
Criminals exploit the anonymity and encryption features of the dark web to buy and sell stolen credit card information. To avoid such losses, it is crucial to regularly monitor credit card transactions, report any unauthorized charges promptly, and take proactive steps to protect personal information. The dark web serves as a marketplace where stolen credit card information is bought and sold, fueling illegal activities. Credit cards and the dark web pose a significant threat to individuals and their financial security. Additionally, phishing scams and malware-infected websites are utilized to trick unsuspecting victims into providing their credit card details unknowingly. Another method employed is card skimming, where criminals install hidden devices on legitimate payment terminals or ATMs to capture card details for later use.
To minimize the risk of payment data exposure, only shop from reputable retailers, use digital payment methods or one-time private cards, and protect your accounts with two-factor authentication. In total, the analysis included more than 200 listings for PayPal accounts and about 400 listings for credit cards. So unlike credit cards, prices for PayPal accounts and transfers have gone up during the pandemic by 293 percent. For this study, the researchers focused on PayPal accounts and credit cards.
Over 30 Million Stolen Credit Card Records Being Sold On The Dark Web
Now, “it’s a lot more difficult to create skimmers to compromise those cards because they have been encrypted.” Since the EMV implementation deadline in 2015, there has been a decrease in in-person counterfeit payment fraud by 80 percent, according to the most recent “Visa Chip Card Update.” “You can go to these forums, and … people will ask to purchase certain types of data, or to learn how to do something,” and others will respond with suggestions of .onion sites, where cybercriminals share information. It’s ‘dark’ if you can’t just walk around and see it—you need special access tools, special permissions, special accounts—things like that grant you or buy you access to it,” explains Chris Novak, director of Verizon Threat Research Advisory Center.
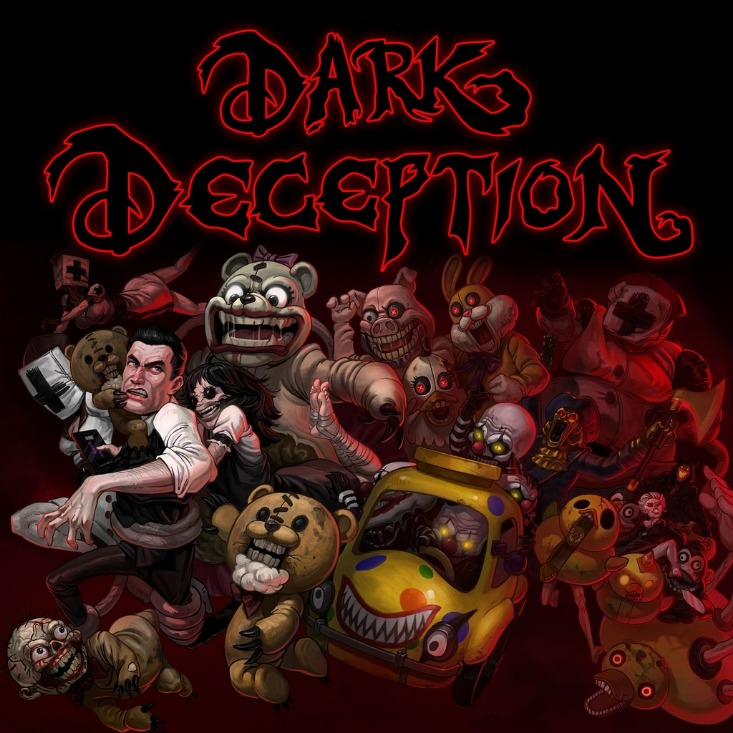
Carding In 2025: How Cyber Criminals Sell Stolen Credit Cards And Teach Fraud
The dark web operates using cryptocurrencies like Bitcoin, making it difficult for law enforcement to track and prosecute criminals. Only through collective efforts and advancements in cybersecurity can we hope to mitigate the impact of these nefarious activities and safeguard the digital landscape for future generations. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.
Understanding Credit Card Fraud On The Dark Web
Card Shops typically host the trade of credit cards and other stolen financial information, making it easy for cybercriminals to find what they're looking for. Free and paid tutorials on the dark web teach fledgling criminals how to use stolen credit cards. The rise of cryptocurrencies like Bitcoin and specialized “Dark Web” markets focused on selling credit card details and other personal information has made it possible for criminals to act efficiently and—most importantly—anonymously. With hundreds of thousands of credit card fraud reports each year, it’s no wonder banks offer 24/7 hotlines specifically for victims to report lost and stolen cards.

JOIN THE Cyber Security Hub COMMUNITY

Start by regularly updating your passwords for online accounts and using strong, unique combinations that include a mix of letters, numbers, and special characters. If you notice anything unusual, contact your credit card company immediately to report the issue. Illegal activities thrive on the dark web, including the illicit trade and sale of credit card information. Additionally, fraudulent charges can lead to overdraft fees, late payment penalties, and damage to credit scores.
Phishing Scams
To ensure larger reach, the crooks distribute the collection via a clearnet domain and on other hacking and carding forums. Backed by Y Combinator as part of the 2021 winter cohort, Cyble has also been recognized by Forbes as one of the top 20 Best Cybersecurity Start-ups To Watch In 2020. Following are some of the essential cybersecurity best practices to create the first line of control against attackers. Here are the top 500 potential affected banks, based on the total count (in descending order) – A surge in infostealer activity is partly responsible for the increased number of compromised passwords, Bitsight said. The latest threat intelligence analysis, however, suggests those numbers are low.
Ways To Avoid Or Mitigate Card Thefts
Don’t put your real credit or debit card credentials at risk—hide them with Privacy Virtual Cards. Depending on the virtual card provider, you can customize details like spending limits and even pause/close the card at your convenience. Calling your card provider is also important because it limits your financial liability. They can freeze the card and investigate further to trace usage details, suspicious activities, and other signs of theft.
Some vendors also offer distinct products such as credit reports, Social Security numbers and login details for different paid services. The customers of stolen data markets may reside anywhere in the world, and their demands for specific data or services may drive data breaches and cybercrime to provide the supply. Many of the people who supply and operate the markets appear to be cybercriminals from Eastern Europe and Russia who steal data and then sell it to others. More recently, vendors of stolen data have also begun to operate on messaging platforms such as Telegram and Signal to quickly connect with customers. The same is true for the millions of email account usernames and passwords, or access to streaming services that data breaches can expose.
- The sale of payment card information is big business; in 2022, the average price of stolen credit card data averaged between $17 and $120, depending upon the account’s balance.
- Hackers get card info through data breaches, phishing, and skimming devices at stores or ATMs.
- Cybersecurity tools can spot threats early.
- Cybercriminals "have been known to purchase expired payment cards to gain more information on potential victims," notes the threat intelligence company Cyble in a post about the leak.
- They injected malicious code on the website checkout pages to exfiltrate payment information.
However, when it comes to the stolen credit cards, Bitsight confirmed that the rise was “exclusively due to a surge in US cards; the number of cards from the rest of the world declined by 1.6 million, but listings of US cards increased by 4.5 million, counting for 80.7% of all compromised card listings in 2024.” But it’s the threat from infostealer malware that is of most concern right now, not just in terms of the gargantuan number of passwords that are available in logs for sale, but the sheer number of stolen credit cards as well. The BidenCash stolen credit card marketplace is giving away 1.9 million credit cards for free via its store to promote itself among cybercriminals. In addition to PayPal account balances, they can also transfer money from any connected bank accounts or credit cards. For fledgling criminals who don’t know how to use stolen credit cards, there are plenty of free and paid tutorials for carding on the dark web. These platforms serve as hubs for cybercriminals to easily buy and sell compromised payment card details, including credit card numbers, CVV codes, expiry dates, and cardholder information.
The banks, lenders, and credit card companies are not responsible for any content posted on this site and do not endorse or guarantee any reviews. Internet criminals buy and sell personal data on the dark web to commit fraud. From Social Security numbers to bank logins and medical records, cybercriminals buy and sell stolen data every day. Learn the basics of credit card cards, including features, fees, and rewards to make informed decisions about your credit card usage. Card checkers are tools used by threat actors to verify the validity and authenticity of credit card information they purchase on the dark web.
Tucker Carlson Is Launching His Own Precious Metals Company
There’s an underground ecosystem where sensitive data is bought, sold, and traded—not just on the dark web, as you might expect, but also on publicly accessible websites, channels, and forums. The offers on the site do not represent all available financial services, companies, or products. Your lender or insurer may use a different FICO® Score than FICO® Score 8, or another type of credit score altogether. The Experian Smart Money™ Debit Card is issued by Community Federal Savings Bank (CFSB), pursuant to a license from Mastercard International. Experian is a globally recognized financial leader, committed to being a Big Financial Friend—empowering millions to take control of their finances through expert guidance and innovative tools.
Many tracker apps link directly to bank accounts for up-to-the-minute info. Tracker apps offer a powerful way to keep tabs on credit card activity. Spotting fraud on your accounts is key. This makes it crucial to monitor accounts closely and use strong security measures. This lets them quickly cash out funds from compromised accounts. Credit card fraud often starts with data breaches or hacking.
This is a great way to safeguard your identity, but you’ll need to lift the freeze if you plan to apply for new credit. Setting up these alerts can provide an extra layer of security by notifying you of any irregular activities as they happen. Log into your account and go to the Dark Web Monitoring section within the app. It can take months—or even years—to recover from this kind of identity fraud. Ideal Credit Union can use this tracking data to monitor visitor behavior on our site, such as what you are clicking and viewing, or where you are submitting information.



