Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Last but not least, we here at Pixel Privacy never condone illegal activity.
What Is Tails Software Used For?

I recommend using a stick since DVDs have a read-only function after you’re done burning well and accessing the dark web required a bit of writing. It’s like in those movies where the doctors are experimenting on deadly viral strains from behind the safety of a glass enclosure. It knows you’re accessing Tor but can’t see beyond that. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny.
- Since these pages would otherwise be behind paywalls, it stands to reason that this would go against copyright laws.
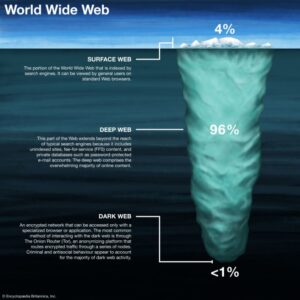
- The dark web is a hidden part of the Internet that the majority of Internet users do not think about or engage with, with the standard activities happening there varying greatly from that of the mainstream Internet.
- The editor will then create a link for you to forward to the sender.
- His phone allegedly contained sexually explicit images exchanged on the app, according to court filings related to his arrest last July.
- As described in public documents, this case was a part of a path-marking global investigation that targeted thousands of users of more than 200 websites operating on the Tor network and dedicated to the trade of child pornography.
- It is a good way to prevent third parties from tracking online activities.
Marketplaces
In fact, there are growing concerns about law enforcement monitoring what is happening on the dark web. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites.

"You went on the dark web, thinking that your actions were anonymous, but they weren't, and we found you," Fort said of the site's users at a press conference. The site's operator, the 23-year-old Jong Woo Son from South Korea, was also charged with nine counts related to the operation of the site. Following the take-down of the site in March 2018, authorities concentrated on uncovering the identities of site users. "Teens on the other hand present risk-taking behaviours, such as self-harm or having multiple sexual partners, academic decline, isolation and difficulty forming healthy relationships.”
What Services And Tools Are Available On The Dark Web?
They also searched seven buildings in connection with the porn ring in mid-April in Germany. Frankfurt prosecutors said in a statement together with the Federal Criminal Police Office that in mid-April three German suspects, said to be the administrators of the "Boystown" platform, were arrested along with a German user. In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses.
Install The Tor Browser
The US Navy’s main reason for creating Tor was to help informants relay information safely over the internet. This .onion link makes it impossible for hackers to impersonate your profile. This .onion site is a bit different from the others reviewed above.
Should I Only Use A VPN To Access The Dark Web?

These categories include email providers, news sites, privacy, and commercial services. These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers. Onion sites are far safer to use as they are hidden deep within the deep web.
Discovering that your personal data is circulating on the dark web is akin to a personal violation. The Tor browser offers strong online protection, given that it routes your online traffic via severa… If you’ve ever worked from a coffee shop and accessed your company’s server, or if two b… After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. It hosted over 7,000 .onion categorized links to make surfing the web easier.
Verified Social Channels And News Sites

The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations. Think of it as the internet’s wild card. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web.
The sites are simple in their appearance, mainly due to the limited technical capabilities of individuals and the community. The maintaining of a publicly advertised list is discouraged and when identified, the .onion address is quickly changed in order to prevent LEAs from becoming aware of its existence. In general, technology companies still believe that the darknet has merits, and that it supports political and religious freedoms. More recently, Europol still identifies the darknet as a criminal threat.
These markets have no protection for its users and can be closed down at any time by authorities. Silk Road was one of the first dark web marketplaces that emerged in 2011 and has allowed for the trading of illegal drugs, weapons and identity fraud resources. Tor browsers create encrypted entry points and pathways for the user, allowing their dark web searches and actions to be anonymous.
Minimize Or Rescale Your Tor Browsing Window
They also reflect an aggressive and coordinated global effort by law enforcement, in partnership with the National Center for Missing & Exploited Children, to crack down on offenders and rescue helpless victims. Also in May, FBI task forces arrested more than 200 people and rescued 115 children during a five-day nationwide operation targeting people accused of child exploitation. The prosecution is among a staggering number of child exploitation cases brought nationwide over the past year, including a seemingly endless stream in Massachusetts charging teachers, doctors, police officers, and public officials. He is awaiting trial in federal court in Boston on charges of possession and distribution of child pornography and has pleaded not guilty.

You will find all the necessary .onion links to access any content or service on the dark web. Unlike other search engines, it does not collect or share web activities and personal data of users. Thankfully, some useful sites can help you circumnavigate the dark web landscape as you search for the best content. Though people usually think of dark websites as the wrong online place, that’s not the complete truth.
That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. While some studies have claimed that illegal Bitcoin activity is as high as 44%.
DULUTH — A Bemidji man has been found guilty of advertising, distributing and possessing material depicting the sexual abuse of children using a site on the dark web. “We are preparing ourselves for it because we know it is coming,” said Milka, noting that a former middle school teacher in Louisville, Ky., was recently sentenced to 19 years in prison for distributing AI-generated sexually explicit images of children. Those reports involve cases in which “bad actors” use AI to create nude images from photographs of fully clothed children, according to Hayley Elizondo, program manager of the tipline’s public reports.
Enter A Darknet Web Address
Being in the wake of the sexual revolution, the climate toward adults having sexual relationships with minors in the 1970s and early 1980s was more open than it is now, but even then sexual attraction to underaged children was generally viewed as atypical. With it, the Internet changed nature from a publishing medium to a participatory medium; a place where users can communicate, interact, and create user-generated content in budding virtual communities. In October 2019, when authorities publicly announced the international investigation, US prosecutors indicted Son on nine charges, including conspiracy to post child pornography. Son downloaded videos of child sexual exploitation from child sexual abuse material distribution site AVSNOO and re-uploaded them to his own server. As a result, law enforcement has employed many other tactics in order to identify and arrest those engaging in illegal activity on the dark web. There are several websites which analyze and monitor the deep web and dark web for threat intelligence.