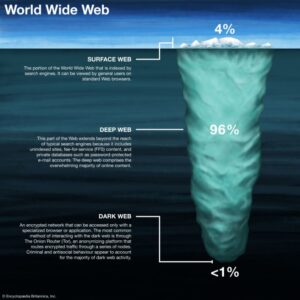
The system is designed to provide enhanced security and privacy features. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
Top 7 Dark Web Marketplaces
Buyers can enable two-factor authentication, and transactions are protected by escrow, including multisignature escrow for added safety. Taking these steps cannot eliminate all risks (exit scams and law enforcement still happen), but they significantly improve privacy and security when researching dark web markets. In a standard escrow model, the buyer sends payment to the market’s escrow account; the vendor ships the item; once the buyer confirms receipt, the market releases funds. These sites operate as self-contained platforms with .onion addresses that are not indexed by Google. These hidden e‑commerce sites run on Tor hidden services with .onion domains, using cryptocurrency payments (often Bitcoin or privacy coins like Monero) to conceal identity.
Recent Shutdowns And Exit Scams

Transactions typically use Bitcoin for payment, sometimes combined with tumblers for added anonymity and PGP to secure communications between buyers and vendors from being stored on the site itself. From then on, through to 2016 there was a period of extended stability for the markets, until in April when the large Nucleus marketplace collapsed for unknown reasons, taking escrowed coins with it. The market owners set up a phishing website to get the attacker's password, and subsequently revealed collaboration between the attacker and the administrator of Mr Nice Guy's market who was also planning to scam his users. Following these events commentators suggested that further market decentralization could be required, such as the service OpenBazaar, in order to protect buyers and vendors from this risk in the future as well as more widespread support from "multi-sig" cryptocurrency payments. In March 2015, the Evolution marketplace performed an "exit scam", stealing escrowed bitcoins worth $12 million, half of the ecosystem's listing market share at that time. From late 2013 through to 2014, new markets started launching with regularity, such as the Silk Road 2.0, run by the former Silk Road site administrators, as well as the Agora marketplace.
Finding A Silk Road Alternative: What Are The Best Options Today?
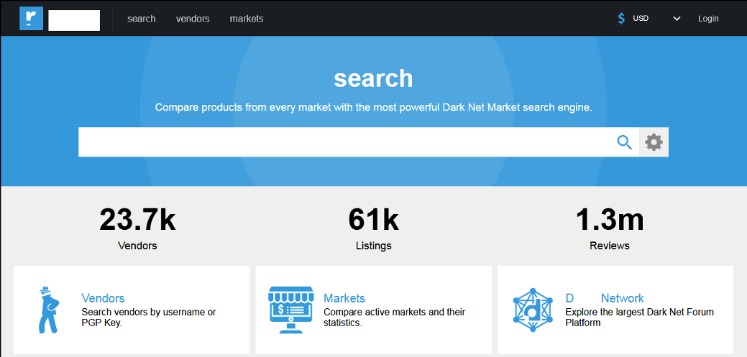
The dark web is home to many online marketplaces, offering everything from digital goods to rare items. Darknet marketplaces in 2025 illustrate a resilient and evolving underground economy. Focusing intelligence collection on specialised marketplaces yields better ROI for threat detection and proactive defence. At the time, it had over 600,000 users, 17,000 listings, and approximately €250 million in transactions.
If you want to find its current links, you can search for terms like “Daniel replacement.” The best thing is to actually understand how to find the fresh, new links. Hence, you never know when a popular .onion site is going to vanish, or even die. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies. The biggest and most frustrating part about dark websites is that they live for a short span of time.
A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. Wondering what the best dark web VPN to use with Tor is for accessing the best onion sites on the dark web? As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web.
Best Threat Intelligence Platform Vendors: Enterprise Buyer's Guide
When accessing a website through Tor, the connection is bounced through multiple nodes, obscuring the source of the traffic. In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace. However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity. One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S.

Later markets such as Evolution ban "child pornography, services related to murder/assassination/terrorism, prostitution, Ponzi schemes, and lotteries", but allow the wholesaling of credit card data. Many vendors list their wares on multiple markets, ensuring they retain their reputation even should a single market place close. Many sites use Bitcoin multisig transactions to improve security and reduce dependency on the site's escrow.

Since product information is quite detailed, an implementation with up-to-date darknet market data is feasible. To aid in this activity, dark net market data—searchable by brand—could be made accessible to companies. The shutdowns forced by law enforcement have exposed the vulnerabilities inherent in these marketplaces.

In-depth Market Overviews & Additional Content
Some health professionals such as "DoctorX" provide information, advice and drug-testing services on the darknet. Some users report the online element having a moderating effect on their consumption due to the increased lead time ordering from the sites compared to street dealing. Centralized market escrow allows a market to close down and "exit" with the buyer's and vendor's cryptocurrency at any time. This suggests that law enforcement responses to cryptomarkets result in continued security innovations, thereby making markets more resilient to undercover law enforcement efforts. A further PIN may be required to perform transactions, better protecting users against login credential compromise. Due to the decentralized nature of these markets, phishing and scam sites are often maliciously or accidentally referenced.
The process of link verification is community-driven, with users reporting successful connections and flagging potential phishing attempts. Specialized link aggregator sites and forums serve as the primary repositories for these addresses, verifying their validity and operational status. This focus on a simple shop interface is not merely a convenience\; it is a strategic element that supports the market's operational efficiency and user satisfaction. Once the correct address is acquired, it is entered directly into the Tor browser, establishing a secure and private connection to the market's interface.
Hydra Market 2015 2022 Europe’s Drug Giant
Torrez Market is a new darknet market that has gained popularity due to its user-friendly interface and wide range of products. The technology and network category includes trust factors regarding the user experience on websites and the smoothness of internet connections. It has a dual-wallet system, which means users can keep their funds in a secure wallet or a spending wallet. These markets offer a wide range of goods and services, including drugs, weapons, hacking tools, and counterfeit items.
Below are the best ways to stay safe while using dark web marketplaces. Finding verified dark web marketplaces is not as simple as searching on Google. ASAP Market focuses on digital goods, software, and security tools, making it one of the few markets without illegal drug sales. We The North Market is built for secure, trusted transactions with some of the lowest vendor fees in the industry.
Strong Encryption For Safe Shopping On The Darknet
- Top darknet marketplaces are anonymous online marketplaces on the dark web where users buy and sell illicit goods or services.
- It operates both on the dark web and the clear web, making access significantly easier.
- In fact, migration was observed37 after the closure of the AlphaBay marketplace when other marketplaces, namely Hansa and Dream Market, experienced an abnormal spike in activity.
- The market's architecture facilitates anonymous online commerce by integrating a mandatory multisignature escrow system for all transactions.
- Use trusted directories or PGP-signed mirrors—30% of 2025 links are scams.
Order details, shipping addresses, and financial transactions are similarly protected, with private keys held only by the communicating parties. Platforms utilize end-to-end encryption (E2EE) for private messages, ensuring that correspondence between a buyer and a vendor remains strictly confidential. Every action, from initial login to finalizing a purchase, is wrapped in multiple layers of encryption, rendering intercepted data useless to any unauthorized party. These cryptographic measures are not an optional feature but a core requirement, functioning as the primary shield for all user activity and sensitive information. This systematic presentation of data transforms the selection process into an evidence-based decision, significantly reducing uncertainty.
How To Access The Dark Web
To the Redditors / mods / Deepdotweb who helped us compile this list, we will keep it growing and updating. However, it is important to be cautious when searching for these links, as many of them may be fake or malicious. Its objective is to eliminate fake or unsafe websites that might contain malware, promoting a safer exploration of the dark web. Bitcoin mixers and “cleaning” services are showing signs of a continued rise in prevalence and sophistication. At the same time, the takedown of Hydra Market pushed cryptocurrency cash-out providers onto other platforms.
For instance, Hansa’s police run honeypot netted thousands of user identities, and dream markets collapse still provokes sting operations. Millions in crypto were recovered, and top Russian vendors and buyers were exposed to investigators. It specialized in narcotics fentanyl, heroin, cocaine, stolen financial data, fake documents, and even in house money laundering/mixing services. On average, marketplaces had 26,342 sales and generated $5,847,417 in revenue.
In 2012, it was closed and several operators and users were arrested as a result of Operation Adam Bomb, a two-year investigation led by the U.S. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Here are some of the now-defunct dark web markets that were notorious for cybercrime. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. WeTheNorth is a Canadian market established in 2021 that also serves international users. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools.