Businesses pass fraud-related costs on to consumers through higher prices. Automatic payments get declined, travel plans get disrupted, and sorting everything out with the bank can take hours. Their payment processor raised their rates, and suddenly their already-thin margins became unsustainable. I’ve worked with family-owned businesses that nearly went under after getting hit with a wave of fraudulent purchases.
By monitoring dark web markets, we often discover data breaches before they’re publicly reported. When used correctly, it provides strategic intelligence that can prevent major financial losses. These generated numbers link to your real card but can be limited by merchant, amount, or time. Early detection enables your security team to prevent a transaction, minimizing the risk of a chargeback. I’ve investigated too many breaches where malware jumped from an infected office computer to the payment network.
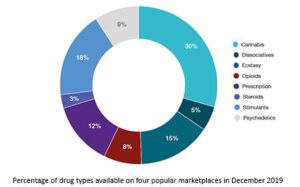
It’s ‘dark’ if you can’t just walk around and see it—you need special access tools, special permissions, special accounts—things like that grant you or buy you access to it,” explains Chris Novak, director of Verizon Threat Research Advisory Center. The dark web—about 6 percent of the internet—is home to TOR-encrypted sites and many illegal activities. The “surface web” is the portion of the World Wide Web that is readily available to the general public and is searchable with standard search engines, such as Google and Bing—but the surface web accounts for only 4 to 10 percent of the internet, according to various estimates. Many other illegal darknet marketplaces have also shut down voluntarily over the winter for unknown reasons. “After the initial free drop,” Draghetti said, “additional cards were made available for purchase, typically priced around $25 each.” This isn’t the first time that a criminal enterprise has distributed stolen data in such a way.

Over the past few years, the availability of information and data prices on the Dark Web has drastically risen. Collins said, "not divulging anything that is personally identifiable to you." The local FBI office says even criminals buying and selling from other countries are being caught.

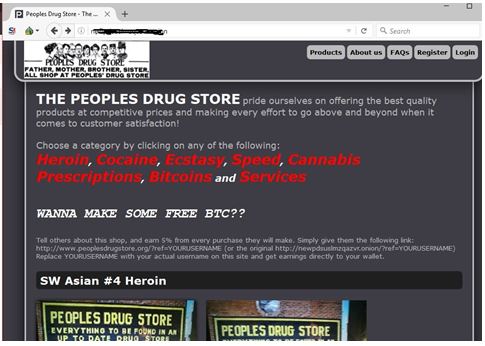
But that’s not all; there are also cardholder details such as their full name, address, date of birth and telephone number as well as email address. That was then; now, you are more likely to find a roaring trade being made on the dark web in the likes of stolen passwords and account credentials, phishing exploit kits and malware-as-a-service platforms. In the ever-evolving landscape of cyber threats, businesses face not only financial losses but also significant reputational damage when targeted by fraud actors on the dark web. On these forums, actors will often share techniques, hacking tools, strategies, and resources for conducting fraudulent activities. These details are primarily sought for physical use, enabling activities such as cash withdrawals from ATMs. It includes critical information such as the bank account number, account balance, service code, PIN code, and card verification code.
Million Stolen Credit Cards Given Away Free On Dark Web Forum
Mador recommends that merchants carry out penetration testing, via a third-party security company, to scan websites and applications on an ongoing basis. “Be aware of the data that you have and try at all costs to protect it, but also understand what the typical threats might be that are targeting you,” says Wilson. “As they conduct business and never scam each other, their reputation rises.” These forums are “created and run for the purpose of conducting business between cybercriminals in a fairly trusted environment—as much as they can have.”
Top 7 Dark Web Marketplaces
- Others might be stolen through phishing attacks on companies, stealing their customers’ payment information.
- Automatic payments get declined, travel plans get disrupted, and sorting everything out with the bank can take hours.
- Of all the data breaches analyzed by Trustwave in the company’s “2019 Global Security Report,” breaches originating from magnetic stripe data comprised 22 percent of compromises in 2017, but only 11 percent in 2018.
- Buying credit cards on the Dark Web requires careful navigation and adherence to specific steps to minimize risks and maximize the chances of a successful transaction.
Require multi-factor authentication for high-risk transactions, but it needs to be implemented intelligently. Instead of storing actual card numbers, each card should be converted into a unique token. Using a layered approach helps distinguish genuine fraud from false positives. They look at everything from how quickly a customer fills out payment forms to whether their IP address matches their billing location.
What Is Spyware? Definition, Types And Protection 2026
These directories provide a list of popular marketplaces, forums, and other websites, making it easier to discover and access them. Explore these resources to gain insights into active marketplaces and their reputation. There are dedicated forums and websites that track and review these marketplaces, providing valuable insights and user experiences. However, with the right approach and tools, individuals can discover these hidden marketplaces. Fraudsters may try to deceive buyers by sending malicious software or attempting to steal their personal information.
In addition, criminals on the dark web follow a “code of conduct” designed to protect their illicit business interests. “From one breach, all these different groups are going to do something different—maybe combining data from one breach with another breach or maybe selling the data to conduct business email compromises,” or other criminal endeavors. “You can have a breach on the surface web—then 15 to 20 different sites on the dark web might be selling that data,” says Wilson. “Many of them offer an alternate card for the next six hours if the one they purchased doesn’t work,” says Mador.
Protective Measures And Precautions
The payment information is then posted for sale on the dark web where other threat actors can purchase and use it. Payment information is stolen in a variety of ways before it ends up on the dark web. Legitimate users of the dark web include activists, or people who live under oppressive regimes, but they only account for a small percentage of the dark web. The phrase “dark web” conjures images of illegal activity, but it simply refers to the encrypted part of the Internet that isn’t indexed by search engines. Historical cases like Joker’s Stash and a steady churn of successor platforms indicate that disruption rarely equals eradication, and researchers expect new marketplaces to fill gaps left by enforcement actions .
Mature Content
Navigating the Dark Web to find marketplaces where credit card details are bought and sold can be a daunting task. Buyers can purchase these card details and use them to make fraudulent transactions or resell them to others looking to capitalize on stolen identities. As mentioned above, purchasing a stolen credit card on the dark web gives you access to a lot of information, including the zip/postal code of the credit card holder. The answer is surprisingly a measly $5.72 USD on average, the median price of a stolen credit card sitting at $5 USD. Focusing mostly on the North American market, for the purpose of this research, Flare has sampled the information of 500,000 credit cards.
PayPal Account Or Card Cancellation
If you notice anything unusual, contact your credit card company immediately to report the issue. Additionally, fraudulent charges can lead to overdraft fees, late payment penalties, and damage to credit scores. For example, victims may find themselves facing hefty credit card bills for purchases they never made.
Your personal information can sell for upwards of hundreds or even thousands of dollars on the dark web—and you might not even know it's even out there to begin with. The average price for your personal information can range from as little as $1 to more than $4,000. Our comprehensive offensive and defensive cybersecurity portfolio detects what others cannot, responds with greater speed and effectiveness, optimizes client investment, and improves security resilience. Trustwave, A LevelBlue Company, is a globally recognized cybersecurity leader that reduces cyber risk and fortifies organizations against disruptive and damaging cyber threats.
Verify essential details such as the card number, expiration date, and CVV code. Avoid sharing personal or financial information that is not necessary for the transaction. Consider factors such as the type of card, issuing bank, credit limit, and validity period. It routes your internet traffic through a network of volunteer-operated servers, making it difficult to trace your online activities. Accessing the Dark Web safely requires careful consideration and implementation of security measures to protect your identity and personal information.
- Tools like an Address Verification Service (AVS) can help detect fraud in online purchases by comparing a customer’s billing address with the address on file with the issuing bank.
- The dark web has become a notorious hub for illegal activities, and credit card fraud is no exception.
- The dark web provides an anonymous platform for these illicit activities, making it difficult for law enforcement to track down the culprits.
- Notably, cryptocurrency has become a valid option for carding operations, whether through exploiting stolen crypto wallets and accounts or using stolen credit card details to purchase cryptocurrency.
- Look for vendors who provide detailed information about the cards, including bank names, types of cards, expiration dates, and CVV numbers.
Be Cautious Of Online Transactions
Next, we’ll look at how tech fights dark web card fraud. Many tracker apps link directly to bank accounts for up-to-the-minute info. Use strong passwords, monitor accounts, and set up alerts.
“With things like cryptocurrency, ransomware, cryptojacking—all of these things that allow these criminal groups to bring in more money” enable illicit activities. The landscape where these criminals are operating “is undergoing a shift and a change, and that’s something to be aware of.” “You have seen criminals move more toward the deep web and surface web. And all payments stakeholders can visit Visa’s website to see public reports and press releases regarding malware, indicators of compromise, mitigation, and protection. Payments professionals also should become more educated—by relying on industry partners, information sharing consortiums, retail and financial services information sharing and analysis centers—and then educating merchants, says Capezza.
Some criminals organize stolen card data by ZIP code, according to Novak, “because it makes it harder to conduct fraud detection,” he says. In addition, gift cards have become a popular way for criminals to turn stolen card data into money. These groups of cybercriminals have been very active in the past two years, stealing credit card data by injecting malicious code into the checkout pages of merchants’ e-commerce stores. But it’s not just the dark web that poses a problem if payment card data is stolen—it’s the entire “cybercrime underground,” says David Capezza, senior director of payment fraud disruption at Visa. This category, known as Dumps on the dark web, encompasses the raw magnetic strip data of credit cards. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.
Moreover, demand for the login credentials of other online services such as Netflix, HBO Max, and Hulu has increased, leading to an influx of information for sale on the Dark Web. As well as this, crypto account sales have increased on the Dark Web as cryptocurrencies have shot up in value. There are countless products for sale on the Dark Web but we’ve found the most popular data categories, all of which are seeing massive sale increases. Here is what you need to know about how much your data costs, and how you can ensure it doesn’t end up for sale on the Dark Web. We’ve reported on many recent security attacks such as the FlexBooker, Volkswagen, and Gigabyte breaches, as well as supply chain attacks like the SolarWinds breach.