It is a peer-to-peer platform that encrypts the data before it is shared. Freenet uses a similar technique of routing the data through different nodes. There are four different layers of encryption; you can access the surface web and the deep web through the layered stream.
It’s extremely capable at hiding your IP address from traffic analysis or network surveillance. The deep web contains mostly benign websites that aren’t on the surface web where browsers like Google can find them. Law enforcement agencies monitor the dark web for stolen data and criminal activity, while major media organizations track whistleblowing sites for news. Many people in countries with surveillance or Internet censorship rely on the dark web browsers for secure communication.
How To Delete Search History On IPhone And IPad
Remember that activity within apps you’re logged into will be recorded, even if you’re using Tor. Orbot is free, open source, and can even replace your VPN, if you don't mind slower browsing speeds. It is worth noting that Private window with Tor isn’t as secure as using the Tor Browser itself. To access the dark net and Tor using Brave, open the browser, choose the hamburger icon from the top toolbar, and select Private window with Tor. Brave is easier to set up, though, and is already more privacy-oriented than most browsers. An I2P connection is slightly more secure than Tor but is also more difficult to set up.
You’re responsible for configuring your own anonymity solution. Freenet (renamed Hyphanet in mid-2023) is a peer-to-peer platform for censorship-resistant communication. Every device that connects strengthens the network.

I2P: Invisible Internet Project
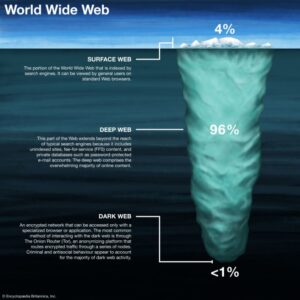
The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. The users only have access to a fraction of the available data and web pages.
OpenAI And Jony Ive Unveil Prototype For First Consumer Hardware Device
Hidden Wiki is a directory of the various dark web links, with detailed explanations of where each link takes you. It is very important to be careful what links you click online. For further anonymity, the service supports anonymous payment methods and lets you pay with cryptocurrency and cash.
What Kind Of Information Can I Find On Dark Web Search Engines?

Anyone who owns and operates the entry node will see your real IP address. Plus, Tor cannot protect against tracking at the entry and exit nodes of its network. Tor Browser is primarily used as a method of anonymous browsing. Though Tor is slower, the process of rerouting data through nodes makes it more difficult to trace your activity back to you. In addition, Tor and VPNs take different approaches to rerouting data. A key difference between Tor and a VPN is that a VPN’s network is operated by a central service provider, while the Tor network is decentralized and run by volunteers.
How Law Enforcement Tracks Tor Users
It can take a little while to load and it’s not as intuitive as other systems. Because enforcing copyright requires surveillance, and surveillance goes against the very foundation of free expression, which is what this network is built on. When you connect to Freenet, you become part of its network by sharing a bit of your bandwidth and disk space.
The Tor Project also offers the Tails operating system for users who prefer a complete privacy solution for accessing the dark web safely. When you use the Tor Browser, all your traffic will automatically travel through the Tor network, which comprises thousands of volunteer-run relays. It is the flagship product of the Tor Project (the company responsible for maintaining the Tor network). Whether exploring the hidden internet for curiosity or privacy, these are the best dark browsers. Our mission is to provide a reliable hub where individuals, businesses, and communities can access up-to-date information on a wide range of security topics. Subgraph OS is a Linux-based operating system designed for security, privacy, and dark web access.
- Many popular websites, such as Facebook and DuckDuckGo, have Onion versions, so check if yours has one.
- The dark web is a small encrypted portion of the internet requiring special browsers to access.
- Torch prioritizes online anonymity and offers uncensored and unfiltered search results.
- As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
- Tor Browser is safe to use if you’re browsing the same sites you would on the “clear web.” But if you browse .onion sites, use caution.
Can Tor Browser Be Used For Regular Internet Browsing?
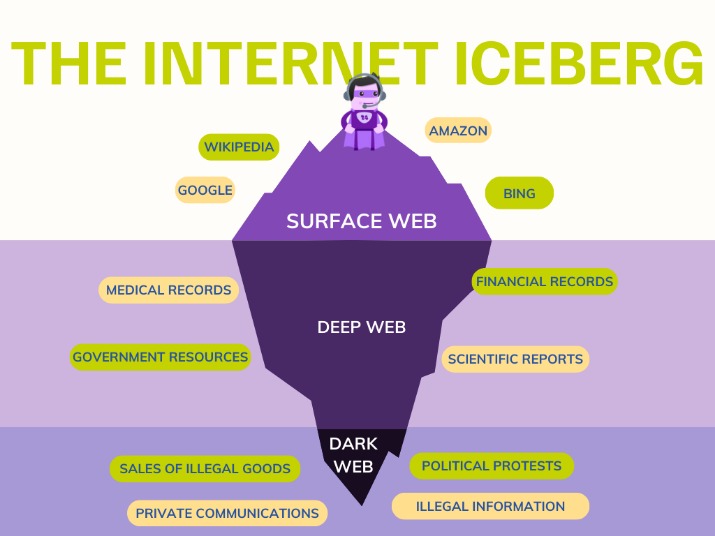
The deep web is every part of the internet that is not indexed by search engines, like private messages from your social media or your online banking portal. With the growing abilities of corporations to monitor and collect our data, the core principle upon which the dark web exists is now more relevant than ever. Although it requires more work, it provides tech-savvy users with a more familiar interface with better security for accessing Tor through a proxy. I2P’s most attractive angle is to access its own internal eepsites, which are its version of .onion sites. The tip above water is the “surface web.” That’s where you have those sites you find when you search Google. You are solely responsible for complying with your region’s laws that apply and for ensuring your anonymity and security online.
Is Accessing The Dark Web Illegal?
If so, it’s better to use the onion address instead of the standard one. We’ve demonstrated how to use Tor to access normal websites. For example, in Safer mode, JavaScript is turned off on non-HTTPS (insecure) sites, but in Safest mode, JavaScript is turned off entirely for all sites. Tor is a network designed to route traffic through multiple servers. It contains information like government private data, bank data, private networks, net-banking passwords, medical records, research papers, etc.
This privacy garlic browser is less well known than Tor, but it’s every bit as respected. The popular onion browser, Tor, is perhaps the most well-known privacy browser out there. Just remember, besides using one of these browsers, be sure to pair it with a good VPN service too.
Power BI Classes In Pune Learn Data Visualization From Experts – Bes
Many people see hacked information and stolen card data being sold on the dark web. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. An easy way to find content on the dark web is to receive a link from someone who already knows about it. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. As a result, you cannot find them with a regular search engine. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark web sites offer malware as a tool for cyberattacks. Accessing blocked content can result in being placed on a watch list or imprisonment. In fact, there are growing concerns about law enforcement monitoring what is happening on the dark web. Government authorities across the globe are taking over many Tor-based sites.
The Tor browser is a great way to surf the internet safely and privately. As a freelance content writer, Stefan can break down complex technological topics, making them easily digestible for the lay audience. You can use a secure email platform like ProtonMail or Tuta. For example, you can use Signal as your daily messaging app– it has end-to-end encryption and collects minimal data unlike many other messaging apps. Use encrypted communication platforms instead of the standard ones with less robust security features. Don’t open attachments from untrusted sources, as they are a common vector for spreading malware.