While a website can’t identify you or an ISP can’t decrypt your internet traffic; still, they can still see you using Tor, which can draw some unwanted attention and raise suspicions. It is highly advisable to take all the necessary security measures discussed in this article to protect yourself. You can access the dark web using your Android device by following a few steps. Remember that any website engaging in illegal activities such as drug trafficking, weapons sales, hacking, and human trafficking violates international laws and, therefore, is illegal. Although browsing the dark web is not illegal, it contains unsavory activities that can expose you to danger. However, criminals and malicious hackers also use the dark web to hide their illegal activities.

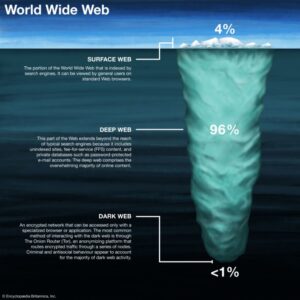
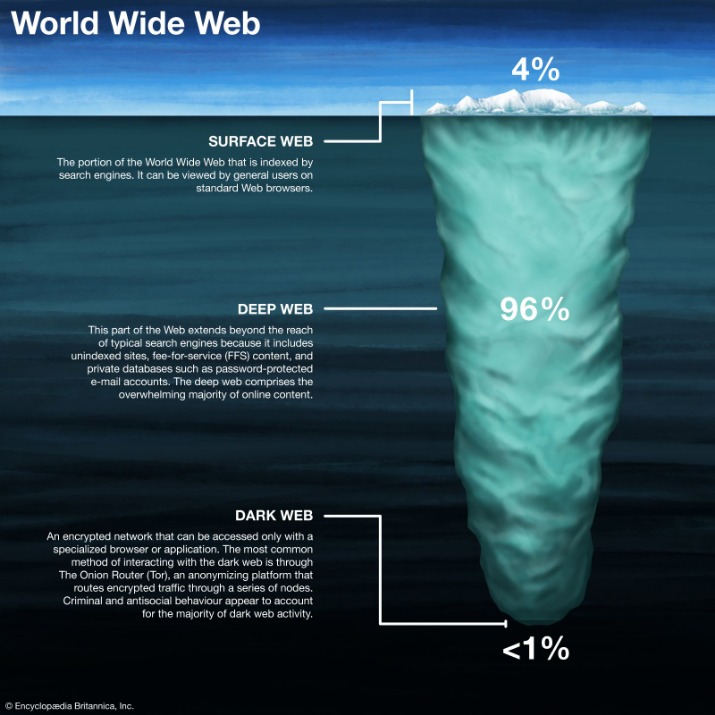
Daniel is a dark web resource that lets you look through lists of around 7000 different .onion sites classified into various useful categories. Most search engines do not work on the dark web, because they are not designed to search for ".onion" URLs. These legitimate people use Tor browser to ensure their safety and to access information that has been censored by the government. The dark web accounts for around 6% of the internet, and it is the secretive portion of the web where drug dealers, black hat hackers, hitmen, and human traffickers sell their wares or services. Due to the value of the private data that is stored on the deep web, it is vital that it is always secured extremely well using encryption. However, it is a huge target for cybercrime because it is the area of the internet where private data resides.
They cater to those seeking anonymity and freedom to explore alternative relationships. While they can offer privacy and security, the risk of scams and dangerous encounters exists. The immutable ledger in the Bitcoin blockchain had considerably aided law enforcement to track the illegal transactions of Silk Road. After all, the immutable ledger in the Bitcoin blockchain had considerably aided law enforcement to track the illegal transactions of Silk Road.
How Do I Find onion Links For Sites?
China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims. While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money.

It’s particularly useful for journalists, whistleblowers, and those who urgently need to send or receive confidential data. ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network. Insights like these help researchers and advocates understand how and why Tor is being used. Tor Metrics highlights that about 22% of daily Tor users come from Russia, while the USA ranks second at 15%.
Media Outlets With A Secret Door
Traditional dating sites often have a broad user base, which can make it difficult to find someone who is a good match. This can be appealing to people who are concerned about their privacy or who want to keep their personal life separate from their online presence. No longer restricted to dial-up, many of us now consider access to a stable high-speed internet connection a critical element of our daily lives.
This just involves turning on your VPN before you open Tor and connect to dark web sites. It’s, ironically, more conspicuous than using popular browsers and sites. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. The dark web, or the darknet, is a small subset of the deep web.
Over the course of their research, DarkOwl analysts observed that romance scams are rarely called ‘romance scams’ directly, but are often advertised and discussed as “catfishing” or “eWhoring”. Per the examples pictured below, DarkOwl analysts discovered multiple Telegram channels where users are seeking advice on romance scams from others in the community. During the course of this research, we generally found that romance scammers typically use pre-built scripts to carry out their schemes.
Encrypted Communication Tools
Simply put, accessing and browsing the dark web is perfectly legal. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The system is designed to provide enhanced security and privacy features. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin.

How To Access The Dark Web Safely: A Step-by-step Guide

Proton further provides access over the Tor network through its customized onion address. Hence, it’s quite useful to be able to connect to its onion link. Speak your mind here without fear, as onion links are immune to censorship. The main advantage is that you can also access other dark web directories without running into malware. You’ll find links to many of the sites we’ve covered in this list.
Protecting Yourself On Darknet Dating Sites
The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. In that spirit, the CIA launched an onion site to help people around the world access its resources securely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored.
Indexes of website links allow Google and other search engines to return relevant results whenever a user types a keyword into the search bar. For additional protection, enterprises should monitor the dark web to identify indicators of dark web compromise, such as database dumps or the posting of personal or financial information. These sites cater to individuals who are looking for relationships and connections outside of the mainstream, often for reasons of privacy, anonymity, or specific interests. However, the darknet is also home to a variety of communities, including those centered around dating and relationships. It is truly important for them to know if their brand name, products, employee/customer data, or confidential documents are being mentioned, even worse sold, in any of these Darknet content. Because these sites are not regulated, there is no guarantee of the authenticity of the profiles or the intentions of the users.
Cyble Strato Cloud Security
Find exclusive products, from rare digital assets to unique services, all while maintaining your anonymity and security. As with any online platform, it’s important to exercise caution and use common sense to ensure a positive and successful dating experience. Darknet dating sites often require users to pay in cryptocurrency, such as Bitcoin, rather than traditional payment methods like credit cards. Once they have accessed the site, they can create a profile, search for other users, and communicate with them.
The Best Dark Web Links (Tested & Working In
- Other sites explicitly block search engines from identifying them.
- The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group.
- When I told Joan (not her real name, to protect her from further scams) what a crook had posted on the internet, there was a long pause, then a deep sigh.
- You can tell you’re on the dark web if you’re accessing websites with .onion addresses on the Tor Browser or a similar anonymity network.
- Users must conduct thorough research and use discretion when engaging in conversations or meetings.
- Gannicus Oliver is an experienced tech journalist (he loves writing on emerging techs and digital privacy issues) and an online business consultant.
They offer a level of privacy and anonymity that traditional online dating sites cannot, making them an attractive option for those who want to keep their dating life off the grid. Because these sites are not indexed by search engines, it is much more difficult for hackers or cybercriminals to gain access to user data. Darknet dating sites are online platforms that allow users to connect with others in a secure and private way.
As an experienced copywriter, I can provide a rephrased version of the following text on "Darknet dating sites" in English. And with the rise of darknet markets, it's easier than ever to find like-minded individuals who share your interests and desires.But how do you navigate the dark web dating scene? However, potential users should weigh the benefits against the risks and take proactive steps to ensure their safety while navigating this obscure corner of the internet. Darknet dating sites present a unique opportunity for individuals to connect in a more anonymous and private setting. Safety varies by site; research extensively, and exercise caution while interacting online. Accessed through specialized software like Tor, these sites often cater to people interested in niche communities or alternative lifestyles.
As with any online platform, education and caution are key to protecting oneself and forming meaningful connections. Hackers and others, then, won’t be able to decipher your password when you log into your online bank account. A VPN hides your IP address from snoops and also encrypts your information while online. Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter a dot onion URL to start browsing. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands.
Knowing this, we tested many dark websites, and only the safest and most reliable ones made it to our list of 29 best dark web sites you should know in 2025. I decided to try to contact some of these 47 people to warn them that their personal information had been posted online and to find out if any of them had ever been victimized by identity fraud. They typically utilize the domain suffix, and onion is reserved for sites wanting to remain anonymous – often created by groups advocating neo-Nazi and white supremacist ideology. When data brokers get hacked, the stolen data can include compromised credit cards, social security numbers, and other data, depending on what was exposed in the breach.
Unlike typical web browsers, Tor Browser uses onion routing, which encrypts and routes traffic through multiple servers around the world to hide your IP address and provide private browsing. This includes firearms, illegal drugs, horrific videos, fake passports, Netflix accounts, credit cards, or even the rental of the hitman. The Darknet Market can be an unregulated market where people can buy just about anythingalmost anything. However, it is important to exercise caution when using these sites and to take steps to protect your privacy. This may include verifying the identity of other users, being cautious about sharing personal information, and reporting any suspicious or inappropriate behavior. This connection methodology enables users to interact with the dark web with minimal risk of their activity being tracked or otherwise exposed.