What you may not know is that you can use Tor browser to access regular HTTPS websites on the surface web. This network of more than 6,000 relays conceals the user’s location from anybody engaging in online surveillance, as well as the websites visited. Instead, onion sites are derived from a cryptographic key and must be accessed using the Tor browser. Instead, visitors must access sites on the Tor Network using a special browser developed by the Tor Project.
Tor Websites: 10 Links That Offer A Safer Browsing Experience
TorLinks is basically the same thing as The Hidden Wiki; it too is a webpage which lists a lot of deep web sites for you to visit. Although fair warning, not all the links on the page may be working, that’s so because these deep web links frequently keep changing due to govt. It also makes searching easier, you can either use the search bar at the top-right corner, or use the right-sidebar to directly find sites in the categories you’re looking for. For e.g. if you click on “links” and then on the big “Random.onion” image at the top of this specific page, it’ll take you to a random .onion site which you may or may not like. Unlike Google, Yahoo, Bing etc. which collect nearly every click of yours, time-spent, sites visited before and after data and everything else, Duck Duck Go doesn’t.
Cybersecurity teams and law enforcement agencies use it for investigations. It's ideal for fast searching and doesn’t show cluttered results. DuckDuckGo offers a .onion version with privacy-first results from both surface and dark web. Known for its massive index and premium version, Haystak is favored by cybersecurity professionals and threat analysts for its depth. It's popular among ethical researchers, journalists, and academic institutions.
Legitimate Use Cases For The Average User
Instead of giving one static list, they index onion sites dynamically. Frequent downtime or sites that never connect are also indicators of unreliable sources. Real dark web engines and onion sites load directly without such tricks. If a search engine looks messy, slow, or overloaded with pop-ups, it is often a sign that it cannot be trusted.
User Interface And Usability
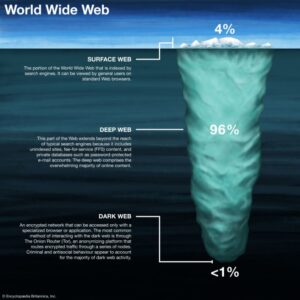
Many phishing sites imitate trusted platforms like the Hidden Wiki to trick users. To boost anonymity, many users connect to Tor through a VPN, which hides Tor usage from their internet provider. These sites often appear in onion directories, but they come with extreme risks. Here are some onion links often mentioned in directories — always verify before use. The dark web, however, is a small, intentionally hidden part of the deep web that requires special tools like the Tor Browser to access. The dark web, by contrast, includes sites that sit on the onion network and require special software like Tor to access.
What Are Deep Web Search Engines?
I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. I found its reporting on security issues and dark web developments particularly valuable for staying informed about online privacy matters. My testing showed it loads quickly and offers the same high-quality content as its regular website, making it an excellent resource for readers in censored regions. ProPublica provides Pulitzer Prize-winning uncensored investigative journalism through its .onion service. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. Its strength lies in regular updates and community-driven verification of links.
- It constitutes a concealed realm of websites accessible solely through specialized browsers, predominantly the Tor Browser.
- Integrate with tools like dark web monitoring services for alerts on credentials or IP theft.
- It’s a lesser-known but highly effective unrestricted search engine ideal for in-depth exploration.
- Many directories are outdated or cloned, while others include malicious .onion addresses.
- Founded in 2012, it stores snapshots of websites, making it possible to “go back in time” and see what websites used to look like and what information they contained.
Phobos is known for indexing new onion sites quickly. You enter a query, and the engine returns onion links with clear descriptions. In 2025, it remains one of the largest and most advanced options for finding onion sites. This is why users must stay cautious and combine Ahmia with safe browsing practices. Still, it is important to remember that no search engine is perfect. This constant updating matters because onion links often change, disappear, or resurface under new addresses.
Best Dark Web Search Engines 2025 – Secure Access To The Dark Web

It achieves this by encrypting communications and routing online content through multiple web servers. While the dark internet is often portrayed as a digital playground for criminals and anarchists, that’s not always the case. Swim even deeper and you’ll reach a subset of the deep web that’s called the “dark web”. A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity.

Top Dark Web Search Engines For Safe Access 2025 Edition
If you try clicking on these links, you’ll get an error message that the site is inaccessible. Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server. Using common sense like avoiding clicking on shady links or download buttons, sticking to known sites and adding a VPN for an extra layer of protection, you should be fine.
Table Of Contents
One of the oldest, huge result index, no content filtering Others integrate metadata extraction and ranking algorithms to determine a site's trustworthiness or usefulness. Unlike conventional web crawlers, they have to be able to handle slower load times, inconsistent site availability, and often sparse interlinking between sites. At a technical level, these engines access the dark web using specialized protocols, like the Tor project. However, the process is slower and much more complex because of the encryption, anonymity protocols, and the unstructured nature of many dark web sites.
However, third parties such as the government and your internet service provider (ISP) can see that you are using Tor. It will encrypt your traffic and data so no one can intercept it. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
Ahmia can even be accessed through regular web browsers to find ".onion" addresses, although a dark web browser like Tor is still required to access them. It also aims to prevent web tracking, enhancing user privacy while searching the dark web. Freenet stores encrypted files across its distributed network, making it difficult to trace the origin or content of information shared within its dark web ecosystem. This dark web browser utilizes a decentralized distributed data store to deliver information.