While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. As a result, you cannot find them with a regular search engine.
Pro Tip: Use A VPN To Stay Safe When Using The Dark Web Search Engines
However, third parties such as the government and your internet service provider (ISP) can see that you are using Tor. It will encrypt your traffic and data so no one can intercept it. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
Can I Get In Trouble For Using The Deep Web?
Cryptocurrency miners and other malicious software often target dark web users. This isolates any potential malware and prevents cross-contamination with your personal data. Avoid entering any real personal details or using existing accounts on dark web sites. I always cross-reference links from multiple verified sources before visiting any dark web address. Always run the latest version of the Tor Browser to protect against security vulnerabilities.
Citizens of such countries can use the dark web to bypass firewalls and access global information. Some users, such as whistleblowers or journalists working on sensitive issues in oppressive authoritarian governments, need privacy to carry out their activities. Later released as open-source, it became widely accessible for privacy-focused use. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously.
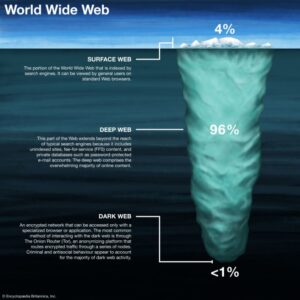
What Are The Deep Web, The Dark Web, And The Invisible Web?
To better understand how the dark and the deep web work, you must first understand how the open web operates. Moreover, given the nefarious nature of the dark web, some government agencies may set up Tor gateways to monitor what’s happening on the dark web. We also recommend using a virtual private network (VPN) such as NordVPN — the best dark web VPN — to add an extra layer of protection. Dark web encryption allows website owners and users to stay completely anonymous during their engagement. We’ll also shed light on some of the legal uses of the dark web and show you how to access it securely in a detailed step-by-step guide. All our content is written fully by humans; we do not publish AI writing.
Step 4: Use Dark Web Search Engines
It’s my first stop when orienting myself in Tor, especially for quick access to trusted services like secure email or news sites. I bookmark its .onion link for quick access but pair it with Ahmia or DeepSearch for safer, cleaner searches. In 2012, I was researching internet privacy and ventured into the Tor network. The dark web presents various threats, including malicious software and computer viruses, posing risks to users' systems and data security. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.
Dark Web Reveals Tech Companies Leak Most User Data
Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. This way, you can protect yourself from websites that want to steal your login details or cryptocurrency. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Other options include Ahmia and NotEvil, which focus on listing .onion links.
Deep Web Radio

Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. Simply accessing the dark web and using the Tor browser may already raise government suspicion. As enticing as it might be, don’t follow links to other parts of the dark web. Check around with other users and ask if they know anything about the new marketplace.

And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. Great life advice, but it’s even more valuable where the darknet is concerned. That’s why it’s never a good idea to burn Tails on DVD. Just click on the onion icon and choose Security Settings. Tor has an in-build slider which lets you adjust the level of security. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
- You could consider the clear or surface web the "top" and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox.
- Your team should absolutely be monitoring the dark web, but this doesn’t mean they need to be searching it themselves.
- As a result, you cannot find them with a regular search engine.
- If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node.
What Is The Dark Web? Here's Everything To Know Before You Access It
Search results are labeled as Verified, Warning, or Risky, making it especially useful for less experienced dark web users who want to steer clear of unsafe sites. Accessible on both the clearnet and through a .onion address for Tor users, VormWeb combines manual curation with automated crawling to ensure a balance between quality control and broad coverage. It is a fast-growing search engine and reports a monthly growth rate of 20% (as of October 2025).
- The dark web, however, requires special software to access, as explained below.
- We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal.
- You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
- NotEvil could evolve its filtering to include trust scores, leveraging community reports and AI to flag phishing or malware-laden sites.
- Ahmia’s defining feature is its commitment to filtering out illegal content, such as child abuse material, a rare stance in the dark web’s murky landscape.
FAQs On The Best Dark Web Search Engines
It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. A virtual private network (VPN) is a good way to mask Tor activities.
Sites on the dark web use .onion domains, which are only accessible via the Tor browser. While traditional security tools focus on known threats, some of the biggest risks, like data breaches, identity theft, and corporate espionage, often start out on the dark web. However, business leaders and security professionals can no longer afford to ignore this part of the internet. Tails enhances security, but Tor Browser with a VPN is sufficient for most privacy-conscious users.
Activists and whistleblowers prefer the dark web for accessing or selling private information or documents. Some people or organizations even use the dark web as a tool to protect their data. Some of the raison d’être of the dark web is to provide privacy and anonymity, making it a valuable tool for people whose access to information is restricted. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges.
This is where all the cat videos and trending YouTube songs live, easy to find and access. When you search for something on Google or Bing, you’re using the clear web. Remember, the Tor browser connects to the internet differently than regular browsers in an attempt to increase your anonymity online.