Among them was a Paraguayan man they believe was the network’s ringleader. In the operation, police dismantled multiple pedophile chat sites, detaining four suspects. Law enforcement agencies frequently target sites that distribute child pornography. Bitcoin allows for anonymous donations, making it easier for terrorists to fund their activities and purchase weaponry.
Method II – VPN Over Tor
Websites accessible through the Tor browser end in this domain name, just as sites reached through traditional browsers such as Chrome and Firefox end with domain names like .com, .org, .gov, and .edu. While a browser lets you connect to the internet, a search engine is what you use to search the internet once you get on it. A dark web search engine can help you surf sites on the Tor browser. Instead, Tor uses a random set of encrypted servers known as nodes to keep users and sites anonymous. Here’s a quick tutorial on how to safely access the dark web and tips on how to use it. Instead, everything stays internal on the Tor network, which provides security and privacy to everyone equally.
If you’re not engaged in illicit activities, it’s not a crime to use the dark web to protect your privacy. Although your internet traffic is encrypted and routed through multiple layers on Tor, your ISP can still see that you’re connected to Tor. But criminals also take advantage of Tor’s anonymity to carry out illegal activities both on and off the dark web.
- Because of this reason, it is quite easy to encounter fraudulent or malicious websites and you need to take a cautious approach to manually avoid them.
- The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them.
- Whatever your reasons for entering the dark web are, you must follow some crucial steps to ensure your safety so that you can access it in an entirely safe and anonymous way.
- The entry node is the first server in the Tor chain, the relay node is the middle node and the exit node is the last server in the network.
- You can access these websites without worrying about someone snooping on a Tor exit node, offering more private browsing of what is known as the deep web.
As I mentioned previously, using the Tor Browser will slow down your browsing. While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser. Stick with the original settings – they’re the most secure. When you install the Tor Browser, it comes preconfigured with the most secure privacy settings. Also, since the Tor Browser is based on the Mozilla Firefox platform, it’s susceptible to the same attacks that other browsers are.
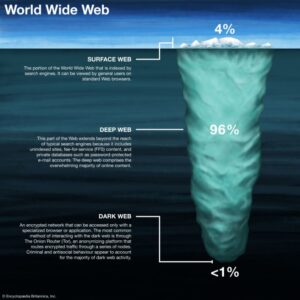
It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. Hackers spend a lot of time on the dark web, and it's not too difficult to get access to hacking tools and data leaks in this part of the internet. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Some of the websites to look out for on the dark web include mirrors of both the BBC and the ProPublica investigative journalism platforms, built to help inform people who are living in countries where the internet is heavily censored. However, there are plenty of legal and legitimate online activities that require privacy and anonymity.
Dark Web 101: The No-Nonsense Guide To The Hidden Internet
Terrorist groups have used the dark web since its inception due to its anonymity and lack of regulation. However, unlike Facebook, the DWSN requires users to remain anonymous and not reveal personal information to protect their privacy. Traditional social media platforms such as Facebook have also created versions that work with the dark web to provide services across all dimensions of the World Wide Web. Ross Ulbricht, the creator of Silk Road, was arrested on suspicion of hiring a hitman to kill six people, but the charges were later dropped. The indie game Sad Satan was claimed to have been found via the dark web, but inconsistencies in the reporting cast doubt on the story.
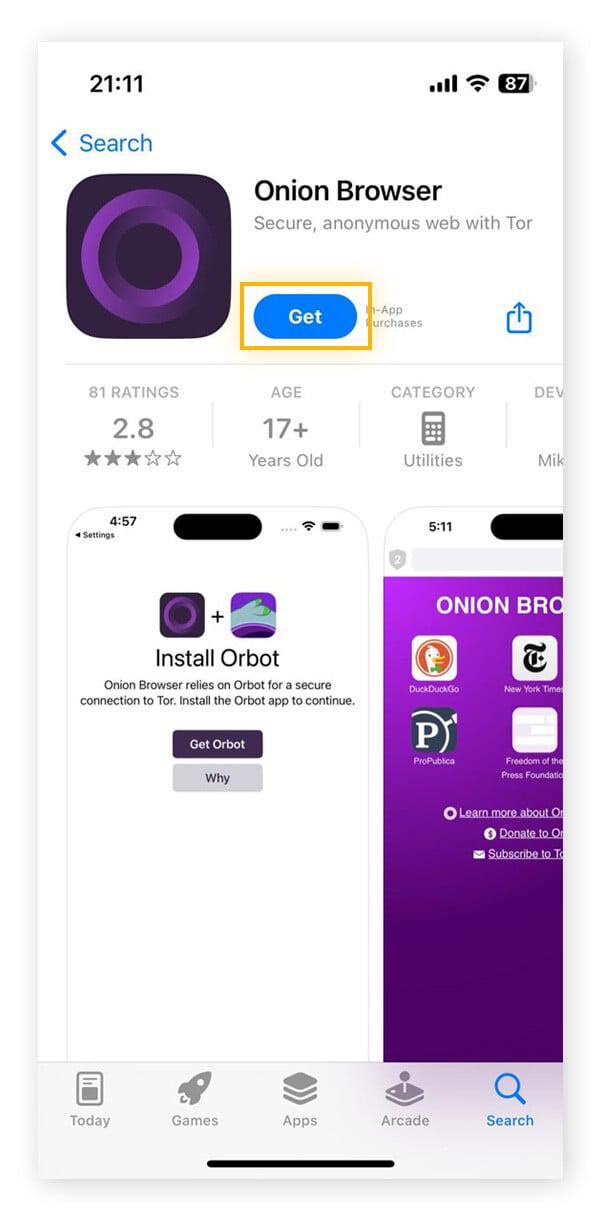
- You’ll need a specialized dark web browser like Tor, which lets you access hidden parts of the internet while protecting your identity.
- While Tor is the most common method for accessing the dark web, I2P and Hyphanet offer alternative options for secure and private browsing.
- Dark web domains tend to be inconsistent — new ones pop up and others disappear, which makes sense if they offer questionable or illegal goods and services.
- Now that your connection is active, it’s encrypted and untraceable by your internet provider.
Such data includes medical records, financial information, research papers, private forums and networks, and other content. If you want to access the dark web, your first step toward a more private experience should be to secure your internet connection and data with a reliable VPN. Once you have the Tor or Onion Browser downloaded and are connected to the Tor network, you can browse the dark web by visiting .onion links — dark web sites that are accessible only via the Tor network. Second, it allows you to access websites or services that block Tor but accept VPN traffic, such as streaming or banking sites. While it’s not a browser, it includes Tor Browser installed by default that provides anonymity for web browsing and enables users to access the dark web. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers.
Other Built-in Tor Features You Should Know
Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. A logless VPN, which doesn’t store any traffic logs nor session logs is highly preferable. Your ISP only sees the encrypted VPN traffic and won’t know you’re on Tor. All your device’s internet traffic first goes to the VPN server, then bounces through the Tor Network before ending up at its final destination. A VPN, in combination with Tor, further enhances the user’s security and anonymity. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing.
Are Dark Websites Illegal To Use And Visit?
If someone visits two different sites that use the same tracking system, they'd normally be followed across both. And that's why organisations such as the CIA, the New York Times and Facebook have onion versions. That central control allows for censorship, as by interrupting that lookup a site can effectively be banned from the web — this is why Turkish protesters were spraypainting IP addresses on walls in 2014, to tell others how to access Google directly without going via a DNS server.
One of the most significant of these is the ability to adjust the browser’s security level. By clicking the “Connect” button, Tor Browser will automatically begin the process of establishing a connection to the Tor network. When the Tor Browser is run for the very first time, users will be presented with a “Connect to Tor” window. For Android mobile devices, the official Tor Browser application can be found and installed directly from the Google Play Store. Some Linux distributions may also offer Tor Browser through their package repositories, but using the official download from the Tor Project website is generally recommended to ensure the latest version and integrity. For users running Windows, the installation process involves navigating to the official download page and selecting the download link for Windows, which will typically download an executable (.exe) file.
How To Install Red Hat Enterprise Linux (RHEL) 9 ? RHEL

I don’t recommend seeking out dark web content unless you have a specific reason to do so. Remember to update the Tor Browser regularly to ensure you have the latest security patches, and scan your computer for malware regularly using antivirus software. Don’t click on random links from strangers while browsing the dark web, and never give away any personal information. To properly peel back the internet's layers, you need a tool that provides layers of encryption to hide your activity.

The risk of infection is considerably higher compared to the surface web due to the lack of regulation and security oversight. Ransomware, which encrypts a user’s files and demands a ransom for their release, and keyloggers, which record keystrokes to steal passwords and other sensitive data, are among the types of threats commonly found on the dark web. The dark web serves as a common platform for cybercriminals to distribute various types of malicious software designed to compromise users’ devices and steal their personal information. Users should be well aware of these risks before venturing into this part of the internet.
Free The Internet
Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. The deep web is just the part of the internet you can’t find with a search engine. When you search for something on Google or Bing, you’re using the clear web.

Understand Legal Risks
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. Buxyen is a privacy specialist dedicated to building and deconstructing secure digital environments. Each time you go online, you create a digital footprint that can be tracked. Think of the dark web as a hidden neighborhood on the internet. Using a VPN first hides your connection to the Tor network and gives you better privacy ultimately. Tor only anonymizes your identity through its routing; while your ISP won’t know who you are, they will see that you connected to the Tor network.
Onion Browser maintains a change log of release notes, including security issues and results of previous security audits on GitHub. Due to technical restrictions on Apple’s proprietary iOS platform, the Tor Project has not yet released an official Tor Browser for iPhone and iPad users, but endorses Onion Browser for iOS users who want to browse the web anonymously. (The Guardian Project’s similarly named Orbot, a Tor proxy for Android that lets you tunnel all your app traffic over Tor, not just web traffic, continues to be alive and well.)
Many major companies have reserved .onion domains and host websites there, and there is a list of onion services on Wikipedia. This separation helps maintain anonymity and shields genuine personal details from unauthorized access by threat actors lurking in the shadows of the clandestine online landscape. A VPN encrypts your data and hides your IP address, making it more difficult for third parties to monitor your online activities.
These pages come with extra protections for user anonymity and data security, and you need special software to access them—you can't get at them through your normal web browser, like you can with much of the rest of the deep web. In addition to the categories below, I exclusively cover ad blockers, authenticator apps, hardware security keys, and private messaging apps. You can still be tracked at network entry and exit nodes, as indicated by reports that police identified Tor users by surveilling data centers.