
This extra layer of security gives peace of mind in today’s digital world. They show recent purchases, account balances, and spending trends all in one place. 1 This quick notice helps spot fraud fast, before major damage occurs. These tools scan transactions in real-time, flagging any suspicious charges instantly. These alerts can spot fraud fast and keep your money safe.
There are many techniques to prevent identity fraud that businesses and individuals can use. Instead, stolen data is permanently accessible on the dark web and can be bought, sold, or used in various ways. Financial loss, harm to one’s credit score, and a great deal of stress and frustration as they try to fix the problem can all be experienced by identity theft victims. The cycle is complete when the stolen data is used to generate profit or cause harm. Prices fluctuate like they do in every market, so criminals wait for the right time to sell your data; it can even be years before they do anything with the information they stole.
However, the availability of prepaid cards or vouchers as payment methods may vary among vendors and marketplaces. When engaging in credit card transactions on the Dark Web, understanding the payment methods used is crucial. Positive feedback from previous buyers suggests that the vendor has successfully delivered the promised credit card data and conducted transactions in a satisfactory manner.
Conclusion And How You Can Prevent Credit Card Fraud
Additionally, fraudulent charges can lead to overdraft fees, late payment penalties, and damage to credit scores. For example, victims may find themselves facing hefty credit card bills for purchases they never made. It is imperative for individuals to remain vigilant and exercise caution to protect their credit card information from falling into the wrong hands. Understanding the Dark Web is crucial for detecting potential threats and taking necessary precautions to protect your credit card information. Prepare to be astounded, as we unveil the chilling reality that lies beyond the bright glow of your credit card statement.
This type of payment uses tokenization, which replaces your sensitive card data — like the expiration date and card verification value (CVV) — with a unique, random token. When possible, using a credit card instead of a debit card is a good move too. Or they'll commit "card-not-present fraud," by hacking a website and stealing the online card information that gets entered into the checkout page. You may have never been to the dark web — but there's a chance your credit card information has. How about one of them sharing your stolen financial data? Is there anything scarier than an underground shop of dark web criminals sharing stolen financial data?
Payment Fraud
Initially, this specific marketplace started out by leaking thousands of credit cards. As reported by Bleeping Computer, in an effort to attract cybercriminals to its platform, the hackers behind ‘BidenCash’ have distributed the details of 1,221,551 credit cards. It is entirely focused on financial cybercrime and offers much more than just stolen cards or basic logins.Here you will find malware logs, remote access (RDP), brute force accounts, complete identity packages, and access to financial platforms.
Best Digital Risk Protection Platforms For Security Teams
This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm. The stolen data included names, contact information, and order histories. The exposed data included customer names, addresses, and purchase details.
Warning For Would-Be Fraudsters
The data includes the service code, PIN code, and card verification code, making it highly valuable for thieves. The resulting financial loss from stolen information is tremendous, not only for the individual victim but also for the financial provider and any involved organizations. For legal reasons, the specific marketplaces used in the study remain undisclosed. Vendors sell additional information about the cardholder, known as "fullz", which includes the cardholder's social security number, street address, birth date, and more.
White Hat Market’s Differentiator Was Security
- Pattern recognition through machine learning has revolutionized how we spot compromised cards.
- Malware captures keystrokes, screen activity, and saved credentials, while spyware transmits stolen data back to command servers.
- "The wave of recent departures has potentially been a trigger for UniCC's retirement, as illicit actors see an opportunity in the turbulence to either run away with users' funds or retire to avoid increased law enforcement attention," the researchers said.
- Like other dark web markets, it was accessible only on anonymity browsers like Tor and I2P.
The market is also known for its listings related to financial fraud, such as phishing tools and stolen credit card information. B1ack’s Stash, a new dark web marketplace, recently gained significant attention by releasing 1 million stolen credit card details for free upon their debut on April 30, 2024. What is the price for personal information, including credit cards and bank accounts, on the dark web? This is used to traffick stolen credit cards details by means of malicious skimmers injection in order to receive crypto for them. The greatest dark web marketplace for stolen credit cards known under the name of UniCC has made an announcement that its team is retiring.
Telegram Carding Groups
Payment information moves through a series of specialized dark web markets. The Magecart group pioneered this technique, compromising thousands of online stores by exploiting vulnerabilities in popular e-commerce platforms. While it’s extremely difficult to identify the individuals involved without additional intel, law enforcement personnel and corporate investigators can use these processes to keep tabs on the flow of stolen, counterfeit, or diverted goods. As a reminder, most of the purchases described here are illegal and/or dangerous.

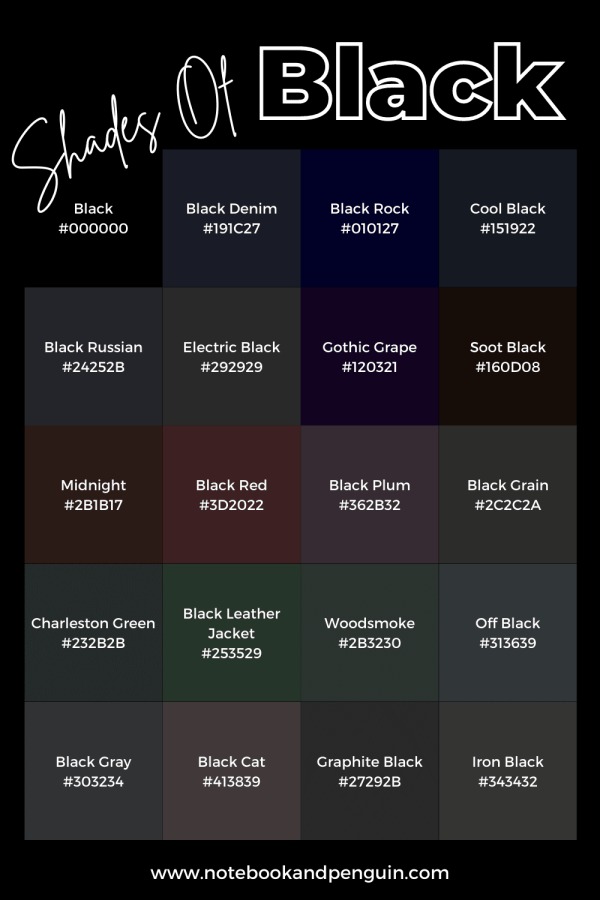
Cyble Titan Endpoint Security
Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing. As with credit cards, the location of the victim whose information is up for sale has a significant influence on price. Back then, the median credit limit on a stolen credit card was 240 times the price of the stolen card, or about 0.42 cents (US$0.0042) per dollar. Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs. Credit card details used for online fraud are cheaper and can be sent in a text message.
Credit Card Fraud On The Dark Web
Engaging in credit card transactions on the Dark Web comes with a host of risks and challenges that individuals must be aware of. The financial repercussions for victims can be debilitating, leading to damaged credit scores, fraudulent charges, and identity theft. The potential profit from these illegal activities is enticing, especially given the relatively low cost of purchasing the credit card information. Buyers must navigate through a labyrinth of fraudulent sellers and law enforcement operations targeting illegal marketplaces. The shop offers stolen card data from around the world for as low as $0.15 per item and uses verification and automated checks to check the validity of the cards people put up for sale on the platform. Regularly reviewing your financial accounts and online activity for unauthorized transactions is also crucial.
- When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces.
- Criminals use stolen credit card information to make unauthorized transactions and drain victims' accounts.
- Stolen identity data is exploited for a variety of malicious purposes.
- Regularly scan your system to detect and remove any malicious software that could compromise your security.
- The dark web provides an anonymous and unregulated platform for these transactions, making it difficult for authorities to trace and shut down such activities.
WeTheNorth has a strong community vibe, with an active forum where users interact and share updates. Despite these markets being generally illicit, they follow the same economic laws and practices as other markets. There has been a steady increase in the availability of goods and services offered in the black markets.
Stolen card details often end up on the dark web marketplace for a quick profit, and this can happen before you even know about it. Regularly monitoring your credit card statements can help you detect any suspicious activity, such as unauthorized transactions. In 2022, for example, BidenCash was linked to the breach of over 1.2 million credit card records. The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.
All World Cards, which appeared in 2021, known for their credit card data leakage activities is considered the most notable. All of these features, its competitive pricing, along with the volume of credit card information listings, make Real and Rare one of the prime sites to trade credit card information online. The ease of obtaining a black market credit card is concerning, with some sellers offering them for as little as $10. The sunsetting comes exactly a year after Joker's Stash, the previous market leader, announced its retirement in January 2021 after having facilitated the sale of nearly $400 million in stolen cards. Fraudsters can use the stolen information for unauthorized transactions, identity theft, or resell the data on other platforms. This incident is described as one of the largest giveaways of compromised credit card data in recent history.
That means buyers pay about 9.2 cents per dollar in the PayPal account, which is almost double the price-to-credit limit ratio on physical credit cards. Due to limited data on credit cards from other countries, we were unable to adequately compare prices for credit cards from different places. For this study, the researchers focused on PayPal accounts and credit cards. When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces.
UniCC has been active since 2013 with tens of thousands of new stolen credit cards listed for sale on the market each day. Cyble posted a list of the top 500 banks affected by the leak of stolen credit cards in descending order. But once you start doing illegal things, like buying drugs or stolen credit cards, that’s when you’re breaking the law. Notably, cryptocurrency has become a valid option for carding operations, whether through exploiting stolen crypto wallets and accounts or using stolen credit card details to purchase cryptocurrency.



