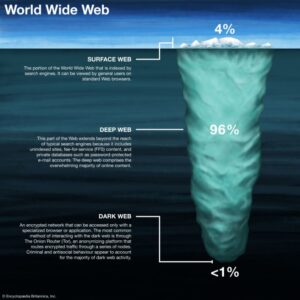
Tor websites may provide secure access to cryptocurrency wallets and anonymous email clients, and they’re also used to access black market sites. Onion sites are websites on the dark web that use the “.onion” top-level domain instead of “.com,” “.net,” “.gov,” etc. The lack of regulation leaves the dark web rife with offensive content and unsafe websites. (b) is the deep web, which consists of sites that require a login to access like email accounts, banking portals, and subscription services.
Search hidden services on the Tor network. Onion Endpoints Fetcher is a web-based tool designed to fetch and display endpoints from onion sites on the TOR network. That’s why it’s important to verify links through trusted directories and proceed with caution.
Welcome To The Official Hidden Wiki
As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. It works by sending internet traffic through volunteer-operated nodes all over the world. For this reason, you cannot browse through these sites using your default search engine. This way, you can protect yourself from websites that want to steal your login details or cryptocurrency.

What Are The Best Onion Sites?

While it can’t know your real IP address, it can see your unencrypted data, which may reveal your true identity (although HTTPS(new window) still protects you). The weakest point in the regular Tor network is the exit node. Tor is a free and open-source anonymity tool consisting of thousands of volunteer-run “nodes” around the world. Protect your business with end-to-end encryption and compliance-ready security. Protect your online identity with an encrypted password manager. "Understand that the web as we know it today is privacy-hostile and that nothing is foolproof, do research, support organisations and projects — like Tor Project, i2p, and Open Privacy — that are building and maintaining tools that make enforcing your consent easier."
Can I Access The Dark Web With The Tor Browser?

As for the nefarious services and tools, they can easily be found on the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. There are multiple search engines on the dark web that can help you find what you’re looking for. However, at least some of the services are relatively harmless. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes.
HTTPS Support
If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. This is high-level protection; no one can intercept your data or activities.
What Kind Of Content Is On The Dark Web?
Instead, visitors must access sites on the Tor Network using a special browser developed by the Tor Project. The Dark Web is just a collection of websites not listed by regular search engines like Google or Bing. Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if you don’t want to stumble on illegal activity or content. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship.
What Percentage Of The Internet Is Dark Web?

These search engines are systems that list onion links from the deep web, the main task of each search engine is to allow the display of hidden pages. I also recommend covering your webcam and disabling location services before accessing .onion sites. Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. Mexico blocked Tor access to government websites citing security concerns. It is a popular tool for journalists, researchers, and users who need to document online content.
Best Dark Web Sites 2025 – Detailed List
While not mandatory, using a VPN adds an extra layer of privacy and security by hiding Tor usage from your internet service provider. For journalists, students, researchers, and security professionals, it’s a powerful tool when used ethically and safely. You can’t search for .onion sites using Google.
The process costs a fee, but unlike other "tumbler" or "mixing" services, there is no risk that Wasabi or any of its users could scam you out of your coins. In that spirit, the CIA launched an onion site to help people around the world access its resources securely. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach. The first online publication that won a Pulitzer became the first major publication with a .onion address.
This multi-layered process makes it incredibly difficult to trace the user's origin or the website's physical location, ensuring a high degree of privacy and security. When a user connects to an onion website, their request is wrapped in multiple layers of encryption, and this encrypted "onion" is then sent through a series of volunteer-operated servers, known as relays. The name "onion" comes from the layered structure of the encryption, similar to the layers of an actual onion. The "onion" in their name refers to the multiple layers of encryption that protect user identity and activity, much like the layers of an actual onion.
- Tor's protocol creates layers of encryption—much like layers of an onion—to protect the identities of users and site operators.
- Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service.
- But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
- Journalist in India → Uses Tor to access a whistleblowing portal → Submits information anonymously while protecting their identity.
- Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy.
Do I Need A VPN If I Use Tor?

When you create a free Proton account, you get encrypted email with 1 GB storage, two password vaults, and one VPN connection. Switzerland-based Proton (formerly ProtonMail) is one of the most secure email services, and has a reputation for not logging IP addresses. Some countries and ISPs may try to prevent access to DuckDuckGo’s direct link.
These trusted sites will help you gain confidence and minimize risks. Our curated list of legitimate dark web sites above offers a safe entry point for first-time explorers. The Escrow’s .onion link provides a platform for conducting anonymous transactions on the Dark Web by holding funds securely until agreements are fulfilled. With over 50 million daily active users, Reddit hosts communities (subreddits) on a wide range of topics, making it one of the most visited social platforms. Ahmia has become a trusted tool for navigating the Dark Web, with thousands of users relying on it for its transparency and user-reporting features. SecureDrop’s .onion link is a platform designed for whistleblowers to securely and anonymously submit sensitive information to journalists.