
Naval Research Laboratory to protect sensitive government communications. Also, it contains several illegal goods, stolen data, credit cards, and more. It was known for facilitating the sale of illegal drugs, goods, and services using Bitcoin cryptocurrency. Deep down, the tip of the iceberg is where over 90% of the internet content is.
I2P: The Invisible Internet Project
Clario Anti Spy’s Data breach monitor scans for known breaches tied to your email and alerts you if anything’s been exposed. Before you explore further, check if your data has already ended up on the dark web. Here’s how to access the dark web safely. If you stick to using it for legitimate and legal purposes and proceed with caution, you can have a perfectly safe and secure experience. However, it’s important to remember there are tonnes of legitimate reasons to use Tor to explore the dark web too.
The Tor Browser automatically routes its traffic through the anonymous Tor network. I’ll go into how the Tor system works, explain the Onion Network, what a relay is, and how to make the Tor Browser work best to protect your online privacy and anonymity. Preventive Approach participates in various affiliate marketing programs, which means we may get paid commissions on editorially chosen products purchased through our links to retailer sites.
Unverified Content And Hoaxes
Some Linux distributions may also offer Tor Browser through their package repositories, but using the official download from the Tor Project website is generally recommended to ensure the latest version and integrity. For users running Windows, the installation process involves navigating to the official download page and selecting the download link for Windows, which will typically download an executable (.exe) file. Each relay in this circuit decrypts only one layer of encryption, obscuring the origin and destination of the traffic from any single point of observation.
Device-specific Guide On Accessing The Dark Web
You might often see news stories about criminal activity involving the dark web, and because of what's happening in some corners of the dark web, it tends to put off law-abiding companies and users alike. Some of these sites can be found through regular web browsers, but you'll then need to switch over to Tor once you've got the onion links you want to follow. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you're looking for.
Any online activity can carry breadcrumbs to your identity if someone digs far enough. Most malware infections can be caught by your endpoint security programs. If you choose to pursue exploring any sites on the dark web, you put yourself at risk of being singled out and targeted for hacks and more.
That means, with the right adjustments, you can adapt it for more private browsing. But if your goal is to build a secure and fortified environment for exploring the deep web, Subgraph is a serious and powerful option worth considering. It hasn’t received many updates lately, which may raise concerns for some users. It can take a little while to load and it’s not as intuitive as other systems.
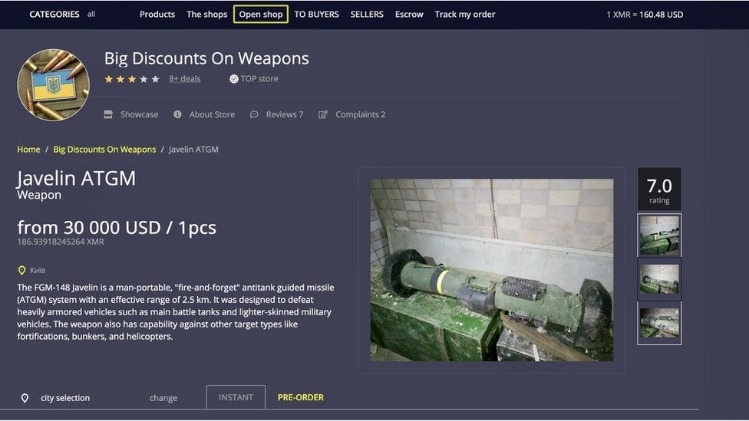
Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers. For example, a popular commerce site called Dream Market goes by the unintelligible address of “eajwlvm3z2lcca76.onion.” Browsers with the appropriate proxy can reach these sites, but others can’t. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. The experience is reminiscent of searching the web in the late 1990s.
How To Safely Access The Dark Web
Accessing the Dark Web, a part of the web that isn’t indexed by standard search engines, is not illegal in most countries. Cracking down on many illegal marketplaces on the dark web is the result of such monitoring. You might visit the dark web seeking anonymity or unique services, but this anonymity also attracts scammers. You can inadvertently download malicious software by visiting these websites, infecting your system.

How Small Businesses Can Survive AI Shopping: 7 Essential Steps
If you come across illegal activities on the Dark Web, you can report them to your local law enforcement agency or to organizations that specialize in cybercrime. Accessing the Dark Web is not illegal in most countries, but engaging in illegal activities on the Dark Web is. Additionally, it is essential to be aware of the legal and ethical considerations surrounding the Dark Web, and to report any illegal activities encountered. However, with the right knowledge and precautions, it is possible to explore this hidden part of the internet safely.
While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. The only difference is that it passes your traffic through random nodes before reaching the destination.
- Ross Ulbricht, the creator of Silk Road, was arrested on suspicion of hiring a hitman to kill six people, but the charges were later dropped.
- Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query.
- Well, as long as you don't visit sites with underaged models or that engage in human tracking or that sell drugs and other illegal items.
- Many people see hacked information and stolen card data being sold on the dark web.
- Your personal data is worth more than you think.
Combining it with VPN and good digital hygiene improves security. Tor provides strong anonymity but is not 100% foolproof. Tor encrypts your traffic and routes it through multiple volunteer-operated relays, making it difficult to trace.

Ahmia Search Engine
You will have to use specialized dark web search engines to find .onion sites. The process of onion routing takes your traffic, encrypts it, and bounces it among at least three relay points (or nodes), which makes it almost impossible to trace the source of the data. It is a free, open-source web browser that routes your internet traffic across the Tor network. Discover the tools you need—like a VPN and Tor Browser—how to stay anonymous, and what precautions to take to protect your privacy while exploring hidden .onion sites.

One option is to try DuckDuckGo’s .onion version, which is great for privacy. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. Just like Google, the dark web has some search engines present on it. If you’re lucky enough, you can find it on clearnet privacy forums. If you want to find its current links, you can search for terms like “Daniel replacement.” Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).
As discussed earlier, configuring Tor Browser’s security level is paramount for safer browsing on the dark web. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP. To mitigate these dangers, users should adopt several essential precautions before and during their browsing sessions.

With Tor, you don’t have to worry about comments coming back to haunt you, or your internet history being tracked. Since Tor is free, open-source, and decentralized, it’s accessible to all and generally resistant to corruption. Many well-known companies such as Facebook and Twitter have .onion counterparts, and Wikipedia even has an entire list of onion services. This has led to malicious relays, where bad actors register as nodes to steal user data. With Tor Browser, you’re assigned a unique browsing IP each time you open it. Tor’s data encryption attracts anyone who wants to keep their activity hidden, regardless of their motives.
Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Keep in mind that you’ve to use very specific keywords when searching. Other options include Ahmia and NotEvil, which focus on listing .onion links.
Protecting Against Malicious Software
The safest and best dark web browsing tool for Android users is the official Tor Browser APK from the Tor Project site. Use .onion URLs from reputable directories only. By disabling, you reduce such attacks’ potential (especially on untrusted websites). Understanding and knowing how to safely access this part of the internet is an important digital skill for today’s era. With the growing abilities of corporations to monitor and collect our data, the core principle upon which the dark web exists is now more relevant than ever. It forces all internet connections to go through the Tor network.



