It offers a Reddit-like interface, where you can learn everything you need to know about darknet websites and spotting the real from the scammers. Hence, it’s quite useful to be able to connect to its onion link. If you’re new to the deep/dark web, DuckDuckGo’s onion link should be your first port of call. Speak your mind here without fear, as onion links are immune to censorship. The main advantage is that you can also access other dark web directories without running into malware. You’ll find links to many of the sites we’ve covered in this list.
🕶️Staying Anonymous On The Dark Web
This provides convenience, as it allows you to access onion websites using your regular browser. Onion Services are websites that exist within the Tor network and can only be accessed from the Tor network. When you buy or sell illegal goods online, you are not hidden from law enforcement, Europol’s director emphasized after a Dream Market bust. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
Vorm Web Search Engine
The tool is designed so that even the server cannot read the content you paste. It’s one of the few resources that consistently updates its .onion mirror, ensuring availability even during domain seizures or censorship events. Every installation has its .onion link hosted by the respective publication. While many users begin their dark web journey here, caution is strongly advised. The organization regularly maintains this onion version and lists the official address on its clearnet site for verification.
Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN. Not very safe, but it’s still useable. Well, it’s really not that complicated – using the Tor over VPN method means connecting to a VPN service before using the Tor browser.
The dashboard should open properly, indicating you’re ready to connect to any VPN server. Even if the Tor node fails, your data won’t be exposed because the VPN’s encryption still holds up. With this information, the ISP will know you’re on the dark web because Tor is mainly used for this purpose. Your ISP can see that you’re connected to Tor, as the encryption takes place after you connect to the browser. The entry node encrypts your traffic, and it bounces across several nodes in the Tor network until it reaches the exit node.
Watch Out; Your ISP Could See You Using The Tor
- Keep in mind that you’ve to use very specific keywords when searching.
- Simply put, onion sites are websites that are hosted on the Tor darknet that use the “.onion” top-level domain instead of “.com,” or “.gov” for example.
- To explore it, you need to install Tor and use a dark web search engine or directory to find and visit onion search engine links.
- This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page.
- The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China.
For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Due to its anonymity, the dark web has attracted people who could endanger their lives by revealing their identities on the surface web. Simply put, accessing and browsing the dark web is perfectly legal. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity.
Verify All onion Links
Detractors argue that online anonymity encourages criminality and impedes law enforcement. The Tor network also gave hackers, terrorists, and distributors of illegal pornography a secure method of communication. The earliest form of the modern dark web arose in March 2000 when Irish student Ian Clarke developed and released Freenet, which offers anonymous communication online via a decentralized network of Freenet’s users.
What Are Darknet Markets? Complete Guide
About 80% of its web traffic is related to accessing child pornography despite it being difficult to find even on the dark web. Scott Dueweke the president and founder of Zebryx Consulting states that Russian electronic currency such as WebMoney and Perfect Money are behind the majority of the illegal actions. Recently, around 100,000 compromised ChatGPT users' login information was sold on the dark web in 2023. Attempts to monitor this activity have been made through various government and private organizations, and an examination of the tools used can be found in the Procedia Computer Science journal.

Once you upload an image, the site provides you with shareable links for email messages, instant messaging, message boards, and websites. You can also use its .onion link via the Tor network to access the site in restrictive countries, where it might be unavailable. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites. Torch is one of the oldest dark web search engines, and it’s generally considered one of the safest. Ahmia is a search engine for .onion sites — you search for a keyword and Ahmia retrieves relevant results.

Naiyie is a former content strategist at CyberGhost, where she researches and writes about cybersecurity and tech-related topics. If you’re reading an independent news site or doing research, it’s probably fine. If you’re looking at illegal dark web porn or purchasing illicit substances, it’s illegal. Whether it’s illegal or not depends on what sites you visit. The dark web is a hidden part of the internet you can only access with Tor software. This gives anonymity to .onion website owners and visitors.
Wasabi Wallet On Tor
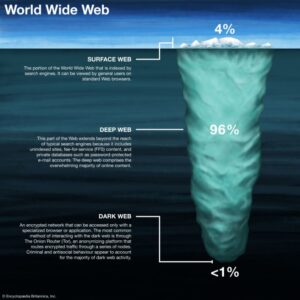
Content and services on the deep web are accessible through a regular browser. When you search a term (or query) in a web browser, the search engine combs through the database to find relevant results and serves them up on SERPs. Discovered pages are indexed in an extensive database and ranked based on numerous factors.
This can often be for political reasons, but also because they may be involved in illegal activities, such as the ones listed above. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
Alt Address
The reviews published on Wizcase are believed to be accurate as of the date of each article, and written according to our strict reviewing standards that prioritize professional and thorough examination by the reviewer, taking into account the technical capabilities and qualities of the product together with its commercial value for users. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. Well, as you might have guessed, the dark web version spins very unpalatable search strings, asking the user to guess their equally disturbing answers. For those of you unfamiliar with this, G-Feud is a clear web game where you have to guess the answers to some random or topic-related search strings.

While your IP address is hidden, the site can still collect information you share on your profile. However, Facebook’s dark web version will still log your data, so keep that in mind. I like that you can ask the search engine to match all of your search words for exact results, or only some of them for broader search results. Plus, it lets you set your location for local results, manage safe search filtering, and there’s even an AI “Assist” tool that provides AI search results — so you don’t have to visit web pages to find your answer. And I liked that if I visited a site that had a .onion version, it prompted me to switch to that version.

There are various sites on the dark web dedicated to the distribution and discussion of hacking tools, cyberattack services (such as DDoS attacks), and information on data breaches and leaks. These platforms provide services related to illegal activities, such as hacking tools, malware, ransomware, or services for hire (e.g., DDoS attacks, identity theft). This includes email accounts, private databases, paywalled sites, and subscription services.
- Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material.
- DarkWeb “marketplaces” guarantee confidentiality and anti-surveillance for your online purchases that you simply won’t find on any other websites.
- In a world of bulk data collection, surveillance, and personalized ad tracking, it's up to us to take control of our personal privacy.
- If you are ready to dive into the dark web, you will need an internet connection and the Tor Browser.
How Can Businesses Protect Themselves From Dark Web Threats?
This includes implementing multi-factor authentication (MFA), using robust firewalls, regularly patching systems, and encrypting sensitive data. Specialized threat intelligence services can scan dark web forums and marketplaces for mentions of your company’s data. Companies should actively monitor the dark web for stolen employee credentials, customer data, and intellectual property. While Tor provides anonymity, it doesn’t hide the fact that you’re using Tor. It allows citizens to access blocked news sites, social media platforms, and other information that their governments don’t want them to see. For many, the primary draw is the promise of true online anonymity.
With the right precautions, the Hidden Wiki in 2025 remains one of the most helpful tools for navigating the dark web — and yes, you’re in the right place. “If you’re completely new, start with this Hidden Wiki beginner’s guide to understand how it works before browsing. If you ever land on a Hidden Wiki version with suspicious design, aggressive pop-ups, or broken links, treat it as a red flag and exit immediately.
The editor will then create a link for you to forward to the sender. To increase the security level, add password protection and determine the expiration time for messages. It protects their submissions using high-end encryption and doesn’t log their IP addresses or device information – full anonymity. It offers users a safe and convenient way to send private and critical information through email.