On top of a booming trade on the open web, new research has identified hundreds of species traded on the dark web, including the Sonoran desert toad (Incilius alvarius). Alas, the internet has allowed this trade to flourish more easily than ever. Amid the human-driven ecological unraveling, the illegal wildlife trade poses one of the greatest threats to many species' continued existence.
Separate Your Real Life From Your Online Persona
Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. To expand their reach, some marketplaces established parallel channels on Telegram. Regularly monitoring the top dark web markets gives your SOC team an insider’s view of the latest malware and phishing kit trends, plus real-time knowledge related to relevant compromised PII.
What Exactly Is Sold On These Marketplaces?
How do law enforcement agencies trace criminals on the dark web if everything is anonymous? What are initial access brokers IABs on the dark web? How can I tell if my personal data is on the dark web? Mohammed’s work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors. Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations.
For instance, a factory employee can secretly slip away with one and sell it on the darknet markets. Nevertheless, most of the items in the darknet markets are illegal or heavily regulated. Therefore, it’s almost impossible for authorities to track those who run the darknet markets or even their locations.
Sometimes branded 2easy.shop, this site has become known as the budget marketplace for stolen logs. STYX is a great example of a ‘new model’ market with a searchable structure and trusted vendor processes, which helps buyers quickly filter for fresh data. Torzon is one of the largest general-purpose darknet markets still active in 2025. For example, people like journalists, activists, and academics use it for cybersecurity or research, to access information in regulated countries, and for anonymous whistleblowing.
After AlphaBay’s shutdown, many users migrated to Hansa, unaware it was under surveillance. However, its rapid growth attracted law enforcement attention, and it was seized in 2017. Pros included a robust search system, responsive customer support, and a reputation-based vendor rating system. This study reveals that Bitcoin isn’t just a payment method; it’s the lifeline of the dark web economy. That’s why users often rely on mixers, privacy wallets, and other tools to make their transactions harder to follow.

What You Can Buy On The Darknet Markets
To access them, you need to use special browsers like Tor, which allow you to browse anonymously. We’re back with another video in our Webz Insider video series on everything web data. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. By submitting you agree to Webz.io's Privacy Policy and further marketing communications. Freshtools has some characteristics that help it stand out from the other dark web stores.
Vendor Profiles And Reputation Systems

I tested all the website links on The Hidden Wiki and almost all of them work (I was able to access sites like Deep Web Radio and ProPublica without any issues). The Hidden Wiki is the best way to start browsing the dark web because it contains dozens of links to popular .onion sites. I also included instructions on how to access the dark web, and outlined how to stay safe when browsing dark web links (the dark web is also home to many scams and malicious sites).
It also masks your IP address, making it difficult for government agencies to monitor or track your activities. A VPN encrypts the data traffic and keeps your activities private on the dark web. The layers of encryption hide your data and activity from snooping eyes.
Marketplaces For Everything Illegal
- Dark web shops sell a wide variety of illegal goods and services.
- The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web.
- Brian’s Club is one of the biggest hacker carding communities online because it is frequently updated, and the dumps are high quality.
- Torch is one of the oldest dark web search engines, and it’s generally considered one of the safest.
- People increase the value of the stolen data by aggregating it with publicly available data, and sell it again for a profit, increasing the damage that can be done to the people whose data was stolen.
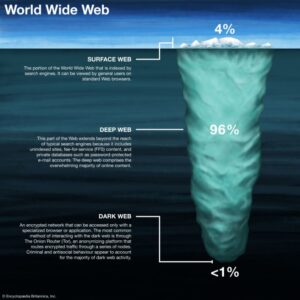
You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. It is easily accessible by the general public and requires no special configuration. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. Everything you find on the dark web is not necessarily illegal.
Quick Links
It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web. With enhanced security features and a strong focus on financial fraud, STYX has become a go-to marketplace for those looking to engage in cybercrime on a more technical level Looking for a way to track all of the new marketplaces that seem to pop up overnight?
What Is Dark Web Monitoring, And How Does It Work?
Many sites specialize in selling illegal goods that are not readily available on the public internet. The dark web is a collection of sites that are not indexed by search engines and can only be viewed with specialized web browsers designed to provide privacy and anonymity. Dark web search engines have become essential for enterprise security teams that need early … …More about Dark Web Search Engines in 2025 – Enterprise Monitoring, APIs and IOC Hunting For cybersecurity professionals, focusing on payment methods, vendor migration, and marketplace specialisation offers the most effective path to actionable intelligence.
Your online activity and communicationsremain private and secret on the dark web. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows.
Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. Of all listings (excluding those selling drugs), 60% could potentially harm enterprises.
Dell Customer Data Breach (
Staying safe on the dark web requires even more vigilance than the public internet. It’s also a playground for cybercriminals, illegal activities, and shady stuff. Only use .onion links that come from legitimate sources like The Hidden Wiki. In addition to these tools, you need to exercise extreme caution when browsing on the dark web because there are tons of phishing and malicious sites on there.