In the event of non-compliance, authorities have shown little patience with crypto platforms facilitating money laundering. Even when crypto platforms comply with high KYC standards, some users can still circumvent those controls, making them vulnerable to various attacks and potential loss of funds (IDnow). Legislation such as the Anti Money-Laundering Directive 5 (AMLD5) and Markets in Crypto-Assets (MICA) aim to prevent money laundering in the crypto industry by requiring crypto exchanges and custodian wallet providers to implement KYC/AML regulations. European lawmakers, for instance, have created a legal framework to regulate the use of cryptocurrencies due to their steady increase in utilization (IDnow). By investing in robust compliance systems and adhering to regulatory standards, crypto firms can mitigate risks, protect their reputations, and contribute to the fight against financial crime.
Uncovering The Dark Side: Disadvantages Of Investing In Exchange-Traded Funds
E-checks provide a convenient and fee-free alternative to traditional electronic payment methods. Whether you are a business owner receiving payments from customers or an individual paying bills online, e-checks can be used for a wide range of transactions. Security is a primary concern when it comes to electronic payment methods.
- Google Wallet offers some level of anonymity by using virtual card numbers when you make a purchase.
- The card number on a credit card is typically found in the top-left corner or along the front edge.
- The ongoing battle against Bitcoin money laundering is crucial to ensure the integrity of the cryptocurrency ecosystem and protect the privacy and security of legitimate users.
- Bitcoin transactions are recorded on the blockchain, a public ledger, but user identities are often pseudonymous, making it difficult to trace transactions back to individuals.
- Sources agree on the mechanics—data theft, resale, automated testing, and cash‑out—but emphasize different elements and timescales.
Cash On Delivery As A Payment MethodOriginal Blog
They can freeze the card and investigate further to trace usage details, suspicious activities, and other signs of theft. Once affected users’ personal info is obtained, fraudsters can log into those users’ accounts or even install malware into their systems to steal more sensitive data. Phishing is a method used by scammers to trick users into trusting them and providing their personal information or account data. Unsecured Wi-Fi networks are prone to man-in-the-middle attacks, where a hacker intercepts the exchange between two parties—often by compromising the router—and gains access to sensitive data.
How Are Credit Card Numbers Stolen Or Hacked?

Hijacking a PayPal account requires a different approach than stealing a credit card number. Back then, the median credit limit on a stolen credit card was 240 times the price of the stolen card, or about 0.42 cents (US$0.0042) per dollar. US$17.36 is the average price for a credit card number, CVV, expiration date, cardholder name, and postal code—the basics. Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs.

The dark web provides an anonymous and unregulated platform for these transactions, making it difficult for authorities to trace and shut down such activities. The risks are real, as victims can face significant financial losses, damage to their credit scores, and potential identity theft. Additionally, fraudulent charges can lead to overdraft fees, late payment penalties, and damage to credit scores.

Defining External Check Fraud
This includes targeting marketplaces, forums, and websites involved in the trade of illegal goods and services. In addition to tracking individual transactions, law enforcement agencies also focus on disrupting the infrastructure supporting illegal activities on the dark web. Investigators also rely on online communities and forums where individuals discuss their experiences and provide information about illegal activities on the dark web.
The Role Of Crypto Anonymity Tools
You can customize your privacy settings to ensure that your transactions aren’t shared openly. Cash App limits daily spending to $250 without requiring identity verification, making it a suitable option if you’re new to anonymous payments. The platform allows you to make transactions without exposing personal details like your full name or account information. While the initial purchase can be kept anonymous if you pay in cash, you’ve got to exercise caution when reloading the card. By purchasing them with cash, you can further enhance your anonymity right from the start. This way, there's no digital trail linking the transaction to your personal information or banking details.
Keeping Your Data Safe
This constant evolution is primarily driven by the decentralized nature of the dark web and the anonymizing technologies employed by marketplaces. Despite the efforts of law enforcement agencies to shut down dark web marketplaces, these platforms have exhibited remarkable resilience and adaptability. The decentralized nature of Bitcoin and its underlying blockchain technology has further facilitated these transactions, making it the preferred currency on the dark web. The rise of cryptocurrency, particularly Bitcoin, has created new opportunities and challenges within the dark web ecosystem. Ulbricht was later found guilty of money laundering, conspiracy to commit computer hacking, and other charges.
Vortex Market
Consider using a password manager to securely store and generate complex passwords. Regularly scan your system to detect and remove any malicious software that could compromise your security. A firewall acts as a barrier between your device and external networks, enhancing security and mitigating the risk of malicious attacks. JavaScript can be used to exploit vulnerabilities in the browser, expose your real IP address, and compromise your anonymity.
The use of blockchain technology ensures that transactions are secure and cannot be easily traced back to individuals. Additionally, these marketplaces often have built-in escrow services and review systems to instill trust among buyers and sellers, further strengthening their resilience. This combination of anonymity and security has made Bitcoin the ideal currency for conducting business on the dark web. Bitcoin transactions are recorded on the blockchain, a digital ledger that is publicly accessible. This level of privacy has made it difficult for authorities to track and regulate illicit activities on the dark web, leading to the proliferation of marketplaces.

However, enforcement inconsistencies highlight the ongoing struggle between financial privacy and regulatory oversight in combating cryptocurrency-enabled money laundering. While they provide anonymity, they also pose regulatory challenges by complicating financial tracking and raising concerns about illicit activities. Smooth digital asset integration demands a well-considered strategy seasoned with innovation, regulation, and proactive risk management to make a secure financial future a reality. However, these digital assets also present significant risks, becoming tools for illicit activities such as money laundering, terrorist financing, and fraud.
Responses from cybersecurity professionals are increasingly focused on comprehensive strategies to combat dark web threats. Collaboration between governments, businesses, and cybersecurity firms is also evolving, leading to enhanced information sharing about emerging threats. Threat actors on the dark web are challenging cybersecurity professionals to innovate in their defensive strategies. You are facing an array of risks, from data breaches to organized crime, all increasingly sophisticated and difficult to detect. As cybercriminals continue to evolve, your awareness and proactive measures become necessary in safeguarding yourself and your community from the insidious effects of these dangerous marketplaces. These platforms facilitate illicit trade, threatening personal security and national safety while fostering an environment of distrust.
The Ongoing Battle Against Bitcoin Money Laundering
By embracing e-checks, we can enjoy the convenience of electronic payments without the hassle of additional fees. With their seamless integration, enhanced security, and cost-saving potential, e-checks have become a viable option for businesses and individuals alike. Over the course of a year, they processed a total of 500 transactions, with an average transaction value of $1,000.
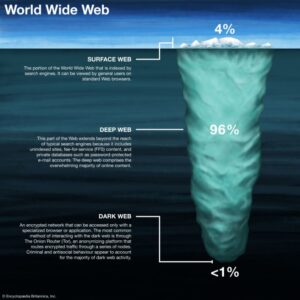
This involves presenting case studies illustrating exploiting the dark web and cryptocurrencies for money laundering. This chapter delves into the dark web, navigating the criminal underworld of money laundering and examining how cryptocurrencies have expanded opportunities for criminals to commit offenses and launder their gains. Despite the attempts to secure the Silk Road’s activities, the platform caught the attention of law enforcement. To achieve this, he leveraged Tor, a privacy-focused browser that masked users’ identities, along with Bitcoin for anonymous transactions. Created by Ross Ulbricht, the platform used Tor to hide users’ IP addresses and Bitcoin for anonymous transactions, setting the foundation for future dark web markets.