Compromised credential monitoring tracks ongoing threats to your organization. This one-time scan shows current exposure, but continuous monitoring is recommended since new breaches happen daily. Enter your email address or domain name to search criminal marketplaces, hacker forums, and breach databases for your exposed credentials.
OnionSearch
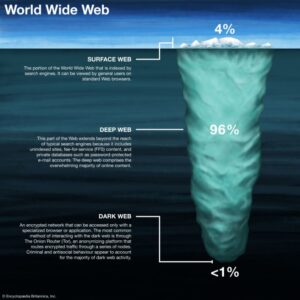
At the same time, platforms that don’t censor posts expose users to raw contents & sometimes allow people to access illegal or content they don’t want. Some search engines are focused on a specific, ultra-niche use case. In comparison to just a few search engines on the surface world, such as Google, the dark web utilizes many smaller search engines but no spectacularly dominating players.
Browse Privately And More Securely
Tor Taxi is one site offering verified links and real-time uptime monitoring to help users navigate safely. However, proxied Tor sites—those that use TOR2WEB services to make dark web content accessible through standard browsers—are regularly indexed on Google. We will refer to the darknet as the network infrastructure, such as the TOR network or I2P network, and dark web as the content aspect that is accessed and viewed by users.
- The platform’s no-log policy ensures your searches aren’t stored or tracked, and its simple interface mirrors Google’s clean results layout.
- To help you act quickly, Keeper also makes it easy to update weak or compromised credentials using its built-in password generator, which creates strong, unique passwords in just a few clicks.
- There have also been technical deanonymization successes for instance, a few years ago, researchers aided police in Germany to identify users by correlating Tor traffic timing.
- The best dark web search engines in 2025 try to reduce this risk by filtering harmful results.
Hidden Wiki, TorLaND & similar engines offer both a standard search site and a curated directory or community discussion forum. They don’t even track the users nor do they log the queries they searched on the engines. Search engines that open on the darknet, such as DuckDuckGo’s .onion variant, don’t play with their users and always make sure they keep them anonymous & protect their privacy. New and novice users to the dark web should engage with sites such as Ahmia, wherein advanced to extreme knowledge users may favor uncensored indexes. Without these tools, discovering applicable information in a world with no acknowledged pathosystem would be about as efficient as finding a book in a library with no catalog.
When you Input your email or phone number, the site will sweep through known breached sites to determine if your data was compromised. Identity Guard not only monitors your data, but it also alerts you when there’s a change in your credit report. It searches through 6 categories of data to assess any vulnerabilities. Everything from phishing email scams to data breaches to malware on your computer can expose your personal information—credit card numbers, CVV codes, or social security numbers—to hackers.
Reddit users report that their attempts to use the service typically result in no search results — likely due to backend failures — marking it effectively defunct. Sites with a warning indicate that it hasn’t yet been verified, while sites flagged as risky are known to contain potentially harmful or dangerous content. Search results are labeled as Verified, Warning, or Risky, making it especially useful for less experienced dark web users who want to steer clear of unsafe sites. Accessible on both the clearnet and through a .onion address for Tor users, VormWeb combines manual curation with automated crawling to ensure a balance between quality control and broad coverage.
What Kind Of Information Can I Find On Dark Web Search Engines?
- Without a search engine built for this environment, it is almost impossible to find working links.
- Dark web monitoring tools are indispensable in identifying threats early, detecting breaches, and safeguarding sensitive data.
- The investigation begins by entering the keyword or other operator in the search bar.
- Some sites might use these details for advertising, analytics, or tracking your online preferences.
- A trustworthy platform will avoid storing your personal information or tracking your search history.
- Bookmark frequently visited services for quicker access in the future.
Let’s say you get an alert that someone on a forum is offering access to Your Company network starting bid 5 BTC. Many vendors include access to their intelligence analysts for clarification or takedowns. They might operate sock puppet accounts on closed forums, have access to invite only groups, or buy data from brokers to include in their feeds.
Is DuckDuckGo An Actual Dark Web Search Engine?
When engaging with dark web forums or contacts, tools like ProtonMail (Tor-accessible) and Signal Messenger can ensure safe communication. As a result, the dark web has become a breeding ground for illicit activities because government agencies face significant challenges in identifying the operators behind hidden services. These sites are intentionally hidden to protect the privacy and anonymity of both the site operators and visitors. The dark web consists of websites that use encrypted .onion domains, which require specific software and protocols to access. The dark web is a hidden part of the internet that requires specialized software to access. Haystack is a dark web search engine designed with privacy in mind, similar to Duck Duck Go.
Best 9 Dark Web Monitoring Tools
Privacy advocates like the ACLU argue that using malware this way can overstep warrants and endanger internet security if the exploits leak. In fact, many dark web busts happen because the perpetrators slipped up on their operational security OPSEC, not because of some magical decryption of Tor. This onion-like routing makes tracing users or site hosts incredibly difficult. Websites on the dark web have masked IP addresses and use encryption to keep their operators and visitors anonymous. We’ll also discuss the legal tightrope that agencies walk when hacking into hidden services, and why international teamwork is the secret sauce behind many takedowns.

How Do I Safely Access NotEvil Dark Web Search Engine Without Risks?
However, the sites on the Deep Web aren’t indexed by search engines. This is a collection of websites that can all be accessed through a search engine. To this, you can use a good Dark Web monitoring tool to easily investigate the Dark Web and ensure your data is not stolen and uploaded there.
In one case, the Welcome to Video child porn site, investigators traced bitcoin payments from hundreds of users and got their names from exchanges, leading to multiple arrests worldwide. In short, police can’t decrypt Tor traffic at will, but through network level surveillance or browser exploits, they have occasionally unmasked users. One method is operating or monitoring enough Tor relays to perform a traffic correlation attack matching the timing of someone’s entry and exit traffic. However, they have identified Tor users by attacking the network in specific ways. There have also been technical deanonymization successes for instance, a few years ago, researchers aided police in Germany to identify users by correlating Tor traffic timing.
Ahmia and Not Evil are also likely popular among security-conscious users. Unfortunately, specific usage statistics for each Tor search engine are not readily available due to the privacy-focused nature of Tor. At the time of writing, Not Evil, one of the top ranked search engine’s was not online. Have I Been Pwned” (HIBP) is a widely recognized online service and database created by security expert Troy Hunt. ShadowDragon offers a robust suite of investigative tools tailored to streamline the complexities of modern investigations.
DarkSearch is a deep search engine that prioritizes user privacy by indexing .onion websites. WormWeb is a user-friendly search engine built specifically for the dark web, providing quick and easy access to .onion websites. These search engines catalog .onion domains, which are not easily accessible from regular web browsers. Hackers, journalists, and security companies use this hidden corner to exchange information and gather intelligence that’s not accessible through the regular internet. Dark Web search engines are powerful tools — when used responsibly.


CrowdStrike Falcon Intelligence is a research service that scours Dark Web sources for mentions of your company’s assets. The DarkOwl system is a mid-market option because it provides results for its customers rather than expecting them to perform searches themselves. Companies subscribing to DarkOwl will also need threat protection and data loss protection software to fully protect their systems. Darkint Suite’s data feeds can be integrated into applications through an API. Another element in this suite is Darkint Score, which is a vulnerability assessment of the client company’s exposure to Dark Web data loss. This information is constantly updated by repeated scans and those disclosures are made available in the dashboard for those subscribing companies to which the data pertains.
Each search result is only given as a direct link to the respective site. However, there are a few countries that have banned access to BBC’s official homepage on the Web. BBC is a reliable news source with one of the largest collections of news events and stories from several decades past. Actually, here are more Dark Web sites that Google won’t let you find.