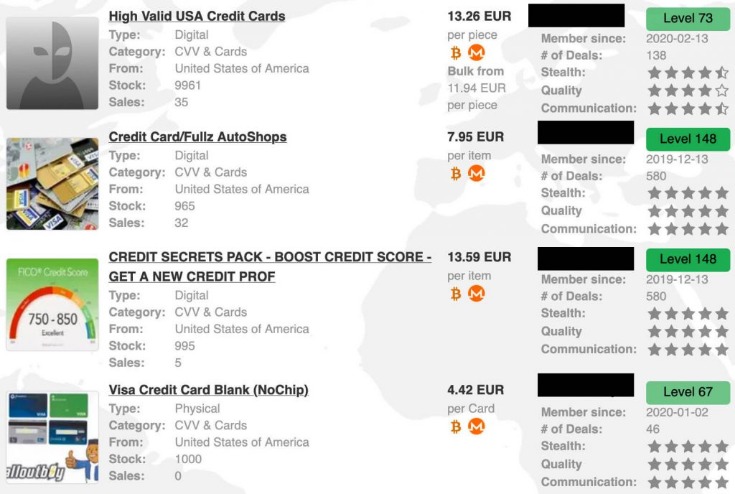
It blends illegal trade with extra features like gambling, all while maintaining a clear and accessible structure. The site is accessible via both Tor and the clear web, and its layout closely resembles that of Abacus Market, which makes navigation very user-friendly.Notable features include an automated carding shop, an escrow system for manual orders, and a dashboard that displays balances in both BTC and Canadian dollars (CAD). There are RDP accesses, SMTP logins, SSH credentials, fake pages, and even fraud tutorials. If someone wants direct access to a server, a cPanel, or an email, this is the place to go.The market is in English and features a massive catalog with over 800,000 illegal products. Each of these “bots” represents a compromised device, and prices for access range from $3 to $10, depending on the quality and freshness of the data.However, it works by invitation only and is accessed through several mirrors on the Tor network. The truth is that, despite the incident, the site is still active and constantly renewing its inventory.Thanks to its track record, loyal user base, and continuous flow of updated data, BriansClub remains a key player in the current landscape of dark web fraud.
What Are Hacking Forums
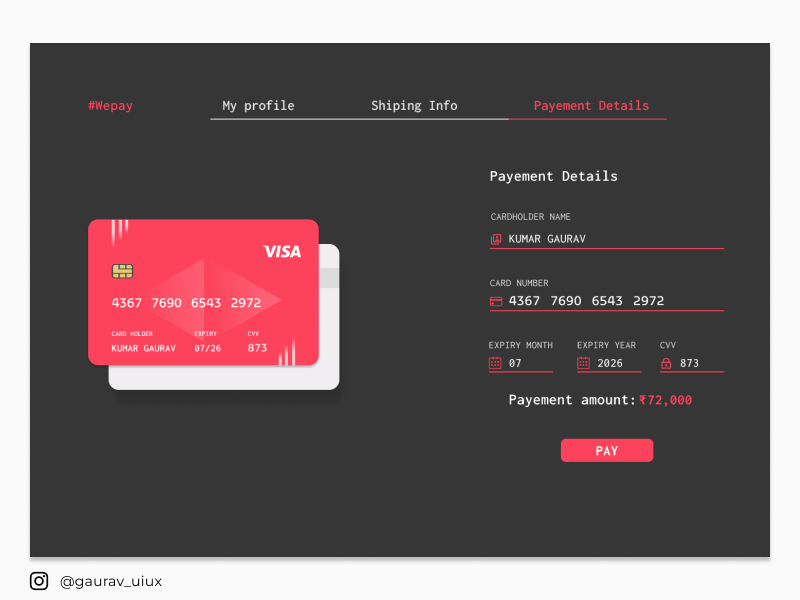
The cards were likely compromised online, using phishing, malware, or JavaScript-sniffers, which are increasingly popular among cybercriminals. Thieves often buy cards to use on specific sites that don't have security features like Verified by Visa (VBV) or MasterCard's SecureCode. Fake credit card information can be bought on the Dark Web for as little as $5. These cards can be used to make purchases online or in-store, and can even be used to withdraw cash from ATMs. Virtual cards for online shopping help too. They get the info from hacked accounts or card skimmers.
ℹ️ These cards mainly come from web skimmers! Researchers are still looking into the leak, but early reports show many of the cards could have already been reported to the card issuers. The “special event” offer was first spotted Friday by Italian security researchers at D3Lab, who monitors carding sites on the dark web. Not all the above details are available for all 1.2 million records, but most entries seen by BleepingComputer contain over 70% of the data types. The freely circulating file contains a mix of “fresh” cards expiring between 2023 and 2026 from around the world, but most entries appear to be from the United States. To ensure larger reach, the crooks distribute the collection via a clearnet domain and on other hacking and carding forums.
Underground Lookup Services
Even if a cybercriminal knew your password, MFA would prevent them from being able to log in to your account. To avoid entering your personal information into a spoofed website, it’s important to learn how to spot a site that’s been spoofed. It’s best to avoid conducting transactions while connected to an unsecured network.
Attack On Identity: Dissecting The 2025 Microsoft Digital Defense Report
This finding was consistent for the 578,524 phone numbers found in the data, of which 242,556 phone numbers had previously been seen by SpyCloud. Numbers from malware logs were even older, with some having originally been stolen in April 2018. While this duplication is not surprising, given the data was likely compiled from many different sources, it does call into question the top-line number advertised by BidenCash. Examining records by country, and excluding countries with less than 1,500 victims – as defined by the inclusion of a country-specific address within the victim’s record – data fidelity varied widely. Download Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online.
Indeed, in the last six months of 2020 alone, threat actors offered more than 45 million compromised cards for sale in underground credit-card markets monitored by security firm Cybersixgill, the company said in a report. Researchers from threat intelligence firm Cyble noticed the leak of the payment-card data during a “routine monitoring of cybercrime and Dark Web marketplaces,” researchers said in a post published over the weekend. Notably, while significant overlap existed between credit card numbers identified in public breaches, the additional records existed for email addresses which did not correspond to the credit cards listed in the breach. Expressed longitudinally, the majority of the credit cards were leaked between July and August of 2021, with smaller exposures occurring between April and May of 2022. On Sunday, underground carding marketplace BidenCash made available for free download a file which purported to contain approximately 1.2 million credit cards. Add your credit card number (along other personal details like email address, phone number, etc.) to the monitoring list.
What Are Ransomware Leak Sites
Not to mention that anonymity safeguards won’t protect you from other threats like hacking and malware. LifeLock notifies you if we find your personal information on the dark web, and we’ll help you run damage control with assistance from legal experts and recovery specialists. This hides your activity and personal identifiers so you can browse safely, protected from prying eyes and identity theft. Some popular search engines that can help you explore hidden content and anonymize your web traffic include DuckDuckGo and Ahmia. You can also update permissions to enhance your privacy and keep cybercriminals from accessing your device’s camera, microphone, or location. Accessing content on the dark web takes a few extra steps, but it’s not as hard as you might think.
- The increase is partly been driven by the increasing popularity of JavaScript-sniffers (AKA Magecart), which enable their operators to steal payment card data from e-commerce websites.
- Today we are one of the largest cards/dumps marketplaces.”
- There are some dark web monitoring services that include financial checks, but these are mostly subscription based.
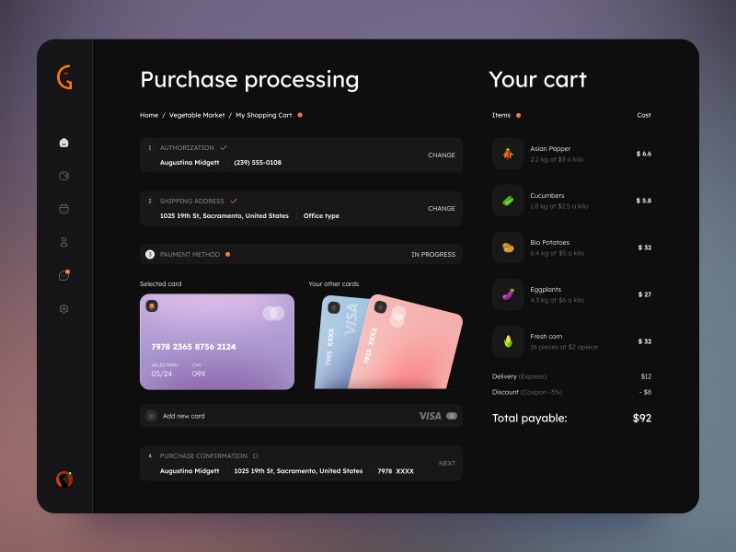
- When using credit cards on the dark web, it is vital to use a secure payment method to minimize the risk of fraud.
- They’ll stop the card and send a new one.
- Additionally, fraudulent charges can lead to overdraft fees, late payment penalties, and damage to credit scores.
Responding To Detected Credit Card Fraud

The link between credit cards and the Dark Web is fueled by a complex network of cybercriminals, who exploit vulnerabilities to obtain and sell stolen credit card details. The Dark Web has become a thriving marketplace for stolen credit card information, posing a significant threat to users' financial security. While credit cards have undoubtedly revolutionized the way we make payments, they too have fallen prey to the nefarious activities that thrive in the depths of this digital underworld.
When a victim falls for a card skimmer and inserts or swipes their card, their card gets scanned and the card information is sent to the threat actor through Bluetooth. To use these devices, threat actors attach them to actual card readers like the ones used in ATMs and at gas stations. Accounts are often compromised due to weak password practices like using short passwords or reusing passwords across multiple accounts. Public data breaches occur when a company you have an account with or work for experiences a breach that exposes customer and employee Personally Identifiable Information (PII). Our platform alerts security teams when an organization’s sensitive data is found. Breachsense monitors the dark web, Telegram channels, hacker forums, and paste sites for external threats to your organization.
- This gives security teams time to adjust their defenses before new techniques become widespread.
- Of course, cybercriminals can also use them for nefarious purposes like discussing illegally shared interests, conspiring to commit crimes, or posting content deemed too unsavory for the clear web.
- Protecting personal information and ensuring online security should always be a top priority.
- Other sellers offer discounts for buying multiple cards, while the cheapest card — with between US$700 and US$1,000 on it — can cost as little as US$80.
- In Q1 2023, Resecurity observed a significant spike in interest from bad actors seeking these tools, as well as the emergence of new fingerprint spoofing and anti-detect products on the Dark Web.
Warning For Would-Be Fraudsters
By using alternative payment methods, you reduce the risk of unauthorized charges or potential identity theft. Look for indications that the vendor has been active for a significant period of time and has a track record of successful transactions. Use pseudonyms or aliases to conceal your real identity and avoid using any personal information that can be traced back to you. This ensures that your conversations and personal information remain confidential and protected from interception by malicious actors. Utilize a reputable virtual private network (VPN) to encrypt your internet traffic and mask your IP address, providing an additional layer of anonymity and security. When engaging in any transaction, it is essential to take protective measures and precautions to safeguard personal information and privacy.
These platforms are hubs for cybercriminals to buy and sell compromised payment card details. These groups often originate from leaked credit card credentials, which have become a common phenomenon, particularly in the past months. Telegram carding groups have become a significant threat in the cybercriminal community, with tens of thousands of members easily accessible through the chat application. These checkers are often offered and sold on the dark web, and are complimentary tools that individuals and organizations use to verify credit card information. Such type of data is likely to have been compromised online, making it a red flag for would-be fraudsters. The three suspects from Indonesia confessed to stealing payment card data using the GetBilling JS-sniffer family.

Established vendors with a track record of successful transactions are more likely to be reliable. Reliable marketplaces often have a system in place to rate and review vendors, providing valuable insights into their trustworthiness and the quality of their products. Engaging in such activities may result in serious legal consequences.

Depending on the type of account a cybercriminal compromises, they can gain access to many types of personal information, including your credit card information. Compromised online accounts can also lead to your credit card information being published on the dark web. Discover the pros and cons of using credit cards or card for purchases, including benefits and risks, to make informed financial decisions. Stolen credit cards are often used to make purchases at specific sites that don't have protections against fraud. Card data is a hot commodity on the dark web, with credit card details and cloned cards being sold to cybercriminals.
This threat actor’s services support multiple geographies, including the Middle East, and the European Union (EU). “Slava044” aka “egg_nfc” is one of the more sophisticated cash-out vendors identified by Resecurity. Some of these threat actors use more sophisticated techniques, including their own merchant terminal and NFC-enabled processing systems . In response to heightened Zelle fraud, the Federal Reserve has proposed new anti-fraud tools to enhance consumer protection . Notably, the commission on processing stolen funds from VCC is significantly higher compared to ACH/WIRE transfers. The Verta service is accessible via Telegram and Jabber, following the initial vetting of cybercriminal customers.
Free and paid tutorials on the dark web teach fledgling criminals how to use stolen credit cards. Some threat actors offer a "complete package" known as "Fullz", which includes full personal details and financial information like bank account details or social security numbers. Dark Web credit cards can be a nightmare for victims, often leaving them with significant financial losses and damaged credit scores. Dark web credit card numbers are stolen card details sold on hidden online markets.



