To Use Tor Browser?
You can’t search for .onion sites using Google. These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. With Tor Browser, you are free to access sites your home network may have blocked.
These are verified media stories that you will not find on the surface web because of censorship, bans, and other restrictions. The site is strongly resistant to hackers and encrypts your data in transit as well as the rest. To contribute a tip, join the community, which can be done anonymously through an approved onion link.
Implement Strong Security Measures
Another good practice is to cross-reference links with multiple sources to confirm consistency. Because the Hidden Wiki aggregates many links, it often contains outdated or malicious URLs disguised as legitimate ones. Dark web sites linked through the Hidden Wiki offer forums for free speech, whistleblowing platforms, and uncensored news outlets that operate beyond the reach of traditional censorship mechanisms. Tor encrypts and routes internet traffic through multiple relays, masking the user’s IP address and online activity from trackers and surveillance. Lastly, consider using a trusted security tool or firewall on your device and stay informed about the latest dark web threats through reliable sources.

The BBC's international edition Tor version is available on the dark web, giving access to unbiased news in regions where the BBC is blocked or censored. The Dutch national police have made their onion site function as a billboard, warning all would-be criminals on darknet marketplaces to think twice about their actions. They offer user generated reviews of forums and darknet markets, alongside breaking stories and news from the Tor-sphere. It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web.

A typical onion link looks like a long, random string—something like abc123def456xyz.onion—and is often difficult to remember or search for. Instead, they’re accessed through the Tor Browser, which routes traffic through multiple layers of encrypted nodes to protect anonymity. The links are organized into categories such as general resources, marketplaces, and email services.
Can I Access The Dark Web On Mobile?
A VPN connection is key to gaining greater privacy, security, and freedom on and off the dark web. While the best dark web sites listed above are a good starting point for a safe, legal surfing experience on Tor, there really is no substitute for a VPN. Enable MFA wherever possible to protect your accounts from unauthorized access. This adds another, more reliable security layer to all of your online activity. A VPN like Surfshark encrypts your internet connection and makes it harder for others to see your real IP address. Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know.
Popular Dark Web Onion Links And Dark Web Sites On The Darknet Tor Network
All in all, it is not illegal to access the dark web, but it can create issues for you. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. At the same time, it is a breeding ground for malicious actors who want to do illegal activities. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
This .onion site is a bit different from the others reviewed above. The .onion site has thousands of downloadable comic books ranging from niche to mainstream. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. Your data is encrypted in the Tor browser before reaching the ZeroBin servers. ZeroBin is a wonderful way to share the content you get from dark web resources.
Why Is Certified Ethical Hacker (CEH V13 AI) So Popular
The site looks and functions like a normal page on the surface web, but encrypts connections to protect users’ identities. It’s popular among students, researchers, and independent scholars. Sci-Hub gives free access to millions of academic papers that are usually locked behind paywalls. Researchers and privacy advocates use it to study Tor usage and detect changes that might indicate censorship or surveillance attempts. It provides data on user numbers, relay performance, and traffic trends.
You're also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it's by no means completely safe. Even with Tor and onion routing in place though, you're not suddenly completely invisible and free to do whatever you want, without repercussions. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are.
Dark Web Links For News
I also like that the security guides are user-friendly — the format is easy to scan, complicated terms are explained very well, and there are videos and screenshots. This is a blog with cybersecurity tips created by the Electronic Frontier Foundation (EFF), a popular non-profit that specializes in digital privacy. It’s run by volunteers in the US and focuses on privacy, security, and supporting social justice. SecureDrop protects your privacy by encrypting your data, which makes it unreadable. SecureDrop is an open-source submission system that nonprofit organizations (NGOs), journalists, and news organizations can use to share and receive sensitive files securely. The Mail Plus plan adds up to 15 GB of storage, unlimited messages, and 10 email addresses, plus advanced email settings (like automatic forwarding).
ExtremeVPN is the best VPN choice for accessing tor sites. Malicious hackers may use phishing to steal your data, extort you, or access other sensitive materials such as intellectual property. In other situations, some sites will blatantly deter search engines from identifying their location. It can be accessed using typical browsers or search engines.
D List Of 12 Onion Websites
This technology makes it very difficult to track the identity or location of users. Tor Network, short for "The Onion Router", is a network consisting of volunteer servers that encrypt Internet traffic and route it through multiple nodes. These lists of goods include both legal and illegal goods. Unlike conventional domain names like .com or .org that are managed by a central authority, .onion addresses are not registered or purchased. This multi-layered process makes it incredibly difficult to trace the user's origin or the website's physical location, ensuring a high degree of privacy and security. When a user connects to an onion website, their request is wrapped in multiple layers of encryption, and this encrypted "onion" is then sent through a series of volunteer-operated servers, known as relays.