Paid services like Aura and Lifelock provide more comprehensive coverage and typically range from $7 to $15 per month for individual accounts. These free services lack the digital security tools and advanced monitoring and restoration services many paid services offer. "Many banks, credit unions, and other financial-service companies offer these."
Darknet Market Price Index: 2018 Report
More generally, payment services were highly prevalent, even with bank accounts and credit cards excluded. Streaming and VPN services dominated the listings of hacked accounts for sale on the darknet markets, together accounting for 57% of all log-ins available for purchase. We also streamlined our focus to only look at online accounts in the strictest sense of the term, which means we excluded traditional bank accounts and credit cards.
Adult sites often ask for a monthly fee to access their videos, and hackers circumvent this by piggybacking off of a legitimate customer's account. In a similar vein, adult website accounts are a hot commodity on the dark web. Compromised Netflix accounts sell for just a couple of dollars, a small price to pay versus Netflix's monthly fee. If a hacker gains access to your Netflix account, they can use it to watch shows without paying a penny. LogDog reported that eHarmony accounts sell for around $10, which made them the second-most expensive account in LogDog's report.
- "As a result, retail organizations have continued to see a rise in attack methods like e-skimming where attackers inject JavaScript into payment processing pages on retail sites in order to steal credit card information from unsuspecting customers. Most prominent among groups that deploy skimming malware is Magecart, a group of malicious actors who got their name from initially compromising the popular e-commerce, Magento CMS, at scale. This group has consistently extended its capabilities and improved its tactics to infiltrate e-commerce applications and avoid detection, most recently through impersonating legitimate payment applications by way of homoglyph attacks, ultimately fooling victims into visiting malicious websites," Foss says.
- The actors are able to receive funds based on credit card number or via banking transfer in EUR, USD and other currencies.
- Internet criminals buy and sell personal data on the dark web to commit fraud.
- But, how much does the sale of stolen information work, exactly, and how much money are criminals making from stolen data?
- Typically, this will require entering a security code generated in an app on another device, such as your smartphone.
How A PayPal Account Or Credit Card Ends Up On The Dark Web
It was like a DIY hacker’s toolkit so they could build their own banking Trojan botnet. He liked the idea of there being a single botnet that ruled them all, and it actually seems fitting because ZeuS would eventually become the king of all banking malware. These early wins were proving to the hackers that they were onto something big, and if they could just improve the malware a little bit and scale it up, they could steal a lot of money this way.
The Dark Web & Identity Theft: What You Should Know
Given the rise of digitalisation (today we live online and our digital identity is an extension of the real one), it is always important to remember the significance of cyber hygiene and protection. This type of information, known as ‘fullz’, includes datasets such as name, address, social security number, date of birth, etc. This allows directors to focus on what matters most, the business, without worrying about access attempts that, if well-supported by a solid consultancy, should come to nothing. For example, in April, a group of cybercriminals managed to infiltrate the system of one of the main banks in Europe and steal sensitive data from more than half a million customers. In an environment where cyber threats are increasingly sophisticated and persistent, cyber threat intelligence serves as an essential tool in a financial institution’s cybersecurity arsenal. By understanding the tactics, techniques, and procedures (TTPs) of threat actors, financial institutions can better anticipate attacks and fortify their defenses accordingly.
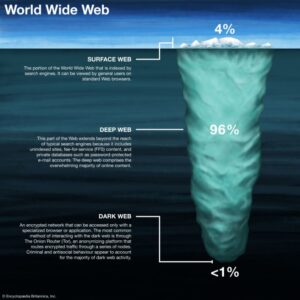
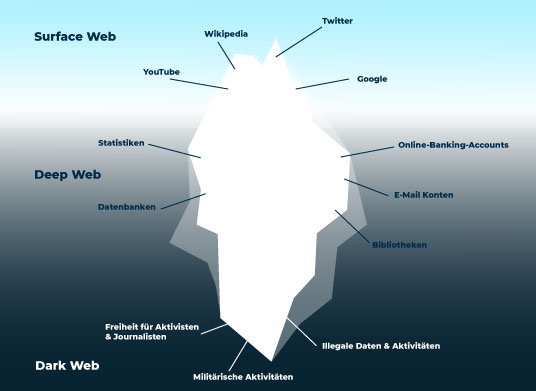
However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. Additionally, VPNs protect you from hackers who might be after your personal information or payment details. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. Business operational data, such as operational data, financial data, intellectual property, and trade secrets can be found on the dark web.
DDOS Attacks
The BlackCat/ALPHV ransomware group spent nine days moving laterally, exfiltrating 6 terabytes of highly sensitive data before deploying ransomware. This is the high stakes end of the credential market, dominated by Initial Access Brokers (IABs). Personally Identifiable Information (PII) is the raw material for a vast array of fraudulent activities.
Darknet Market Price Index: 2019 Report
Here is the Assistant Attorney General Leslie Caldwell of the US Department of Justice Criminal Division to explain what they did. By May of 2014, the FBI discovered the real identity of Slavik. Now, ZeuS infects computers and steals passwords, then listens for bank logins. Together, the Business Club thought about other ways that the ZeuS botnet could make money, and that’s when it hit them; ransomware. Each member had their own specialty; some were good at tech support, others good at creating malicious software, and some were good at recruiting money mules.

Frequently Asked Questions (FAQs) About Dark Web Marketplaces
This trend may seem odd at first, but think about the personal information used in dating accounts. Private and financial accounts are the more obvious examples of dark web account selling. It goes beyond bank accounts, too; a lot of accounts you believe are useless to hackers are sold on the dark web. While the dark web is an active marketplace for illegal goods, did you know that your web accounts are also a valuable commodity?
Telephone And E-Mail Flood – Fraud-as-a-Service
This not only jeopardizes customer trust but also exposes institutions to substantial financial losses. In return for decrypting the files and for not leaking out the compromised data, the cybercriminals are likely to demand a ransom from the victim, which makes this business usually very profitable and popular. Ransomware, which is a type of malware, is designed to penetrate into the system of an organization, steal its internal information and encrypt the files so they won’t be accessible anymore.
However, you must wait some time to reassess this marketplace because it’s been shut down. It contains a good selection of product listings that range over 35,000 items. But since its relaunch, the developers are focusing more on operational security and ensuring that users can have a good experience on this site.
"As a result, retail organizations have continued to see a rise in attack methods like e-skimming where attackers inject JavaScript into payment processing pages on retail sites in order to steal credit card information from unsuspecting customers. Most prominent among groups that deploy skimming malware is Magecart, a group of malicious actors who got their name from initially compromising the popular e-commerce, Magento CMS, at scale. This group has consistently extended its capabilities and improved its tactics to infiltrate e-commerce applications and avoid detection, most recently through impersonating legitimate payment applications by way of homoglyph attacks, ultimately fooling victims into visiting malicious websites," Foss says. Criminals buy this information and use it to open fake bank accounts, steal money, or commit other crimes under your name. However, when it comes to darknet markets, the story is very different.
Don’t Provide Personal Information
In addition, mainstream search engines also track your searches and collect personal information. Moreover, you can use a Tor circuit, but it won’t improve security; instead, it will surely improve the browsing speed. For instance, you can choose the preferred security levels for enhanced protection. Changing the Tor browser settings can further boost your security levels on the dark web shops. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details.
The transfers were sending the money to accounts overseas, but the thought crossed the FBI agent’s mind that maybe these customers were just trying to commit fraud and lying that the money was stolen. It specialized in narcotics fentanyl, heroin, cocaine, stolen financial data, fake documents, and even in house money laundering/mixing services. It specialized in narcotics, stolen data credit cards, credentials and contraband. Cryptocurrency accounts still fetch the highest prices among hacked online accounts, according to online data security provider Privacy Affairs. This data – most often stolen through phishing, credential stuffing, data breaches, and card skimmers – is bought and sold on dark web marketplaces. Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing, says Comparitech.

How Law Enforcement Tracks Down Dark Web Criminals
In response to escalating cyber threats, banks must adopt a multi-layered defense strategy that includes dark web monitoring. The deep and dark web platforms that consist of many different marketplaces, hacking discussions, and closed chat rooms are fertile grounds for the trade of malicious information. Because third-party vendors store sensitive data of different clients, a single compromise could impact hundreds and sometimes thousands of companies.