Magnetic stripe data dumps on the dark web include raw credit card data, such as bank account numbers and account balances. Stolen credit cards are often used to make purchases at specific sites that don't have protections against fraud. Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. Physical cards, on the other hand, are cloned from stolen online details and can be used to withdraw cash from ATMs. Card data is a hot commodity on the dark web, with credit card details and cloned cards being sold to cybercriminals. Card Shops typically host the trade of credit cards and other stolen financial information, making it easy for cybercriminals to find what they're looking for.
- Scammers then lure cardholders in by promising top-up bonuses, rebates, or other discounts, none of which will ever materialize.
- I agree to Money's Terms of Use and Privacy Notice and consent to the processing of my personal information.
- Buying Bitcoin anonymously is less frightening and burdensome than you might think, and it’s completely legitimate other than your fundamental right.
- But it’s hard to ignore the bank card numbers when you see them in black and white like this.
- Running your own node protects your Bitcoin wallet from disclosing information about your transactions.
- The initial bidding price was set for US$5,000 but the cards could be purchased outright for triple the amount.
PayPal is widely used by online merchants and even real-life stores, allowing you to make private purchases from almost anywhere. VPNs also hide your IP address, which prevents others from tracking your activity and provides access to geo-restricted payment methods from anywhere. I always recommend using a reputable VPN to protect your online transactions.
Can You Buy Gift Cards Anonymously Online?
They use data breaches, phishing, and skimmers. The average cost of a hacked card is just $10. Neon is the official database partner of DEV If businesses don’t stay ahead, they will keep losing millions to invisible, untraceable fraud. Customers who reused their passwords across sites found their accounts cleaned out overnight.
Can I Use Anonymous Payment Methods While Traveling Or Abroad?

The card number on a credit card is typically found in the top-left corner or along the front edge. These platforms serve as hubs for cybercriminals to buy and sell compromised payment card details. The price for cloned cards varies depending on the credit limit, with an average price of $171. The average price for a credit card number, CVV, expiration date, cardholder name, and postal code is $17.36. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. These groups often originate from leaked credit card credentials, which have become a common phenomenon, particularly in the past months.
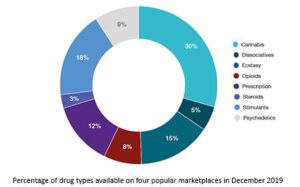
Tutorials range from guidance on using legitimate websites with stolen credit cards, to tips on avoiding IP address flagging and methods for exploiting mobile payment services and cryptocurrencies to drain funds. Leaked credit cards from Telegram channels account for the overwhelming majority of compromised payment card details. Researchers gathered data from 13 dark web marketplaces, where they found over 200 listings for stolen PayPal accounts and about 400 listings for credit cards. If you have the chance to buy prepaid cards from your local store in cash instead of your debit/credit card, you’ll reach the ultimate level of anonymity for such a method. Comparitech researchers gathered listings for stolen credit cards, PayPal accounts, and other illicit goods and services on 13 dark web marketplaces.
Continuing to use Paysafecard as my example, not every online store accepts it (though to be fair, most do). They’re similar to prepaid debit cards but usually have some secondary purpose. For comparison, if you buy the same pair of jeans with your credit card, only the company or a potential hacker could see the transaction records. My favorite virtual card service (and password manager), 1Password, lets you create a virtual payment card and then store it for future use.
Smarter Access, Better Protected Data, Faster Audits: Enhancing Your Insider Threat Defense
This lets them quickly cash out funds from compromised accounts. 1 Next, we’ll look at how this sensitive data ends up for sale online. • The U.S. has the highest volume of available card details • Stolen card data prices ranged from $17 to $120 in 2022 • Nearly 50% of these numbers came from U.S.-issued cards

Google Pay generates a virtual account number for your card and uses transaction tokens for each purchase. But, like PayPal, Cash App requires a lot of personal information when creating an account, including an email address, phone number, and full name. Whenever you buy something or send someone money, they can only see this alias (not your email or banking details). You need to give PayPal a lot of personal information when you create your account, including your email, phone number, and even a government ID.
ELI5: How Do Hackers Get Their Money When Money Has To Be Transferred To A Real Bank Account?
Addresses and transactions are inherently connected in the Bitcoin blockchain, making it relatively easy to extract private information. Services like Protonmail and Tutanota were created to preserve your privacy and security; therefore, you should consider adopting such tools. As computer scientist Nick Szabo defined them, such “trusted third parties are security holes” that should be removed for more privacy and security by running your own node. Random public nodes verify your Bitcoin transactions if you don’t run your own node. Running your own node protects your Bitcoin wallet from disclosing information about your transactions. While TOR encrypts and makes your online traffic private through a decentralized network, VPN encrypts and routes your connection using a network of servers maintained by a centralized entity.
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The system is designed to provide enhanced security and privacy features. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
Wasabi Wallet
In the real world you can just use cash or check. Otherwise they're useless for online purchases now, and why else would you need them? Not only is your online identity at risk, but your physical self is also challenged.

Best Minecraft Survival Servers You Should Check Out
They sell these details on dark web marketplaces. Fraudsters use card skimmers at gas stations to steal info. 11 North America faces the biggest threat, with 42% of global e-commerce fraud value. E-commerce transactions carry serious risks. This helps stop fraud before it starts. They alert banks and users right away.
Top 5 Data Removal Services Of 2025
However, limited-use prepaid cards don’t have to be tied to any particular account or identity. It’s no surprise, then, that the global market for transactions involving prepaid cards reached $3.65 trillion in 2023. Most marketplace sellers say that these cards are 100 percent safe to use because they function just like any other kind of gift card that you might use in a store. Using specific payment methods to receive your funds is still necessary to maintain complete privacy, as sending directly from your KYC’d bank account obviously leaves a transaction trail.
Stolen Credit Cards Handed Out For Free On Dark Web Forum
These illegal transactions pose big risks. Criminals steal card info and sell it on hidden websites. This black market thrives on anonymity and cryptocurrency payments. Buyers pay $10 to $120 per card, based on the card’s limit and type. They package this data into “dumps” for sale. 3 Hackers then sell the stolen numbers on hidden sites.
Fortunately, you can use virtual pay cards to mask existing credit cards you use online without needing to install a new app or apply for a new service. Prepaid gift cards are fully anonymous and can be bought at a store and used online. For every E-Wallet on this list, you’ll need to link a bank account or a valid debit/credit card to make payments. The most notable of the lot has been All World Cards, which emerged on the scene in May 2021 and has since drummed up attention by leaking data for one million credit cards plundered between 2018 and 2019 on a cybercrime forum for free, with most cards from the State Bank of India, Banco Santander, and Sutton Bank.
Detecting unwanted transactions is key to protecting your finances. This extra layer of security gives peace of mind in today’s digital world. They show recent purchases, account balances, and spending trends all in one place. 1 This quick notice helps spot fraud fast, before major damage occurs. These tools scan transactions in real-time, flagging any suspicious charges instantly. These alerts can spot fraud fast and keep your money safe.
Most virtual card services impose fewer costs than prepaid cards. Virtual cards have standard credentials (from popular brands like Mastercard® or Visa®) and are accepted by most merchants, even for recurring payments. The virtual card acts as a layer of protection between your actual account information and the merchant, providing an extra level of security. They stand in as a decoy card between a merchant and your funding source, masking your real payment data in the process.