Using the ProtonMail .onion site offers security and privacy advantages. Furthermore, data will help to detect attacks against the network and possible censorship events. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web. Among them was a Paraguayan man they believe was the network’s ringleader. In the operation, police dismantled multiple pedophile chat sites, detaining four suspects.
Choose An Overlay Network
It’s a solid option if you’re not planning to access the dark web, but still want to keep a low profile while browsing. While it still occasionally connects to Mozilla to protect against malicious extensions, it doesn’t track you or collect your data. Although the company clarified that private browsing is still respected, some users were left uneasy. It hasn’t received many updates lately, which may raise concerns for some users. But if you’re serious about maximum privacy, it’s absolutely worth the effort. It can take a little while to load and it’s not as intuitive as other systems.
Reconnoitre – Open-Source Reconnaissance And Service Enumeration Tool

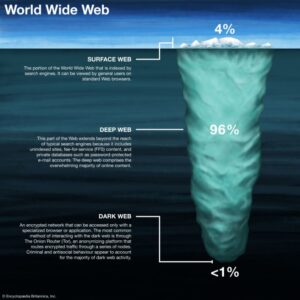
Content and services on the deep web are accessible through a regular browser. When you search a term (or query) in a web browser, the search engine combs through the database to find relevant results and serves them up on SERPs. Discovered pages are indexed in an extensive database and ranked based on numerous factors. The hidden web (also known as the deep web or deep net) is the largest part of the internet. The dark web is part of the deep web and is hosted on darknets and encrypted networks like Tor, Freenet and Riffle.
Illicit Substances
- As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
- All of the above is why I strongly recommend using the dark web not for access to iffy or outright illegal trading of goods and services, but instead to gain access to information you might normally be blocked from.
- This is pointless because VPN services are usually legal.
- The dark web is designed to protect private information, keeping sensitive data out of the public eye.
- The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet.
To do so, enter a .onion URL and you’ll be taken to the dark web page being served at that address. So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations. By using a VPN to connect to Tor — a special browser designed to access the dark web — you can securely access the dark web using a technique known as Tor-over-VPN. The editorial team did not participate in the creation of this guide.

WANT TO TRY THE TOP VPN RISK FREE?
You won't be able to access .onion addresses using a standard search engine as they aren't indexed by crawlers. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. The mobile app uses DuckDuckGo as its default search engine and is supported by the Orbit framework to provide secure access to the Tor network. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet.
What Is The Safest Way To Access The Dark Web?

That is why the explorers post their content on the dark web forums rather than the surface web. This .onion site is a bit different from the others reviewed above. The .onion site has thousands of downloadable comic books ranging from niche to mainstream. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. Your data is encrypted in the Tor browser before reaching the ZeroBin servers.
Tools Needed For Safe Access
While this might sound vast, it’s still a drop in the digital ocean of the estimated total of 5.35 billion internet users worldwide in 2024. Although some legal products may be available, their ‘bread and butter’ is the sale of illegal drugs and it’s common to find other prohibited items such as stolen data and weapons. The majority of it contains web pages which are not indexed and therefore not accessible by search engines but have a legitimate purpose and can be accessed if you know the relevant internet address.
It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources. Darknet markets facilitate transactions for illegal goods and services. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web.
Moreover, hackers who offer their services over the dark web have also targeted financial institutions and banks. The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group. Fraudulent activities on the dark web include phishing scams, fake identity sales, and the sale of fake products. Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information.
What Percentage Of The Internet Is Dark Web?
“On the deep web, you can assume that activities are monitored at the gateway. Mail providers Mailbox.org and Protonmail can also be accessed via an .onion link. Any internet traffic leaving the exit node is no longer part of Tor's dark web.
These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Last but not least, we here at Pixel Privacy never condone illegal activity. If you decide to enter the dark web, always make sure to take all the necessary online privacy precautions. Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails.
What Is Archetyp Market?
It blends performance, online privacy, and online protection into a single (free!) app. You’re better off on the surface web where the light of online regulations can still shine! And in some countries, a visitor will catch the attention of authorities by just downloading Tor. As an example, the URL for the popular commerce site Dream Market is in fact the catchy “eajwlvm3z2lcca76.onion”.