Accused of helping oversee one of the largest collections of child pornography on the dark web, McIntosh, 65, pleaded guilty to two federal felony charges in August. "To exploit children as long and deeply and aggressively as possible." Some countries lack comprehensive cybercrime laws, complicating international efforts to combat dark web activities. These changes aim to provide clearer guidelines for prosecuting cybercriminals and deterring illegal activities.
Work With A Competent Internet Sex Crimes Criminal Defense Attorney
Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. Your data is encrypted in the Tor browser before reaching the ZeroBin servers. ZeroBin is a wonderful way to share the content you get from dark web resources. Blockchain even has an HTTPS security certificate for even better protection.
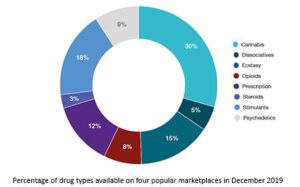
Those caught facilitating or participating in illicit transactions, such as drug trafficking or the sale of illegal firearms, face stringent federal charges. This initiative aims to harmonize laws across countries, facilitating prosecutions and international cooperation. The UN Office on Drugs and Crime (UNODC) is working to develop an international legal framework to address cybercrime, including activities on the dark web. The GDPR imposes strict requirements on data controllers and processors, with substantial fines for non-compliance. In the European Union, the General Data Protection Regulation (GDPR) has influenced how personal data is handled, including on the dark web. Several countries have introduced regulatory measures and legal reforms to address the dark web’s challenges.
- A Sudbury man who sexually abused his daughter and who had been accessing child pornography on his cellphones will be sentenced later this spring.
- The UN Office on Drugs and Crime (UNODC) is working to develop an international legal framework to address cybercrime, including activities on the dark web.
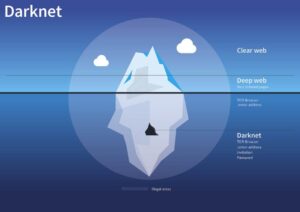
- Check out these best onion sites to access the dark web securely and anonymously.
- According to law enforcement, when requests are made to the company, Snap often replies that it has no additional information.
- Other sites explicitly block search engines from identifying them.
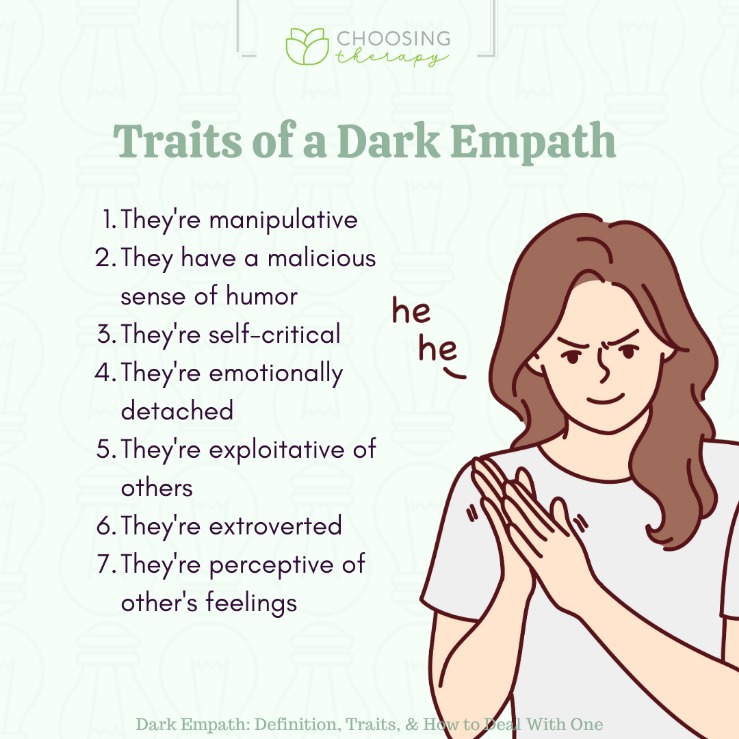
- These perpetrators use psychological manipulation to weaken their victims, gradually pulling them from one stage to the next.
Police Backlash
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. This means your activities cannot be traced or your browser history exposed. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
Dark Web Child Pornography Facilitator Sentenced To 27 Years In Prison For Conspiracy To Advertise Child Pornography
“It isn’t pretty, it isn’t fun, and it isn’t right,” he said, but it doesn’t require the abuse of actual children. He said McIntosh mostly oversaw the site’s fantasy and roleplay rooms, where “sick people engage in a game” of pretend sexual abuse. He added that agents who raided the men’s homes found tens of thousands of images of child pornography in some.
Which Wallet Best For Darknet Market
In addition, it ensures that no record of communication is stored. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. However, note that the site only uses non-sensitive and public data for the metrics. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. For example, the BBC website is not accessible in such countries.
Types Of Dark Web Websites
Congress has regularly allocated about half of the $60 million in yearly funding for state and local law enforcement efforts. The federal government has also not lived up to the law’s funding goals, severely crippling efforts to stamp out the activity. The law Congress passed in 2008 foresaw many of today’s problems, but The Times found that the federal government had not fulfilled major aspects of the legislation. All the while, criminals continue to trade and stockpile caches of the material. And when tech companies cooperate fully, encryption and anonymization can create digital hiding places for perpetrators. In interviews, executives with some companies pointed to the voluntary monitoring and the spike in reports as indications of their commitment to addressing the problem.
The Justice Department’s coordinator for child exploitation prevention, Ms. Harris, said she could not explain the poor record. Senator Richard Blumenthal, a Democrat of Connecticut who was a sponsor of the law’s reauthorization, said there was “no adequate or logical explanation and no excuse” for why more money was not allocated. Facebook has long known about abusive images on its platforms, including a video of a man sexually assaulting a 6-year-old that went viral last year on Messenger. A Snap spokesman said the company preserved data in compliance with the law.
Michigan THC Limits: Legal Consequences And Enforcement
McIntosh later confirmed to authorities that this was a reference to 13-year-old Abigail Williams and 14-year-old Liberty German, two children murdered in 2017 by a man in Indiana. He encouraged users to craft stories with characters “like adult men prone to violence” and centering around girls named Libby and Abby. Under the right circumstances, he added, he would entertain those that feature children as young as 7. Though his codefendants didn't disclose prior instances of abuse, the attorney called it "wildly unlikely" that their involvement in the website was their "first rodeo." Though Schiller suggested that McIntosh's history of abuse made him the worst of the site's four leaders, Serafini disagreed.

Hidden Answers
The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users). MacOS users will need to drag and drop the Tor Browser icon to the Applications folder. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. Instead, you need to get the Tor browser to access the dark web.
In a study conducted by Michael Seto in 2010, 33–50% of a sample of child pornography offenders reported having sexual interest in children. Digital cameras and Internet distribution facilitated by the use of credit cards and the ease of transferring images across national borders has made it easier than ever before for users of child pornography to obtain the photographs and videos. Legal professionals and academics have criticized the use of child pornography laws with mandatory punishments against teenagers over the age of consent for sex offenses. The University of New Hampshire's Crimes Against Children Research Center estimates that 7 percent of people arrested on suspicion of child pornography production in 2009 were teenagers who shared images with peers consensually. In 44% of cases, the most serious images depicted nudity or erotic posing, in 7% they depicted sexual activity between children, in 7% they depicted non-penetrative sexual activity between adults and children, in 37% they depicted penetrative sexual activity between adults and children, and in 5% they depicted sadism or bestiality.
If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. They know how to process the information and get it to the correct law enforcement agencies internationally. Note that engaging with the content in any way is not only distressing but could also put you at legal risk. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark web sites offer malware as a tool for cyberattacks. Accessing blocked content can result in being placed on a watch list or imprisonment.
The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web. With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity. The platform is free and is run by volunteers in the US who prefer privacy and security. It does not store logs and is protected from interference and malicious attacks.
“This complex, global investigation, lengthy and successful extradition, and substantial jail sentence are proof of the Department’s steadfast and unwavering commitment to identifying and bringing to justice criminals who hide behind anonymous networks to abuse and exploit the world’s children.” According to court documents, between July 24, 2008 and July 29, 2013, Marques operated a free anonymous hosting service located on the dark web, an area of the internet that is only accessible by means of special software, allowing users and website operators to remain anonymous or untraceable. In one joint raid by German and Dutch authorities, they seized a hard drive containing a staggering 72,000 videos of child sexual abuse.