Software developers and security experts continuously work to identify and patch vulnerabilities, but the demand for these exploits remains high. The sale and use of exploits and zero-day vulnerabilities on the dark web contribute to the advancement of cybercrime and pose challenges to cybersecurity professionals. Cybercriminals can exploit these vulnerabilities to gain unauthorized access to networks, steal sensitive information, or carry out devastating cyber-attacks. The trade of exploits and zero-day vulnerabilities on the dark web poses significant threats to individuals, organizations, and even government entities.
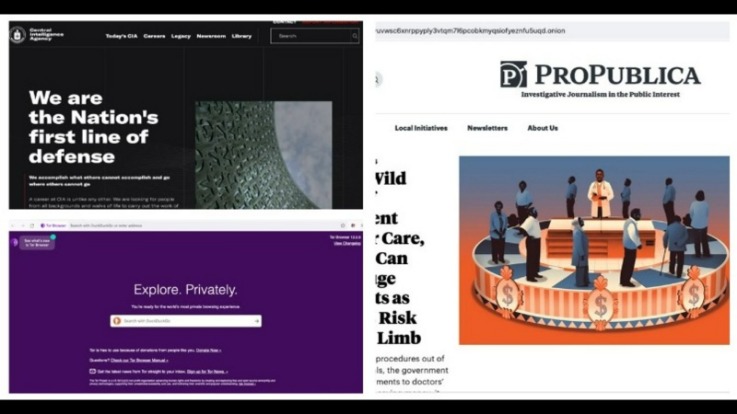
- Just visiting the dark web, or using a tool like Tor, isn’t illegal in most countries.
- Thoroughly checking credentials, contacting educational institutions for verification, and employing reputable credential verification services can help mitigate the risk of accepting fraudulent qualifications.
- Changing the Tor browser settings can further boost your security levels on the dark web shops.
- But you need to check the credit score before you buy them.
- You probably don't want to access any of the websites where any of this stuff can be bought.
Dark Web Marketplaces In 2025: What’s For Sale And How To Stay Safe
Meanwhile, Facebook also offers dark web access to their social network. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users). MacOS users will need to drag and drop the Tor Browser icon to the Applications folder. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store.
The Best Dark Web Markets To Consider In 2025
- Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records.
- Scrub the metadata from files before sharing them on the Dark Web.
- The second category consists of data stores, which specialize in stolen information.
- He says most of the sites on the regular internet, which the Senate report focused on, are scams in which dealers will take money and fail to deliver.
Also, there’s always the small, but real, chance of getting ripped off on the dark web when visiting a dark web market. Always prioritize your security, privacy, and adherence to legal and ethical norms above all else. Remain vigilant, adapt to evolving risks, and be mindful of any changes in regulations or best practices.
However, their market is like the surface web, and you can even find job postings like the one below. In Example 7 below, buyers can actually choose which state database they would like to purchase. Voter fraud, scams, and data breaches make the rounds in global headlines all the time, but entire lists of voter data are up for grabs in dark web auctions. In Example 2, the seller has put on a festive sale—201 American Express credit cards—with a special deal just in time for the holidays. One of the most common items sold on the dark web includes credit card numbers.

Government Data
Being able to have your drugs delivered right to your door is so much simpler. But when you buy online, you can read reviews and look at the forums. Her background in computers and information security gave her an advantage when it came to navigating the dark web. She had never purchased drugs in the conventional way—and, at the age of 28, still hasn’t. Marie had never purchased drugs in the conventional way—and still hasn’t. He no longer likes buying from the streets of New York, as he did when he began using heroin in the 1990s, because of the risks he experienced in certain neighborhoods.
Law Enforcement Efforts
She has recently conducted commissioned research for the NSW Coroner's Office, the WA Mental Health Commission and the Victorian Department of Health and Human Services. You'll often see a sign in stores that says "look, don't touch," and it's not a bad adage to bear in mind as you navigate around the dark web. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with.
Many DNMs sell “pressed pills” which are fake pills cut with more dangerous illegal substances. Still, it isn’t unheard of for people to be arrested for buying drugs on DNMs. More often than not, law enforcement is targeting the sellers more than the buyers. There’s nothing stopping sellers from packing up and leaving the market at any time.
Step 4: Funding Your Darknet Account
By the way, most have shipping services. And no, they don’t all sell drugs or firearms. Believe it or not, the dark web even has online shops.
Why Dark-Web Drug Marketplaces Can Be A Refuge
We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. Nearly all dark web commerce sites conduct transactions in bitcoin or some variant, but that doesn’t mean it’s safe to do business there. The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services.
Why Buy Credit Cards On The Dark Web?
Implementing multi-factor authentication and keeping software and security systems updated can also minimize the risk of falling victim to credit card fraud. This involves implementing robust data protection protocols, enforcing strict access controls, and educating individuals about the importance of securing their personal information. Individuals should exercise caution when sharing personal information online, be wary of phishing attempts, regularly monitor financial accounts, and report any suspicious activities to the appropriate authorities.
Often written as RussianMarket, this is the largest marketplace for stealer logs. STYX is a great example of a ‘new model’ market with a searchable structure and trusted vendor processes, which helps buyers quickly filter for fresh data. Unlike older drug-oriented markets, STYX looks more like a specialized cybercrime exchange than a bazaar. Its listings focus on stealer logs, initial access and financial credentials, making it highly relevant for financial security professionals. As such, they are typically under intense scrutiny from both law enforcement and security professionals. The offerings include leaked credit card details, exploit kits, hackers for hire and advertisements for hitman services.
From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. As you can imagine, bad actors around the world would be attracted to any method of keeping their illegal activities undercover, and began to appreciate the dark web as a place to more or less safely conduct their activities. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
Immediately after a big takedown, users flood to remaining markets or spawn new ones a whack a mole cycle. It specialized in narcotics fentanyl, heroin, cocaine, stolen financial data, fake documents, and even in house money laundering/mixing services. It specialized in narcotics, stolen data credit cards, credentials and contraband. Silk Road’s demise proved that even Tor hidden sites could be penetrated by good detective work, prompting many users to flee to successor markets. These markets use cryptocurrencies and encryption to hide, but law enforcement’s growing technical skills have repeatedly broken them open. If you accidentally stumble upon illegal content on the dark web, immediately close the website and disconnect from the internet.
Choosing A Safe And Trusted Dark Web Marketplace
This is where drug trades, weapon sales, human trafficking and a number of other illegal operations are conducted behind the veil of internet anonymity. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. All applications are automatically blocked if they try to access the internet without using Tor, Persistent Storage is encrypted by default, and as mentioned above, nothing is ever written to the computer’s hard drive.



