You’ll know you’re on the dark web when the URLs end in “.onion” — these addresses only work inside the Tor network. The deep web refers to anything that search engines can’t crawl.1 These pages aren’t public — not because they’re illegal, but because they require a login or special access. By patronizing sites or marketplaces that facilitate these things, you may be inadvertently supporting these illegal activities and contributing to the harm caused by them. It encrypts your traffic, making it nearly impossible for anyone to intercept or monitor your online activity. Accessing the dark web requires a special browser and the use of a virtual private network (VPN) to keep your online activity private and secure. You’ll need directories and search engines designed for .onion domains.
How To Access The Dark Web – A Step-by-Step Guide

As well as attracting cybercriminals who use the anonymity it provides to offer hacking and phishing services, the dark web is awash with illicit forums, malware, and other potentially dangerous content. You can access the dark web quickly and easily using Tor Browser, which is specifically designed to anonymize web traffic by routing your data through multiple encrypted server “nodes,” which helps provide secure access to the dark web. Without a VPN, your ISP or network administrator may be able to detect, monitor, or block dark web access; Tor-over-VPN provides an extra layer of privacy. The dark web is a murky part of the internet that isn't accessible via a normal browser — and can be dangerous to visit if you don’t know what you’re doing.
Yes, Tor Browser is available for Android via the Google Play Store and F-Droid. Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script. Combining both provides extra security. Tor anonymizes by bouncing traffic through relays; VPN encrypts and routes through a single server. It disables JavaScript and other potentially risky web features for maximum security. Combining it with VPN and good digital hygiene improves security.
Where Can I Find Safe Onion Links?
You can use search engines like DuckDuckGo or Torch to find the websites you want. Dark web websites have URLs that end in .onion, which usually consist of a 32-characters sequence of random letters and numbers. You will have to use specialized dark web search engines to find .onion sites. In most places, you do not do anything illegal by merely accessing the dark web. The process of onion routing takes your traffic, encrypts it, and bounces it among at least three relay points (or nodes), which makes it almost impossible to trace the source of the data. It is a free, open-source web browser that routes your internet traffic across the Tor network.
How To Access The Dark Web Using The Tor Browser
There are plenty of malware actors waiting for someone to be curious and wander around aimlessly. If you’re thinking of connecting to the dark web for the first time, here are some steps to ensure that you don’t fall into malicious hands or legal trouble. You need to have an onion website link to copy/paste into your Tor browser. Other dark web aggregate or searchable indexes would be Not Evil, Torch, Haystack, and Ahmia.
- Go to the directory where you downloaded the Tor Browser installation file.
- While this doesn’t tell the exit node what your original IP address or your geographical location is, it could spy on your activity if the website you’re visiting isn’t a secured HTTPS website.
- As well as attracting cybercriminals who use the anonymity it provides to offer hacking and phishing services, the dark web is awash with illicit forums, malware, and other potentially dangerous content.
- Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they're doing and what they're looking for.
That could make them suspicious about what you’re doing. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. As I mentioned previously, using the Tor Browser will slow down your browsing. While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser. Also, since the Tor Browser is based on the Mozilla Firefox platform, it’s susceptible to the same attacks that other browsers are.
- They’re part of the internet, but hidden from public search.
- Second, it allows you to access websites or services that block Tor but accept VPN traffic, such as streaming or banking sites.
- Without a VPN, your ISP can see that you’re using Tor, and the first Tor server (entry node) can see your real IP address.
- The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not.
- The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software (such as the Tor Browser), configurations, and authorization to access.
Safe Dark Web Access: Best Practices
We’ve already mentioned the importance of using a VPN and a browser like Tor Browser when accessing the dark web. It’s up to each individual to weigh the potential benefits and risks of accessing the dark web and decide for themselves whether the risk is worth the reward for them. It is simply a different section of the internet that is harder to access and less regulated. Unlike other search engines, Duck Duck Go does not track your activity or store your personal information. Use caution when accessing dark web pages and never give out personal information or download anything suspicious. The Tor browser uses the Tor network to bounce your traffic through multiple servers around the world, making it virtually impossible for anyone to track your activity.
Is It Illegal To Use The Tor Browser?
Fake sites are everywhere, and even a one-character difference in the URL can land you on a phishing page. Screen dimensions are a known fingerprinting vector. Avoid changing default settings unless you know exactly what you’re doing. Before you start browsing, open the shield icon in Tor’s toolbar and set the Security Level to ‘Safer’.
Accessing The Dark Web On Various Devices
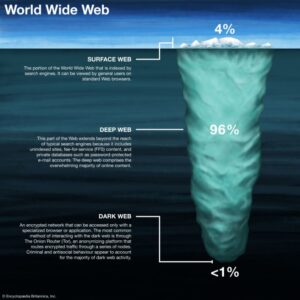
Also, your data is more likely on the deep internet in one way or the other. In this digital age, your data could be anywhere on the internet, meaning it could already be at the three internet levels (surface web, deep web, and dark web). Your Internet Service Provider will see everything when your online data is not encrypted. It means that unless you use a VPN that encrypts your internet traffic, they always receive all information about you and your digital life. Tor Bridges or a VPN will help you to use Tor privately, as your ISP (Internet Service Provider) will not see that you’re connected to a Tor node. While a website can’t identify you or an ISP can’t decrypt your internet traffic; still, they can still see you using Tor, which can draw some unwanted attention and raise suspicions.
With all this data, your ISP could create a very accurate profile of you and link it to your IP address. Sometimes, they even know more than you would like about private matters, such as your health or finances. So, if you aspire to use Tor privately, you can use VPN or Tor gateways (Tor nodes that are not publicly indexed).
Tor has an in-build slider which lets you adjust the level of security. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web.
We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention. The dark web (often referred to as the “darknet,” “black web” or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. In addition, NordVPN offers Onion over VPN (think Tor over VPN), which routes your internet traffic through one of its servers, passes it through the Onion network, and then sends it to the internet.