Hence, you never know when a popular .onion site is going to vanish, or even die. The US Navy’s main reason for creating Tor was to help informants relay information safely over the internet. This .onion link makes it impossible for hackers to impersonate your profile.
Threat Actor Claims Sale Of State Grid Corporation Of China (SGCC) Data, World’s Largest Utility Company
The dark web is most commonly accessed using the tor security suite and the tails flash bootable operating system The dark web is a network of websites and servers that use encryption to obscure traffic The threat actor shared samples of the compromised data, which appears to contain a vast amount of sensitive user and operational information. A threat actor has allegedly put a database containing 2 million lines of data belonging to Helity Copter Airlines up for sale on a dark web forum.
In fact, there are growing concerns about law enforcement monitoring what is happening on the dark web. Government authorities across the globe are taking over many Tor-based sites. Some services are genuine; you can get what you want at an agreed fee. Many services that are allegedly offered on the dark web are scams. Here are some of the common dark web dangers that users can face. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals.
This is because law enforcement often actively monitors these sites. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. The threat can extend to your entire network of devices connected to the internet. For example, China uses the Great Firewall to block access to Western sites.
RiseUp — A Secure Email And Chat Platform For Activists
Its free plan comes with up to 1 GB of storage, 150 messages per day, and 1 email address. It’s based in a privacy-friendly country (Switzerland), and all of its apps are open source, meaning anyone can inspect the code for security vulnerabilities The articles are in-depth and informative, and the site is completely free to access — no random paywalls pop up in the middle of articles. In addition, Darknetlive has a list of dark web vendors, which is very convenient — it offers detailed information about each vendor, including .onion addresses (in alphabetical order) and FAQs.
Best Privacy Protection Apps For Ultimate Anonymity And Security
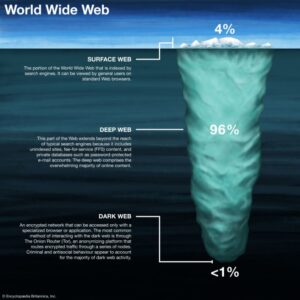
Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. As a result, you cannot find them with a regular search engine.
Onion Links: How To Access Them
Alongside drug trafficking, the dark web has also served as a key channel for other criminal activities, such as child pornography distribution. The research also highlights that drug traffickers rely on underground platforms to acquire synthetic opioids from Asia, demonstrating a sophisticated use of this technology to expand their international operations. Some experts have even referred to this phenomenon as a form of “deviant globalization,” where criminal actors transcend borders and local regulations. Within this environment, platforms similar to conventional e-commerce marketplaces enable the proliferation of criminal networks that exploit anonymity and decentralization to operate without restrictions. The lack of specialized resources and limited awareness of the risks inherent to this environment have left governments in a vulnerable position against the threats lurking in the shadows of the internet.

Spanish Insurer Pelayo Seguros Allegedly Breached – Database Of 15 Million Users For Sale
Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. It is the dark web’s version of Wikipedia with a massive links directory. It will offer you an additional layer of encryption to access the deep parts of the internet. You can also use it within the dark web, as it has .onion links.
I tested all the website links on The Hidden Wiki and almost all of them work (I was able to access sites like Deep Web Radio and ProPublica without any issues). The Hidden Wiki is the best way to start browsing the dark web because it contains dozens of links to popular .onion sites. I also included instructions on how to access the dark web, and outlined how to stay safe when browsing dark web links (the dark web is also home to many scams and malicious sites). You can also use the dark web to access clearnet (publicly accessible internet) sites securely, and to visit sites that aren’t available on the public internet. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage.
- For example, it has a reputation for hosting pedophile sites.
- Data gleaned from ransomware and data breaches is available on the dark web.
- MacOS users will need to drag and drop the Tor Browser icon to the Applications folder.
- Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic.
What To Do If You See Something Illegal
Taking the necessary precautions makes tracing your activities on the dark web difficult. Also, try its services risk-free with the 30-day money-back guarantee. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. All the plans come with a 30-day money-back guarantee, so you can try the services risk-free.

Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. It is possible to navigate the dark web even though it doesn’t host user-friendly onion search engines. This article lists some of the best dark web websites you can visit securely. Detractors argue that online anonymity encourages criminality and impedes law enforcement. The U.S. government’s Naval Research Laboratory developed Tor for members of the U.S. intelligence community to use the Internet without risk of identification.
Once you upload an image, the site provides you with shareable links for email messages, instant messaging, message boards, and websites. You can also use its .onion link via the Tor network to access the site in restrictive countries, where it might be unavailable. It has indexed more than 1.5 billion pages from over 260,000 .onion websites, so you’ll easily be able to find what you’re looking for. DuckDuckGo also lets you access chatbots anonymously, has image, video, news, shopping, and other search options. Essentially, it’s a search engine like Google or Safari, but unlike other search engines, it doesn’t track your browsing activity or collect user data. Ahmia is a search engine for .onion sites — you search for a keyword and Ahmia retrieves relevant results.
A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. This means that there will be no data to track your activities. It uses TrustedServer technology on the entire server network to wipe out your data after every session.
However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. Do you want to access the Onion sites with multiple devices? It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. This is high-level protection; no one can intercept your data or activities.

Don’t Provide Personal Information
Users could exchange funds online without sharing credit card numbers or other identifying information. The rise of cryptocurrency, and in particular Bitcoin, significantly increased the dark web’s use in illegal trade. The term dark web first appeared in print in a 2009 newspaper article describing these criminal applications. As hoped, the Tor anonymous network grew in popularity among computer enthusiasts, privacy advocates, journalists, dissidents under repressive governments, and others desirous of strict secrecy. Our editors will review what you’ve submitted and determine whether to revise the article. We're part of Translated, so if you ever need professional translation services, then go checkout our main site
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The system is designed to provide enhanced security and privacy features. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.

How To Access onion Sites Safely
In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. The users only have access to a fraction of the available data and web pages.
Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That means that Google wants to minimize the amount of time users spend searching for certain queries. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. The deep web is made up of content that search engines such as Google do not index. Did you know that Google only shows you a glimpse of all the websites that actually exist?