This controlled access connects users directly with a network of trusted sellers who have built their reputations...
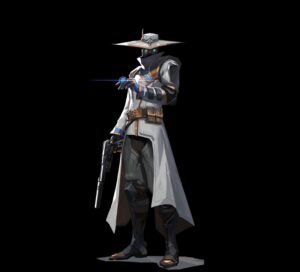
cypher
Data from relational databases may consist of one or multiple CSV files, depending on the source database...
The official list of these mirrors is typically accessible from the main site itself once a user...
The point() Cartesian 3D function returns a 3D POINT in the Cartesian CRS corresponding to the given...
User verification on platforms like the Nexus darknet market functions as a critical security layer, establishing a...