OnionLand functions as both a dark web search engine and a deep web search engine, offering a smooth user experience and access to thousands of hidden services. DarkSearch is a deep search engine that prioritizes user privacy by indexing .onion websites. It delivers an uncensored search experience, granting users access to a diverse array of information while effectively excluding illegal content. Since the dark web is hidden from the surface web, these dark web search engines allow users to explore the concealed part of the Internet.

The Deep Web And Its Real Purpose:
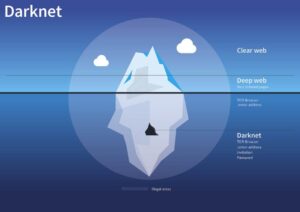
It’s no secret that the dark web can be a tricky and dangerous place for the general internet user. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. In darknet mode, you can select friends on the network and only connect and share dark web content with them.
- It was initially created to provide additional security and eliminate cryptocurrency theft.
- Tor is a free and open-source anonymity tool consisting of thousands of volunteer-run “nodes” around the world.
- Finding Tor links isn’t easy, and when it comes to finding legal links the hardship only increases considering how the Deep/Dark web is ill-famous for its illegal nature.
- However, these search engines serve as an entry to the internet's underbelly.
- These malicious sites may attempt to steal your personal information or compromise your device’s security.
How To Watch The Google IO 2025 Keynote
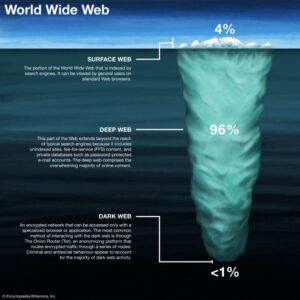
No, .onion sites require the Tor network to access them. Yes, if you're using tools like Tor, a VPN, and avoiding suspicious links, these search engines can be safe when used responsibly. In this blog, we explore the top 10 Dark Web search engines of 2025, focusing on safety, anonymity, and usability. Many of them are safe for beginners to use since they filter out dangerous/illegal content to only provide safe .onion links. The “surface web,” on the other hand, is the publicly available part of the internet that search engines index.
Because it’s easier to contain malware in a virtual environment, which can be fully controlled. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Because it’s not as safe as Tor over VPN. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN.
A Quick Guide On How To Use A VPN With Tor
The entry of internet groups involved in various countries have brought forward requirement of new laws. Users can conceal their identity online and make them safe before publishing required data. Therefore, it is inevitable to discipline the laws regulating internet usage first.
News & Whistleblowing
Uploading, as well as downloading/accessing the books is absolutely free without requiring any registration whatsoever. Anyone can upload Ebooks on the platform even if it’s your own considering it adds some value. Also provides for advanced features such as password protection of the pasted content along with expiry time for it. Upon the text being pasted, a URL is generated which can be shared with those you wish to share the content with.
Best Tor Websites In 2025

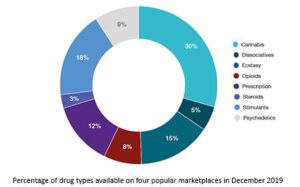
While some use it for legitimate reasons like bypassing censorship, others exploit it for illegal activities. The dark web offers anonymity and privacy, but it also presents significant challenges. These lists may not be trustworthy, and some might contain malicious links. Finding them often involves browsing specific dark web directories or forums known as “link lists.” However, be cautious.
If you log into personal accounts on the dark web or visit websites with tracking scripts, then your activity may be tracked. Avast BreachGuard monitors the dark web for data breaches around the clock. What should you do if your information is found in a data breach or you think it’s been leaked somewhere? When data brokers get hacked, the stolen data can include compromised credit cards, social security numbers, and other data, depending on what was exposed in the breach. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data.
BBC News (and Other Leading News Sites)
VPN is not a mere security layer; it is a lifesaving mechanism there days. This requires framing of international laws for regulating internet freedom. The laws need to be enacted in such a way that a dark web user in another country needs to avail the protection.
Since it’s an old search engine that hasn’t changed much, its indexing, while broad, is not always reliable. But you need to keep in mind that even one careless click can result in you downloading malware, compromising personal data, or unintentionally accessing compromising content. Torch is one of the oldest dark web search engines still in operation and hasn’t changed much over time. This search engine’s indexing is relatively shallow compared to other uncensored engines, meaning many dark web sites remain undiscovered or unlisted. It filters content heavily and can be accessed both through the surface web (the traditional part of the internet) and the Tor browser. Ahmia is one of the better-known dark web search engines.

StrongBox adds advanced metadata stripping and encrypted messaging features, increasing whistleblower protection. GlobaLeaks is an open-source platform designed for NGOs and media to create customizable submission portals, emphasizing decentralization and anonymity. For developers and site operators, hosting on the dark web requires privacy, uptime, and resistance to attacks. These services form the communication backbone for sensitive conversations in high-risk environments. Sigaint provides encrypted email favored by whistleblowers and privacy advocates, focusing on ease of use and robust security. The Hub is another well-established forum offering extensive guides and support for newcomers and veterans alike, covering everything from vendor reviews to operational security.
Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Besides, victims of crime may want to hide their identities from their perpetrators. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
While no search engine can cover the entire dark web due to its decentralized and ever-changing nature, Haystak is a top choice for exploring its hidden content. While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking. The search engine doesn’t impose censorship, meaning you can find a broad spectrum of sites, including those that may be illegal or disturbing. The search engine allows you to look for old V2 onion addresses, images, and content on I2P.
Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing. You can access the dark web on mobile with a dedicated dark web browser app. The Tor network combined with a VPN is one of the safest ways to get on the dark web.
Phishing is a common method used on dark web forums and sites to extract sensitive information. Tordex also provides no filters, no user guidance, and no warning labels. The accuracy of search suggestions is another concern. Because it doesn’t use a crawler or ranking algorithm, OnionLinks is static and highly dependent on manual submissions, which makes it unreliable for current or time-sensitive research. Users must manually scroll through categories, many of which include outdated or broken links.

Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines.