Data from relational databases may consist of one or multiple CSV files, depending on the source database structure.A performant approach is to run multiple passes of LOAD CSV to import nodes separately from relationships. Cypher is Neo4j’s declarative graph query language.It was created in 2011 by Neo4j engineers as an SQL-equivalent language for graph databases.Similar to SQL, Cypher lets users focus on what to retrieve from graph, rather than how to retrieve it.As such, Cypher enables users to realize the full potential of their property graph databases by allowing for efficient and expressive queries that reveal previously unknown data connections and clusters. The prescribed property existence and datatypes for nodes and relationships.

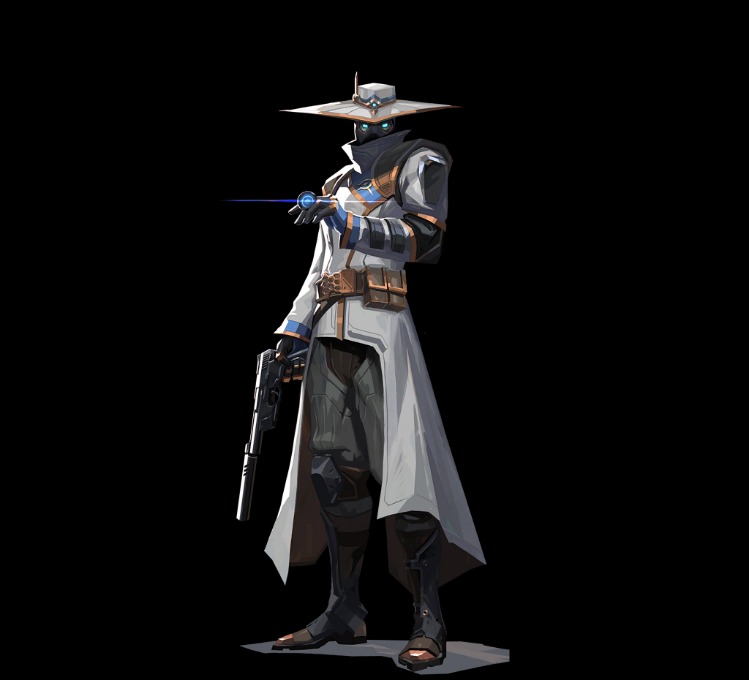
About Cypher Market
The feature is triggered by either merging a PR with the cherry-pick label or by adding the cherry-pick label to an already closed and merged PR.In the latter case, ensure that you first add the labels containing the target branches and then finally the cherry-pick label.Otherwise the automation starts without any target branches. When curl connects to a TLS server, it negotiates how to speak the protocoland that negotiation involves several parameters and variables that bothparties need to agree to. A web app for modular conversion, encoding, and encryption, all performed directly in your browser with no server interaction. The cipher itself is not causing any significant data expansion.

Cypher Syntax
Cypher’s easy-to-learn pattern constructs make it accessible for developers, data scientists, and those with limited query language experience. Created by Neo4j, Cypher provides expressive and efficient queries for property graphs. Cypher is a declarative graph query language that is used by developers worldwide. A node represents an entity or discrete object in your graph data model. If you are familiar with NoSQL ("Not only SQL") system, you can also learn more on how to make the transition to a graph database.
Your Go-To Tools For Online Safety
A middleware application between the client and the server could log every domain that are requested by a client. According to Cloudflare, the server name indication (SNI aka the hostname) can be encrypted thanks to TLS v1.3. Note that when you use a HTTP Proxy, it knows the address (domain) of the target server, but doesn't know the requested path on this server (i.e. request and response are always encrypted). It may be desirable forclients to provide this information to facilitate secureconnections to servers that host multiple 'virtual' servers at asingle underlying network address. TLS does not provide a mechanism for a client to tell a serverthe name of the server it is contacting.
Want To Schedule A Consultation With A Neo4j Expert?
- That's why client has to enumerate ciphers to be able to find those supported by server and for that to do at least one new start handshake (ClientHello) for each cipher suite.
- For mobile apps, if you control both ends of the application (server and app), as long as you use HTTPS you're secure.
- Following is an example that demonstrates how easy it is to use Cypher using two simple datasets, TMDB (Movies) and Northwind (Retail).
- We'll also include examples of common use cases for Cypher, such as querying social networks or e-commerce databases.
- Using the neo4j-core Gem, we can talk to Neo4j Server or embedded (using jRuby) by just changing a single line of configuration.
First, download the ssl-enum-ciphers.nse nmap script (explanation here). GregS points out below that the SSL server picks from the cipher suites of the client. Cypher is an extensive query language with lots of features, and this cheat sheet is a great starting point for mastering them. This query will calculate the rank of every node, order them from highest to lowest and return the first 10 results.
Import Local FilesNot Available On Aura
However, complex encryption methods or custom codes will require knowledge of the original encoding method and any keys or shift values used. While it's possible to decode some messages through trial and error, having the original encryption method makes the process much more accurate and efficient. Then choose your preferred encoding method – common options include Caesar cipher, substitution cipher, or custom letter mapping. The variety of encoding options keeps things fresh, and it's really helped spark interest in cryptography among our members. It's incredibly versatile with multiple cipher options, and I love how quickly I can switch between encoding and decoding.
Available Commands
Regularly the database is updated and new ciphers are added which allows to refine the results. This structure allows the program to detect subtle patterns in data, improve its accuracy, and adapt to different types of encryption more effectively. To decrypt / decipher an encoded message, it is necessary to know the encryption used (or the encoding method, or the implemented cryptographic principle). Tool to identify/recognize the type of encryption/encoding applied to a message (more 200 ciphers/codes are detectable). If you want to determine all suites supported by a particular server, start by invoking openssl ciphers ALL to obtain a list of all suites supported by your version of OpenSSL. You can also go through our Cypher lessons on Memgraph Playground, an online platform for running Cypher queries on live data.

Choose your preferred encoding method from options like Caesar cipher, shifted alphabet, or custom letter substitution. Following is an example that demonstrates how easy it is to use Cypher using two simple datasets, TMDB (Movies) and Northwind (Retail). Compare this Cypher query to its equivalent in SQL.

It will pad the data to be a multiple of the block length, but that is insignificant in your case. If size matters I would recommend to compress the data before encrypting it. As others have mentioned, the only real answer is to reduce the size of the data you are encrypting so that you need to encode less data. That's why this isn't a feature of any encryption algorithm.
No single SSL/TLS library supports all cipher suites, and that makes comprehensive testing difficult. Then submit them to the server one by one to test them individually. For an exhaustive overview of available tools see sslLabs Assessment Tools.
We'll also include examples of common use cases for Cypher, such as querying social networks or e-commerce databases. If you're new to graph databases and Cypher, this blog post is for you. Though both examples above are accepted by the interpreter, they are not equivalent and refer to two different types of Nodes/Relationships, and node properties follow this same logic. Let’s start at the highest level with an overview of the structure of a graph database composed of Nodes and the Relationships between them. For example, several Nodes with the Label ‘Person’ can have completely different properties of different data types.
Over time, security researchersfigure out flaws and weaknesses in existing ciphers and they are graduallyphased out over time. It is often used in the submission of HTML form data in HTTP requests. You might try compressing the input prior to encryption.
Transform your data into knowledge to build smart, accurate, and adaptive applications. Click below to get your free copy of O’Reilly’s Graph Databases ebook and start building better apps powered by graph technologies. Accessing web-APIs is a simple task in all stacks and languages and JSON as transport format is ubiquitous. Using the neo4j-core Gem, we can talk to Neo4j Server or embedded (using jRuby) by just changing a single line of configuration. For JavaScript I want to show how to call the transactional Cypher endpoint directly, by just using the request node module. To pass in the JSON to Cypher we have to programmatically call the Cypher endpoint of the Neo4j server, which can be done via one of the many drivers for Neo4j or manually by POSTing the necessary payload to Neo4j.
- If you try to import a file that doesn’t use , as field delimiter and you also don’t specify a custom delimiter, LOAD CSV will interpret the CSV as having a single column.
- (Either that or don't put the data in url's in the first place e.g. store the data in a database and put a unique id in the url).
- I want to show here that retrieving that data and ingesting it into Neo4j using Cypher is really straightforward and takes only little effort.
- This makes it a great choice for developers who need to work with complex data structures but don't want to spend a lot of time writing complex SQL queries.
- For a list of type casting functions, see Casting data values.
- Cypher supports a wide range of filtering and aggregation functions, allowing you to work with your data in a flexible way.
It also offers a basic evaluation of offered ciphers and protocols. You'll never need an old OpenSSL version, though, since the cipher suite scan is in pure Python. It's a fast, pure-Python library/CLI application that enumerates cipher suites and groups by making its own TLS handshake packets. I am not aware of a tool to do this, though it should not be hard to cobble one together from scripting tools and openssl s_client. SSLScan is great; a new tool SSLDiagnos works for Windows, or you can just write a script using the openssl s_client. It actually can’t negotiate even a single suite, but just proposing to negotiate is enough for servers to tell you if they support a suite or not.



