Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. This means your activities cannot be traced or your browser history exposed. Since the internet is open to everyone, there is no privacy. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web.
The New York Times
“I remember looking around the room, and there wasn’t a dry eye,” said Ms. Kozakiewicz, 31, who had told of being chained, raped and beaten while her kidnapper live-streamed the abuse on the internet. With so many reports of the abuse coming their way, law enforcement agencies across the country said they were often besieged. Many of the survivors and their families said their view of humanity had been inextricably changed by the crimes themselves and the online demand for images of them.
Subscribe To Our Newsletter!
It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services. The process costs a fee, but unlike other "tumbler" or "mixing" services, there is no risk that Wasabi or any of its users could scam you out of your coins. Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to "join" your transactions with others to increase your anonymity. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017.
Project Uses Online Games To Help Stroke Recovery
- Not being identifiable on the Internet’s regular search engines, the darknet provides security to these forums through obscurity.
- The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
- Rescues involving live streaming commercial sexual exploitation of children by parents often require a separation of the minors from the families and new lives for them in a shelter.
- Apart from having that “As above, so below” vibe, Tunnels is a great source of info for users who are into dark urban history.
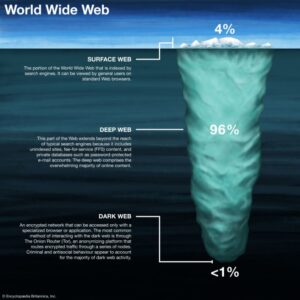
- The open web (also known as the surface web) is the part of the internet that’s easily accessible to all users.
- Shehan told Ars that “NCMEC has received at least a dozen CyberTipline reports submitted by companies regarding individuals attempting to upload known CSAM” into AI image generators to influence the kind of content that can be created.
You could try to visit a major site like Facebook’s onion site to check if your browser is working at all. This method is called Tor over VPN, and it’s a great way to increase your privacy over using Tor alone. As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law. Naturally, this makes the dark web a breeding ground for illegal activity. With the above dangers, it’s imperative to tread carefully as you step into the dark web.
We analyse search queries from a well-known public search engine for onion websites. According to this keyword-based basic search with the stated false positive and false negative estimation, 18.5% of unique websites hosted through the Tor network share CSAM in December 2022. We execute the search against the content of these distinct websites. Project evaluation shows that post-treatment recidivism is lower among individuals who commit contact offences as opposed to child sexual abuse material users.
Legitimate Use Cases For The Average User
Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. Take a look at the sites that these directories have collected and see what topics interest you. Do not explore random links to websites you aren't aware of or familiar with. Only visit trusted websites with URLs that are maintained by a trusted source.

First, Install A Reliable VPN

“Memex helps us build evidence-based prosecutions, which are essential to fighting human trafficking,” says Manhattan District Attorney Cyrus R. Vance, Jr. “In these complex cases prosecutors cannot rely on traumatized victims alone to testify. The NYDA says that its new Human Trafficking Response Unit now uses DARPA’s Memex search tool in every human trafficking case it pursues. Search resultsThe technology has already delivered results since DARPA began introducing Memex to select law enforcement agencies about a year ago. White also showed how MEMEX can generate color-coded heat maps of different countries that locate where the most sex advertisements are being posted online at any given time. Just as important as Memex’s ability to pull information from a broader swath of the Internet are its tools that can identify relationships among different pieces of data.

We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives. In a world of bulk data collection, surveillance, and personalized ad tracking, it's up to us to take control of our personal privacy. If you see inaccuracies in our content, please report the mistake via this form.
Using the ProtonMail .onion site offers security and privacy advantages. However, note that the site only uses non-sensitive and public data for the metrics. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. For example, the BBC website is not accessible in such countries.
Artificial Intelligence (AI) And The Production Of Child Sexual Abuse Imagery
“We don’t know how much content is out there,” says Fred Langford, the charity’s deputy CEO. “In the past two months, we have seen an escalation in the type of content being shared on social media platforms, which became much more explicit than what we used to see in the past,” Paltieli told Ars. Paltieli said one result of companies moving too slowly to solve the growing problem is the recent appearance of even more explicit AI-generated images. Already his team is seeing “content migrating from dark web forums to the clear net,” finding “numerous examples” on “mainstream social media platforms.”
But law enforcement officials aren’t the only ones working on finding better solutions to this problem. A 61-year-old Quebec man, Steven Larouche, was sentenced to more than three years in prison after being charged with creating AI-generated child pornography, CBC News reported. Stability AI, which created Stable Diffusion, doesn’t record all Stable Diffusion images like other AI tools like Midjourney and DALL-E do, The Post reported. “This leaves them vulnerable to embarrassment, harassment, extortion, financial loss, or continued long-term re-victimization.” “Once circulated, victims can face significant challenges in preventing the continual sharing of the manipulated content or removal from the Internet,” the FBI’s alert said. The agency blamed recent technology advancements for the surge in malicious deepfakes because AI tools like Stable Diffusion, Midjourney, and DALL-E can be used to generate realistic images based on simple text prompts.
Find The onion Address You Want To Access
The dark web is a part of the deep web that is hidden and inaccessible through conventional means on purpose so that criminal activities can be carried out without tracing. Furthermore, it can oftentimes be possible that you accidentally engage in criminal activity when accessing the dark web without your knowledge or intent. However, engaging in illegal activities on the dark web can result in investigations, charges, and penalties from the justice system. No, it is not illegal to use the dark web as long as you are not using it to engage in illegal activities. The dark web is full of normal chat rooms and can also be a safe and anonymous place for a journalist to break a story. However, not all of the activities that take place on the dark web are illegal.
- ’ campaign demonstrates the high effectiveness of the public health approach in preventing child sexual abuse.
- "Most of the hidden services we only saw once. They do not tend to exist for a very long time," he said during a speech at the 31st Chaos Communications Congress in Hanover, where he presented his findings.
- This “explosion” of “disturbingly” realistic images could help normalize child sexual exploitation, lure more children into harm’s way, and make it harder for law enforcement to find actual children being harmed, experts told the Post.
- Online predators create and share the illegal material, which is increasingly cloaked by technology.
This platform’s library of websites currently totals 50, which may not sound impressive until you consider that all the links are active and popular. Sci-hub has more than 80 million research documents, and more than 80% of the database contains journal research articles. Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall.
Deep Web Vs Dark Web Vs Surface Web
The FBI obtained records from Google that showed Ulbricht was accessing his Gmail account from San Francisco; the server through which Roberts accessed Silk Road showed an IP address corresponding to a San Francisco café. His Google+ account linked to some of the same sites and videos–including some from the Ludwig von Mises Institute–that the Dread Pirate Roberts mentioned. “It was basically an open thumbing of noses at law enforcement,” Bharara says. “A lot of people answered ‘came for the drugs, stayed for the revolution.'” Dread Pirate Roberts, or simply DPR, was hailed by Silk Road customers as an antiestablishment hero.
Moreover, given the nefarious nature of the dark web, some government agencies may set up Tor gateways to monitor what’s happening on the dark web. We also recommend using a virtual private network (VPN) such as NordVPN — the best dark web VPN — to add an extra layer of protection. If you’re intrigued and want a firsthand experience, follow this guide to learn how to access the deep web with an anonymizing browser. The hidden web (also known as the deep web or deep net) is the largest part of the internet. Dark web encryption allows website owners and users to stay completely anonymous during their engagement. He has also contributed to platforms like Financesonline.com and Timeero.com.