The UniCC team also gave its users 10 days to spend their balances, while also warning customers to "not follow any fakes tied to our comeback." EMV stands for “Europay, Mastercard, and Visa,” the companies that initiated the chip standard. “As currently there are no widely used technologies that can completely clone bank card EMV chips, we expect cybercriminals specializing in harvesting bank card dumps to encounter further challenges,” Group-IB said in a statement. New marketplaces include All World Cards, BINART, CC Shop, Dundee Shop, Flowcc, Hogwarts Market, Rockefeller’s Store and Wixxx, according to threat intelligence firm Intel471, but “no dump shop or threat actor has been able to fill the void” left by Joker’s Stash. Criminal groups like the gang known as FIN7 knew they would find customers on the forum.
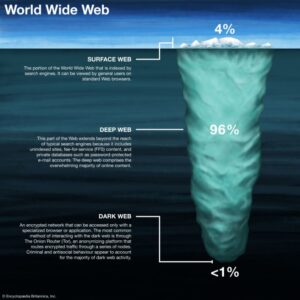
While it mainly focuses on drug sales, hacking-related topics are increasing, making it a significant forum despite its lower ranking. Cracked operates on the surface web, discussing combo lists, vulnerabilities, and hacking tools. Established in 2015, Nulled is a notorious English-language cybercriminal forum on the dark web. It connects cybercriminals with collaborators for hacking, fraud, and RaaS activities. Founded in 2005, Exploit is a leading Russian hacker forum operating on both TOR and the surface web. Its stance against sharing data about Russia indicates a nuanced approach to geopolitical sensitivities.
Prevoty Is Now Part Of The Imperva Runtime Protection
- Not all the above details are available for all 1.2 million records, but most entries seen by BleepingComputer contain over 70% of the data types.
- Law enforcement agencies actively monitor these platforms, and infiltrators may pose as fellow carders to gather evidence.
- Cybercriminals use a range of nefarious technological and social engineering techniques to steal credit card information.
- Beyond the above techniques, which allow you to directly validate if traffic originates from a real user or a bot, use the measures below to strengthen your security perimeter against cracking bots.
- They then use bots or automated scripts to test these cards on websites that process payments.
The solution uses more than 350 advanced machine learning algorithms, behavioral analysis, and predictive methods to detect and mitigate automated carding attacks with exceptional accuracy. While cybercriminals have become increasingly sophisticated with their attacks, many online retailers have not followed suit, continuing to rely on traditional or ineffective security tactics. The Federal Trade Commission reported $148 million in fraud-related gift card losses in the first nine months of 2021 alone. Additionally, many online merchants provide a specific webpage for gift card balance checking. Gift card cracking is a variation of carding where attackers use bots to systematically test large volumes of possible gift card codes on a merchant site in order to identify valid combinations.
How Do Carding Attacks Work?
One compromised payment processor or e-commerce platform can yield thousands of card numbers at once. The pricing varies based on the card type, with premium cards from certain banks fetching higher prices. Credit card fraud on the dark web operates quite differently from what many people imagine.
Figure 3 Card cloning services as advertised on dark web chatrooms In the recent weeks, Cyberint has detected a rise in the dark web trade of ‘fullz’, for use in the fraudulent application of disaster loans. They are on top of the latest TTPs and monitor rising threat groups, malwares and trends. The Cyberint Research Team work round the clock to unearth the latest threats to SMBs and enterprises. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action.
Are Carding Bots Easy To Detect?
Every chargeback hurts a business’s reputation with credit card processors. Chargebacks can happen for legitimate reasons (for example an erroneous purchase or a clerical error), but are very often the result of fraud techniques like carding. The objective of carding is to identify which card numbers or details can be used to perform purchases. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. With the large number of illicit channels that exist on Telegram, we also see malware being distributed, ransomware being sold (as well as other hacking tools), step by step guides for cybercrime, and payment facilitation using cryptocurrencies for illicit transactions.
These forums serve as illicit marketplaces for compromised cards, carding software, tutorials and fraud-as-a-service offerings. Among these are platforms dedicated to carding—a cyber crime niche centered on the large-scale use and abuse of stolen credit card information. Malware can be used to steal credit card information by infecting devices to log keystrokes, intercept online transactions, or extract saved card details. Carding schemes typically involve fraudsters illegally obtaining card details, checking the card is active by attempting small transactions, purchasing hard-to-track prepaid cards with valid stolen details, and then selling the prepaid cards for profit. Hundreds of millions of payment card details have been stolen from online retailers, banks and payment companies before being sold on online marketplaces such as UniCC.
What Can You Find On Forbidden Telegram Channels?
Early detection enables your security team to prevent a transaction, minimizing the risk of a chargeback. I’ve investigated too many breaches where malware jumped from an infected office computer to the payment network. Require multi-factor authentication for high-risk transactions, but it needs to be implemented intelligently.
The Truth About User Agent Spoofing: Why It’s Costing You Real Money
For example, another app with similar features Credit Card Reader NFC (EMV) 5.1.4 (nodpi) doesn't access the Internet (No Internet permission) and the operator needs to confirm credit card details manually. Cybercriminals exploit the same approach by manipulating HCE for malicious purposes to process compromised credit card data via NFC. Notes were detected onmultiple forums on the Dark Web that using NFC may be less suspiciousthan traditional carding methods. Therefore, the merchandise can be“purchased” at the POS terminal, but the credit card terminalwill not submit the transaction for payment to the merchant’spayment processor. In this case, bad actors"tap" their mobile devices with stolen, compromised data tomake fraudulent transactions. As NFCtechnology became more widespread, reports of fraud and cardingincidents started to emerge, mainly as mobile payment systems likeGoogle Wallet and Apple Pay were introduced.
Named after the web security vulnerability “Cross-Site Scripting (XSS),” the forum caters primarily to Russian-speaking cybercriminals and hackers. Selecting the top dark web hacker forums requires a systematic approach to ensure that we identify the most relevant, active, and influential platforms. Organizations must consider ethical and legal considerations when monitoring hacker forums. By exploring the most active and influential forums, we hope to shed light on cybercriminals’ evolving tactics and strategies.
Loyalty Points Fraud
Others suggest that the future of carding will move to other platforms, like Telegram – although not all users trust the instant messaging service. On January 2022, a message appeared on a prominent carding forum stating that the Russian Internal Affairs Ministry had shut down the site as part of a "special law enforcement operation". While the human cost of carding and credit muling is significant, it is essential to remember that victims are not alone in their struggle. Victims of these crimes should have access to resources such as financial counseling, legal assistance, and credit monitoring services to aid in their recovery. Financial institutions and online platforms must invest in robust security measures to detect and prevent fraudulent activities. Jane, a victim of carding, recounts the distress she felt upon discovering unauthorized transactions on her bank statement.
Industry-Specific Cyber Threat Intelligence Powered By Agentic AI
Tutorials range from guidance on using legitimate websites with stolen credit cards, to tips on avoiding IP address flagging and methods for exploiting mobile payment services and cryptocurrencies to drain funds. As a result, carding communities are developing new strategies to leverage existing online platforms and withdraw money from stolen credit cards. Carding forums act as central hubs for cyber criminal activity—particularly for promoting websites and Telegram channels that sell stolen credit card data. Among these threats is carding, a type of fraud used by cybercriminals to profit from stolen credit card information.
It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. With over 40,000 product listings and valued at around $15 million, it’s a sprawling marketplace and go-to destination for drugs, counterfeit items and cybercrime tools. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. Some were taken down by law enforcement, others just vanished overnight with users’ money. Ransomware and cryptocurrency-based crimes saw a significant increase in 2025, with $2.17 billion stolen from crypto platforms, surpassing the total for all of 2024.
- Still, the best defense against carding is to take proactive measures.
- Some carders also track your IP (Internet Protocol) address to snag your credit card info.
- They predicted that if the issues aren’t resolved, carding won’t be at all profitable within “a few years.”
- Criminals used this bot to enumerate through possible gift card account numbers, and automatically request the balance account of each card number.
- As Elihu Yale specifically sought to mention, all “deposits and payments” to Yale Lodge were still functioning – only payouts from the vendor were apparently impacted.
Another user said it’s “scary” to imagine what the future of carding will look like. They said few cyber criminals can make real money from this type of malicious activity; a few years ago, forum articles regularly spoke of beginner carders earning $3,000–5,000. Until now, carding was seen as a way for novice crooks to begin their criminal careers because of the low startup capital required. We’ve been tracking the carding-related chatter throughout 2022 and have seen worry morph into frustration, and then into predictions that carding is on its way out. This carefully developed system of methods for obtaining and trading card details was shaken up earlier this year by a shocking law-enforcement operation.
In this blog, we examine the series of rather unique events that led to this threat actor’s peculiar downfall. It became the official sponsor of at least one prominent cybercrime forum and held verified status on many others. Many carders follow the trend of creating pseudonyms for themselves, using names of prominent politicians or media personalities.
But the shutdowns and disappearances appear to be having an impact on some users, who are starting to get worried. In the labyrinthine world of finance, the alchemy of credit reserve calculation transmutes… If you notice any discrepancies, report them immediately to your financial institution. Additionally, raising awareness among the general public about the risks of sharing personal information online and promoting safe online practices is crucial. The financial burden of legal fees added to his already dire situation, leaving him in a state of despair.