It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace. Like other marketplaces, ASAP Market also requires you to register for an account. It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoin to keep you anonymous on this marketplace. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea of the vendors for the buyers and vice versa.
Third-party Risk
You’ll get stolen credit cards, remote desktop account info, personal details, and various logs. Everything is in English, but users from around the world are welcome. That way, they aim to create secure forums and limit outsiders like law enforcement. Also, set up two-factor authentication (2FA) to add an extra layer of protection in case someone manages to figure out your password. In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer.
- While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities.
- FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels.
- The most recent example is the shutdown of the oldest marketplace Hydra Market in 2022 which took a combined effort of the FBI and the German authorities.
- These tools enable a rapidly growing cohort of organizations around the world to safely embrace cryptocurrency-related transactions, products, and partnerships.
- One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it.
- As per MoneyZine, Blacksprut is the largest marketplace on the platform, with 28% of the market share.
These markets use cryptocurrencies and encryption to hide, but law enforcement’s growing technical skills have repeatedly broken them open. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious.
- The dark web is famous when it comes to hosting as well as spreading explicit and illegal content.
- The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others.
- Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums.
- There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks.
- Visiting the Dark Web isn’t illegal in itself, but it is illegal to engage in illicit activity while using it.
This includes domains, stolen credentials, leaked configurations, and shadow assets. While both are used for illicit activity, the differences are significant. If attackers circulate your credentials or data, compromise may already be underway. Threat actors use these platforms to buy or sell assets originating from corporate environments. Vendors and buyers must constantly evolve their methods to avoid deanonymization.
Popular Posts
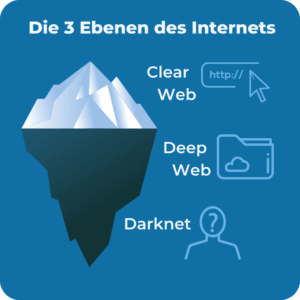
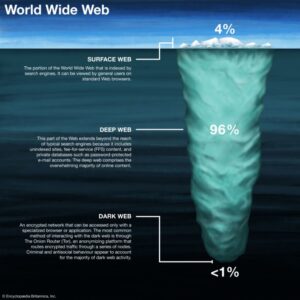
You can access most deep web content through regular browsers with proper credentials. The deep web includes all content not indexed by search engines, like password-protected sites and private databases. You can access it for legitimate purposes like whistleblowing and freedom of expression. You can only reach it through specific configurations and authorization, making it separate from the regular internet. Businesses operating in such regions may need to adapt to the technical challenges and risks posed by using darknets for legitimate purposes. Businesses should be aware of the potential for data leaks and invest in data loss prevention measures.
Frequently Asked Questions (FAQs) About Dark Web Marketplaces

To expand their reach, some marketplaces established parallel channels on Telegram. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action. Here are some of the now-defunct dark web markets that were notorious for cybercrime. users comments were generally critical of the legitimacy of the marketplace, with comical references like “Welcome to the FBI HQ” posts.|Dark markets are online platforms on the darknet where illegal goods and services are traded. Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. These marketplaces facilitate the exchange of everything from stolen credentials and drugs to weapons and hacking tools.|Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities. Emphasizing anonymity, darknets and dark markets operate on a technical level that significantly differs from the conventional surface web. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors. The anonymity and encryption provided in dark markets create a haven for cybercriminals and nation-state actors to buy and sell dangerous assets while evading detection.|What’s the difference between classic marketplaces and data stores? The illicit marketplace for stolen data reached a staggering $2 billion in 2024, with over 1.4 billion data records breached in just the first half of 2025. Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. In 2025, it hosts over 2.5 million active users daily, with markets facilitating billions in cryptocurrency transactions annually. On top of that, undercover operations are a key strategy that's being used, with agents posing as buyers or sellers to infiltrate these markets.}
Following AlphaBay shutdown, Hydra emerged as the dominant market exhibiting the strongest observed dominance to date8,9,10. Then, by the end of 2015, AlphaBay became the dominant market until its takedown by operation Bayonet34. After Silk Road shutdown, there was a transition period when no market was dominant. Therefore, there is small fraction of actors responsible for moving most of the trading volume in both directions, i.e., buying and selling.
Additionally, ransomware and malware tools show strong demand, with 1,000 malware installs offered for USD 1,800. As of 2025, daily traffic surpassed 3 million, with approximately 60 percent of domains hosting illicit content. In 2023, it averaged 2.5 million daily visitors, rising to 2.7 million by April 2023. It’s a place where illegal activities such as selling credit card numbers, bank login details, weapons, hacked social media accounts, and drugs take place. He specializes in digital marketing, SEO,…… Rohan Jambhale is a senior editor at Smartphone Thoughts.
Such launches were not always a success; in February 2014 Utopia, the highly anticipated market based on Black Market Reloaded, opened only to shut down eight days later following rapid actions by Dutch law enforcement. The shutdown was described by news site DeepDotWeb as "the best advertising the dark net markets could have hoped for" following the proliferation of competing sites this caused, and The Guardian predicted others would take over the market that Silk Road previously dominated. The first marketplace to use both Tor and Bitcoin escrow was Silk Road, founded by Ross Ulbricht under pseudonym "Dread Pirate Roberts" in February 2011. It has been considered a "proto-Silk Road" but the use of payment services such as PayPal and Western Union allowed law enforcement to trace payments and it was subsequently shut down by the FBI in 2012.

Search Code, Repositories, Users, Issues, Pull Requests
Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. Regardless of your jurisdiction, activities such as trading stolen financial data, compromised accounts, or money laundering services are illegal. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
The Future Of Cybersecurity Leadership: AI, Governance & Education Kevin Powers, Boston College
The dark web is a portion of the internet accessible only via special anonymity-preserving networks like Tor. As cybercriminal marketplaces grow more organized and automated, organizations face escalating exposure — often without their knowledge — until it’s too late. As dark web marketplaces evolve, so too do the sophistication and automation of the threats sold and traded.
Ransomware Groups

For example, you can join a chess club or BlackBook, a social network described as the “the Facebook of Tor.” Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Start by downloading the Tor browser, which is necessary to access dark web sites. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. The dark web is a part of the internet that isn’t indexed by search engines.
Discover Content
Many operators have since moved to accepting only Monero (XMR), a privacy coin with features designed to boost anonymity and reduce traceability. The FBI tied Taiwanese national Rui-Siang Lin, Incognito’s operator, to the DNM’s website by tracing crypto transfers to an exchange account in Lin’s name. Besides Hydra operators, other DNM administrators faced criminal prosecution in 2024. The court also sentenced fifteen accomplices to anywhere from eight to 23 years in maximum-security penal colonies. Last December, a Russian court imposed a life sentence on Stanislav Moiseyev, Hydra Market’s suspected founder and operator, although the Moscow prosecutor’s office did not publicly tie the guilty verdict to Hydra. While these outfits are not traditional DNMs, their success highlights how drug vendors are scaling their operations throughout Russian-speaking countries.
Currently there are 12 actives listings, and the below screenshot shows 3 financial counterfeit products. The counterfeiting category on Dark Empire Market primarily advertises counterfeit financial products. Counterfeit goods are products that are made to imitate genuine items with the intention of deceiving others.
Torrez Market
We find that multisellers have the largest median income throughout the period of observation—except in the last quarter of 2017 and 2018, when they have the second largest median income. To study the performance of sellers, we analyse the quarterly median income, i.e., the quarterly median of the money received by each seller, for each category and multisellers, as shown in Fig. Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. On the other hand, the number of U2U-only buyers is less affected. The U2U-only category is comparatively small, representing only 6% of all buyers on average. The results for buyers are different, as shown in Fig.
Therefore, key actors in the ecosystem of DWMs may play important roles in broader criminal networks. For example, in some cases, a seller in a given market may behave as a buyer in a second market or in the U2U network. Third, at any given moment we classify entities as either buyers or sellers. Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. These different regimes suggest that the ecosystem’s resilience is mainly supported by the high demand of buyers rather than the response of the sellers.
Later that month, the long-lived Outlaw market closed down citing a major bitcoin cryptocurrency wallet theft; however, speculation remained that it was an exit scam. In May 2017, the Bloomsfield Market closed after investigations in Slovakia inadvertently led to the arrests of its operators. Further market diversification occurred in 2015, as did further developments around escrow and decentralization. Not long after those events, in December 2013, it ceased operation after two Florida men stole $6 million worth of users' Bitcoins.