The rankings and reviews we publish may also take into consideration the common ownership mentioned above, and affiliate commissions we earn for purchases through links on our website. The reviews published on Wizcase are believed to be accurate as of the date of each article, and written according to our strict reviewing standards that prioritize professional and thorough examination by the reviewer, taking into account the technical capabilities and qualities of the product together with its commercial value for users. My favorites are DuckDuckGo (usually the Tor browser’s default search engine), The Hidden Wiki, and Ahmia.
Hacking Groups And Services
OnionName lets you generate an .onion domain name that starts with a specific keyword — like onionamev33r7w4zckyttobq3vrt725iuyr6xessihxifhxrhupixqad.onion/, which is OnionName’s dark web link. Dark web domains are generated in a cryptographically secure way, so they look like random strings of 16 characters or more (like 3g2upl4pq6kufc4m.onion, for example). Archive.today allows you to take a snapshot of a web page, which will remain online even if the original web page disappears. I also like that the security guides are user-friendly — the format is easy to scan, complicated terms are explained very well, and there are videos and screenshots.

Depending on your preference, you can find links in well-categorized groups. OnionLinks is a library of dark web links, most importantly, active links. But it is not all bad; the dark web’s anonymity also allows well-meaning individuals, such as whistleblowers As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. We’ve organized these sites into intuitive categories so you can quickly jump to what matters most for you.
Therefore, by visiting dark net sites unprotected, you expose yourself to potential attacks that may target you. Unfortunately, some individuals utilize the dark web’s image to scam people. Other services are real; if you need something, you will receive it after reaching a certain price agreement.
How Do I Open Onion Links?
The core principle of the Tor network was first developed by U.S. Those who access the dark web do so via the Tor (The Onion Router) browser. Journalists in overly restrictive countries also appreciate the anonymity of the dark web.
Onionname

To reach Geekflare.com, you can either type its URL in your standard web browser or search for Geekflare in your favorite search engine. However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. The dark web often connotes illicit activities like illegal drug sales and hacking.
- Some of these people are whistleblowers, abuse, persecution, and activist victims, as well as politicians.
- The dark web and deep web are home to countless hidden forums where users discuss everything from privacy tools to cybersecurity to hacking,…
- It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled.
- It helps people anonymously use the BBC website without restrictions.
The Danger Of Tor Network
- Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web).
- The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network.
- For these reasons, it’s a good idea to safeguard your online activities with NordVPN while using the dark web.
- “But much of this appears to be driven around a need for criminal threat actors to get convenient access to quick payments from victims in order to support further operations,” he adds.
- Europol said several pedophile chat sites were also taken down in the German-led intelligence operation.
- Because of its structured directory format, OnionLinks is often included in lists of dark web search tools.
Ransomware leak sites are publicity sites where ransomware groups share the details of their latest victims. Dark web forums are very similar to their clear web counterparts in almost every way, except for the content they discuss. The Dark Web Hub equips law enforcement, enterprises, MSSPs, and researchers with essential knowledge to navigate dark web threats. Darren is regularly featured as a cyber-security expert in major media outlets including CBS Evening News, Fox & Friends, USA Today, ABC and Mashable. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC.
Marketplaces
Ross Ulbricht, the creator of Silk Road, was arrested on suspicion of hiring a hitman to kill six people, but the charges were later dropped. China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims. While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money. There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons. The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity.
The Top 5 Dark Web Search Engines
Ahmia is a popular dark web search engine that indexes .onion websites, making them accessible through the Tor network. Ahmia is a dark web search engine that indexes .onion websites and filters out illegal content, providing a clean and ethical search experience. Many dark web search engines offer uncensored search results, increasing the likelihood of encountering illegal content such as abuse material or hidden services. It means they search for .onion websites through automated means but also allow users to suggest new sites, most often anonymously. The Tor network adds a layer of anonymity, which helps dark web sites remain hidden and makes it impossible for conventional search engines to index them. It began as a simple, categorized directory of .onion links — helping new users find forums, search engines, whistleblowing tools, and more.
Some dark web search engines are designed specifically for darknet browsing, while others also work on the clear web. Accessing content on the dark web takes a few extra steps, but it’s not as hard as you might think. Do your research beforehand and don’t click suspicious links. Others, called shadow directories, require you to access the dark web and enter a special URL. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. Cybercrime services are more commonly sold through marketplaces, but you can usually find someone offering hacked servers, computer logins, and stolen data on such forums.
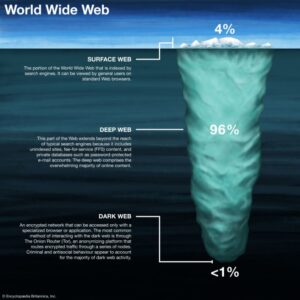
The deep and dark web are applications of integral internet features to provide privacy and anonymity. The creator of Silk Road, Ross Ulbricht, was arrested by Homeland Security investigations (HSI) for his site and allegedly hiring a hitman to kill six people, although the charges were later dropped. There are at least some real and fraudulent websites claiming to be used by ISIL (ISIS), including a fake one seized in Operation Onymous. Four people had been detained in raids, including a man from Paraguay, on suspicion of running the network. In May 2021, German police said that they had dismantled one of the world's biggest child pornography networks on the dark web known as Boystown; the website had over 400,000 registered users. There is regular law enforcement action against sites distributing child pornography – often via compromising the site and tracking users' IP addresses.
Also, we'd like to point out that several dark net sites face technical issues and remain inoperative temporarily or shut down permanently. Although there is some crossover, the list of sites on OnionLinks is broadly different from those on The Hidden Wiki. You can rely on this .onion site if The Hidden Wiki goes down temporarily or permanently. It provides a list of dark net sites across endless categories. That said, you may come across advertisements while searching on Haystack.
What Is Kubernetes And Containers? Why Is So Popular?
The following list of Tor sites showcases some of the best and most useful legitimate content available on the dark web. Learn more about how to access the Tor network with Proton VPN You will first need to configure your browser to resolve .onion links, but you only need to do this once. To access an onion website, simply open its onion link in the Tor Browser or, if using one of Proton VPN’s Tor special servers, inside your regular browser.
You'll often see a sign in stores that says "look, don't touch," and it's not a bad adage to bear in mind as you navigate around the dark web. As I've previously said, it's a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you're dealing with. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. However, it's much harder to get at the people who are doing the uploading and downloading.
Aside from being a place for legitimate research and activities, the dark web is home to the world’s most nefarious black markets. The Tor Project is a nonprofit organization, it started as a university research project. If the connection drops, you’ll be vulnerable to attack and your data could leak into the wrong hands. That’s why it’s important to make it as difficult as possible for them. It is possible for people to track you on the dark web.
The tip of the iceberg floating above the surface is the portion of the internet we can access through normal means — i.e. browsers and search engines. A repository of sites that can’t be found by traditional search engines, the dark web is as intriguing as it is dangerous. Use categorized directories or reputable search engines to reduce the chance of clicking on spam or malicious links. Some may log search history, contain hidden scripts, or other elements that can jeopardize user anonymity. Unlike the surface web, dark web search engines have no reliable mechanisms to report or take down malware-hosting websites.